System Encryption: BitLocker And TrueCrypt Compared
Now that Intel offers hardware-based AES acceleration in a number of its mainstream processors, it's time to take a look at two of the most popular system encryption tools, BitLocker and TruCrypt, both of which are able to harness the hardware feature.
BitLocker On Windows 7 Ultimate x64
BitLocker was designed to be a logical volume encryption solution, which means that you deploy it across entire volumes, whether they span multiple drives or only a fraction of one drive. BitLocker requires two NTFS partitions to operate. One has to be the boot partition, which must not be encrypted; the other is for your operating system.
Microsoft's solution is based on 128-bit AES encryption, and it offers several methods of authentication. BitLocker supports a Trusted Platform Module (TPM), TPM with PIN, a passphrase on a USB thumb drive, TPM with USB thumb drive, and a combination of TPM, PIN, and a passkey on a USB drive. Depending on the implementation of each approach, you can trigger different options. For example, simple TPM support will render the system unusable if you install the protected hard drive on a different host PC. Other approaches require active authentication.
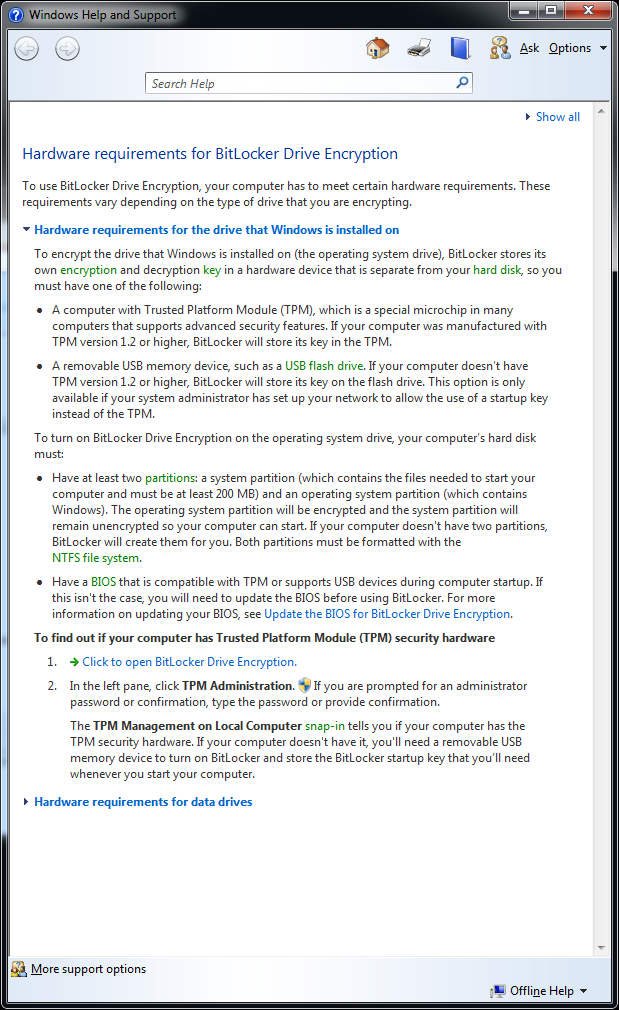
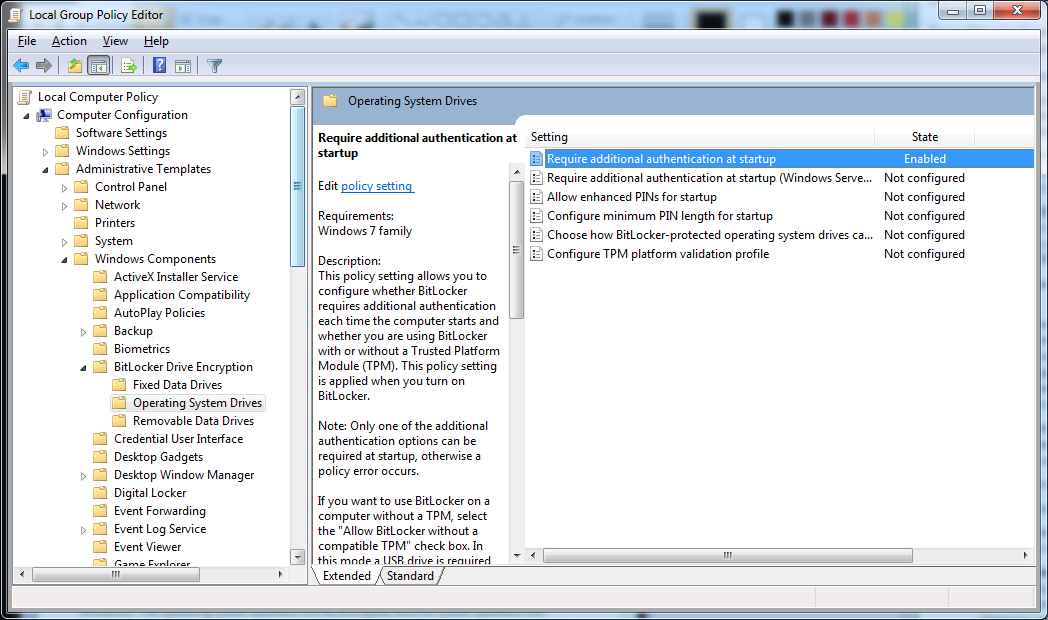
There are a number of hardware requirements that have to be fulfilled before deploying BitLocker. Please look at the screenshot above for details.
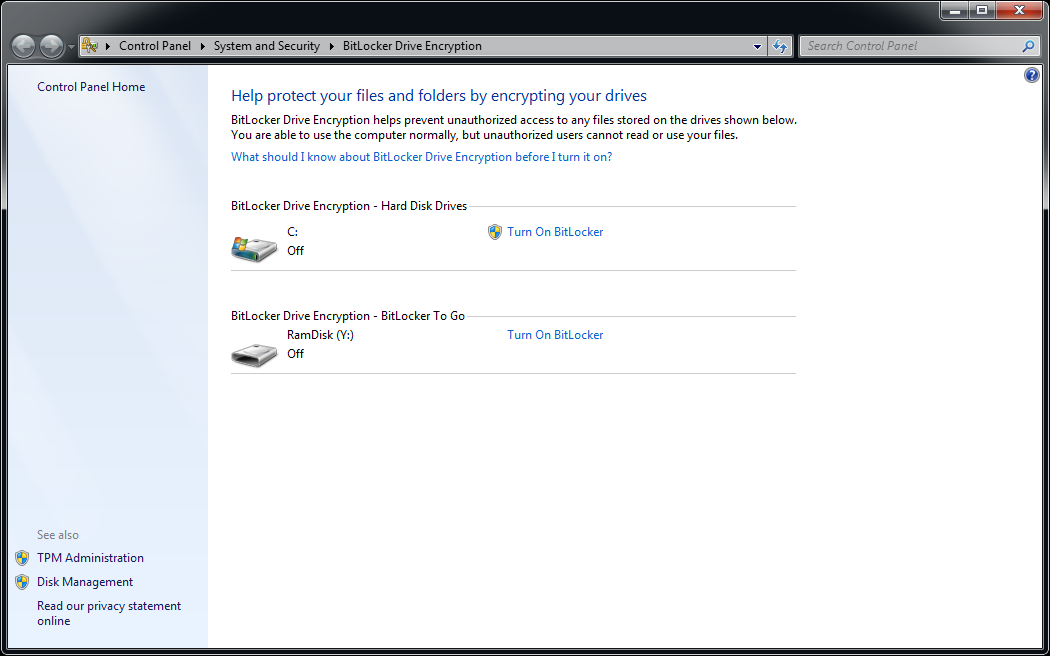
BitLocker's configuration interface can be executed from the start menu search prompt, or by locating it in the start menu structure.
