ESA To Adopt Controversial Quantum Key Distribution For Satellite Communications
The European Space Agency (ESA) will start investigating how to use “quantum key distribution” (QKD) for secure communications between its satellites. Countries such as Switzerland, Austria, and China have already experimented with QKD and implemented it in some of their satellites.
QKD Is “Guaranteed By The Laws Of Physics”
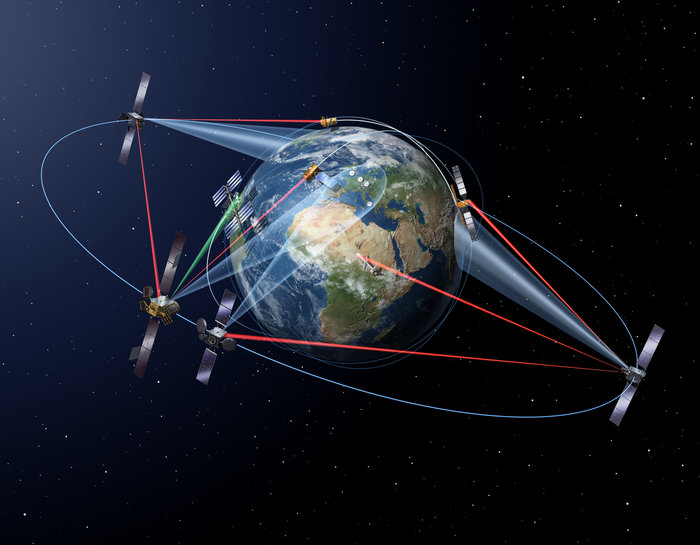
ESA signed a contract with SES Techcom S.A. (LU) to develop the Quantum Cryptography Telecommunication System (QUARTZ), which is a satellite communications platform that uses QKD.
The idea behind QKD is that a secret code is sent from one place to another, and the people on the other side need the key to decrypt that code. This is similar to you sending a friend an encrypted .zip file and then having to give them the password over a secure channel, too, while hoping that no one will intercept that password.
Article continues belowThis is also similar to how messages were sent in World World 2. However, we’ve since discovered public key cryptography algorithms that allow us to send only a public key to the recipient, so it doesn’t matter if someone between the sender and the receiver captures that key in transit, because it’s meant to be public. What you need to secure is the private key, which stays on your computer or server. This is how PGP and HTTPS work.
Unlike with PGP, with QKD you need to send the key along with the message through a secure channel. In this case, that secure channel is “guaranteed by the laws of physics” (as many QKD proponents like to say), because the key is sent through entangled photons. The moment anyone tries to look at the key sent over those entangled photons their quantum properties will change. That means the interception will be detected and the communications can be abandoned and restored later. This is why QKD’s proponents believe that QKD is the best form of encrypted communications.
QKD Controversy
The issue with the QKD system is that it seems to be promoted primarily by physicists, rather than cryptographers. In fact, prominent cryptographers such as Daniel J. Bernstein, the same cryptographer who fought the U.S. government’s rules that put export controls on encryption, and whose cryptographic algorithms have been adopted as IETF standards (Curve 25519, ChaCha20, Poly1305, etc), believe it’s awfully insecure.
In a recent paper, Bernstein claimed that attackers would in fact be able to record messages sent over QKD via a large array of radio receivers, if the collection of data starts before the QKD communication begins. This seems likely given how intelligence agencies operate these days by collecting all the data they can at all times. Bernstein also claimed that QKD systems will likely be vulnerable to all sorts of side-channel attacks.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
As ESA is formed of scientists and physicists, it may be more inclined to believe the claims made by other physicists about QKD, instead of claims made by cryptographers whose sole jobs are to build secure communications.
Alternatively, if ESA’s thinking here is to use some form of “quantum encryption” to counteract the threat of quantum computers breaking all conventional encryption (in use today), then that may not be the best solution either. Cryptographers such as Bernstein have been working on “post-quantum” algorithms that are resistant to quantum computers and they don’t require any quantum phenomena to protect communications. One such algorithm, called “New Hope,” has already been implemented in a developer edition of the Chrome browser.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
bit_user Reply
I'm slightly confused, here. As the name suggests, I thought the idea was only to send the key through the quantum channel. The message would be sent normally, but requires the key in order to be decrypted. I assume the reason for doing it this way is that the quantum channel is lower-bandwidth and/or overuse could cause entanglement to be lost much sooner.20940800 said:with QKD you need to send the key along with the message through a secure channel.
I'm also curious about the side-channel attacks. Is the idea that the radar array would be used to spy on the end-point device? Somewhat akin to peering though the window at a spy, while they're in the act of decoding & reading a secret message?