Avast Unknowingly Bundled Malware With CCleaner For Almost A Month
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
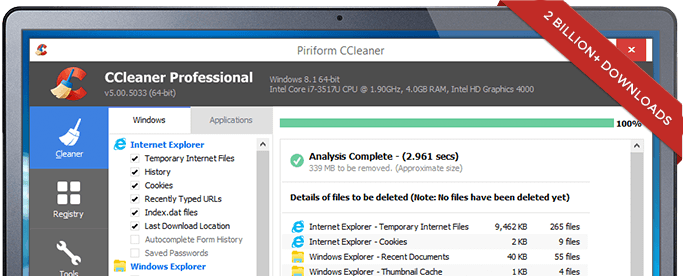
Cisco’s Talos Intelligence security research group found that CCleaner, a popular piece of software that allows users to do routine maintenance on their Windows PCs, has been distributing malware along with its installation file for almost a month. Piriform was the previous owner of CCleaner, but the company has recently been acquired by antivirus maker Avast, which makes the whole situation quite ironic.
CCleaner’s Suspicious Activity
On September 13, Talos was conducting some beta testing for its new exploit detection technology when it noticed that CCleaner 5.33 (the latest version at the time) was being flagged by the new software.
The Talos team further analyzed the CCleaner file, and although the file was correctly signed by the vendor, CCleaner was not the only application being downloaded on users’ systems. The 32-bit binary of CCleaner 5.33 also included a malicious payload with a connection to a hardcoded command and control server.
Article continues belowThe affected version of CCleaner (v5.33) was released on August 15, which gave the malware almost a month to infect CCleaner users. Version 5.34 came out on September 12, the same day the CCleaner devs found the malware themselves, and it didn’t have the malware bundled with it.
Compromised Certificate
It’s unclear whether or not this has anything to do with it, but CCleaner’s “valid” digital certificate with which the infected file was signed was apparently provided by Symantec. Symantec’s certificate issuing infrastructure was recently seen as untrustworthy enough by Google that it got the company to progressively distrust all Symantec’s certificates in Chrome, and forced Symantec to sell its certificate business to DigiCert.
The Talos team believes it may have more to do with an attacker compromising Avast’s development and signing process for the CCleaner application and recommended that this certificate be immediately revoked and untrusted going forward.
Potential Impact
CCleaner had 130 million active users at the time of the Avast acquisition, and it continues to gain millions of users every week. However, there are a few factors that limited the number of infections, one of which is that for users of the free version of CCleaner, updates are not automatic. If they were, we may have seen orders of magnitude more users being infected.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Other factors limiting the potential impact were the fact that the malware was only bundled with the 32-bit version of the software, as well as the malware only activating on Windows accounts with administrator privileges.
Lessons Learned
What we can learn from this situation is that attackers seem to be increasingly targeting developers of popular software as a way to more easily infect millions of users at once. Additionally, if updates are automatic, the damage could be much larger, as we saw with the NotPetya attack.
Automatic updates may still be a net win for users because of how many patches to exploitable bugs could reach users faster than otherwise, but it also means that developers of software with automatic updates should take the security of their update servers that much more seriously.
Talos also showed that anti-exploit technology can be quite useful in situations where antivirus software cannot, as Malwarebytes has also said in the past. Talos added that right now very few antivirus programs can even catch the CCleaner malware: only one antivirus engine out of 64 was able to detect it (ClamAV).
Finally, it’s always a good idea to use a Standard/Limited account on your Windows PC by default, as opposed to using an Administrator account. Previous research has showed that the overwhelming majority of security bugs would be rendered useless if people would use Standard/Limited accounts instead of Administrator accounts by default.
Users of CCleaner 5.33 are urged to immediately update to the latest CCleaner 5.34 version.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
alchap1 FYI, just ran Malwarebytes on my 64-bit machine with CCleaner v5.34.6207 already installed.Reply
Malwarebytes detected Trojan.Nyetya for download of ccsetup533.exe and \Program Files (86)\iolo\System Checkup -
3ogdy On September 13, Talos was conducting some beta testing for its new exploit detection technology when it noticed that CCleaner 5.33 (the latest version at the time) was being flagged by the new software.Reply
The Talos team further analyzed the CCleaner file, and although the file was correctly signed by the vendor, CCleaner was not the only application being downloaded on users’ systems. The 32-bit binary of CCleaner 5.33 also included a malicious payload with a connection to a hardcoded command and control server.
The affected version of CCleaner (v5.33) was released on August 15, which gave the malware almost a month to infect CCleaner users. Version 5.34 came out on September 12, the same day the CCleaner devs found the malware themselves, and it didn’t have the malware bundled with it.
OK, this makes no sense at all. Talos says 5.33 was the latest version at the time, which is September 13th, yet 5.34 had come out a day before? -
ddpruitt Reply20186759 said:OK, this makes no sense at all. Talos says 5.33 was the latest version at the time, which is September 13th, yet 5.34 had come out a day before?
Talos never said that. Tom's once again editorializing without admitting it. The actual writeup states just that they were doing testing on 5.33, not why they were using it. My guess is that since it was beta testing it didn't really matter and they just went with what they had lying around. -
ddpruitt My respect and trust in a company depends on how they handle an incident like this. It's clear that this malware was intended to allow another large scale botnet and that there were several breakdowns in the software development process that allowed this to happen.Reply
Talos makes it pretty clear that there was a serious problem on Piriform's end (how do you build and send something out when the source obviously doesn't match what is in your release branch???). They spell out what happened and what they know and don't know and try to avoid assigning blame.
On the other hand Piriform's statement makes it seem like they figured it out and eliminated the problem and released an update. It's pretty obvious they just got damn lucky the new version doesn't have the malware, probably because it got built on different machine from the affected release. They aren't taking any responsibility for what's a pretty massive breach on there end.
With that type of response I won't ever support the use of Avast or Piriform software in the foreseeable future.