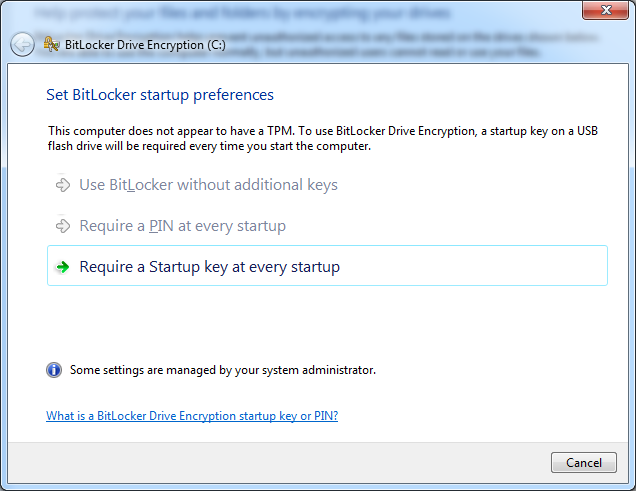
Because our test system didn’t have a TPM, we opted to have the solution check for a startup key every time the system boots. The key is typically provided through a USB thumb drive.
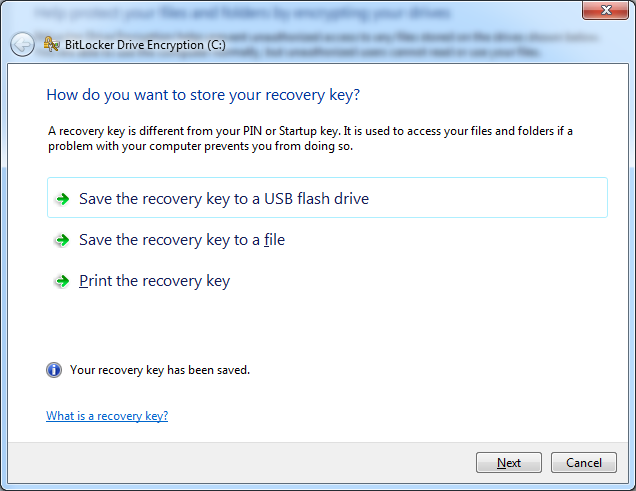
Here you can choose where to copy the recovery key, which you need in case you lose your PIN or thumb drive containing the passkey.
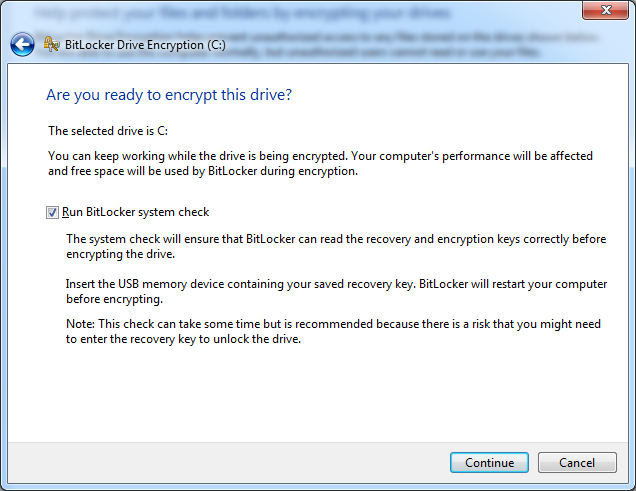
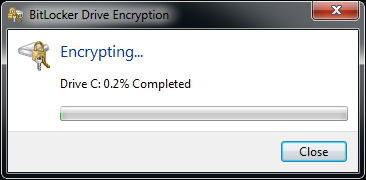
We’re ready to encrypt!
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: BitLocker On Windows 7 Ultimate x64
Prev Page A Bit-Locking And Cryptography Exercise Next Page TrueCrypt 6.3a On Windows 7 Ultimate x64