How Secure Is The Cloud?
Data Encryption
How is data encrypted, both in use and at rest, when stored in the cloud infrastructure?
Most cloud providers automatically encrypt data in transit by requiring SSL connections on any Web browser, but whether this data is stored in encrypted containers is another matter. The best way to do things is to create a hybrid public/private cloud so that any cloud-based resources can sit behind the corporate firewall and be protected just as if they were inside your own data center. See Public And Private Hybrid Clouds: The Pros And Cons for more on this.
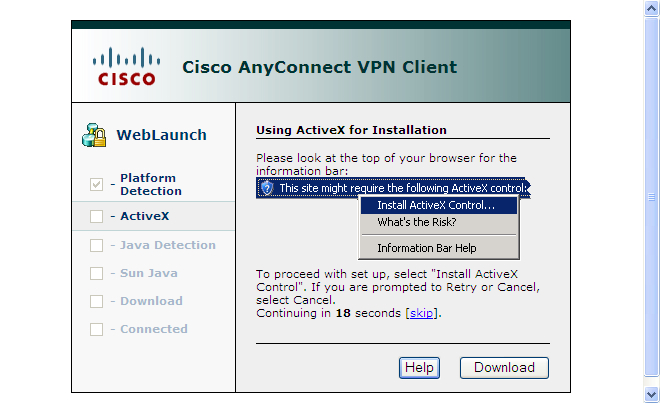
Most cloud vendors offer some kind of Virtual Private Network (VPN) protection of their environments, so that information is encrypted in transit and easily accessible via ordinary network shares. As an example, Verizon's Computing as a Service offers Cisco's AnyConnect VPN client that is launched from Internet Explorer.
Other cloud providers offer virtual firewalls from vendors, such as Vyatta, that connect to their twins inside a corporate data center, or work with traditional Cisco VPN gateways.
One of the numerous Amazon Web Services is its Virtual Private Cloud, which allows you to connect any of your Amazon-based cloud-based resources to your own premises. You can bridge your Amazon and on-premises networks, assign private IP address ranges, and route traffic from your applications running in the cloud to your internal security devices before reaching the Internet.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: Data Encryption
Prev Page Perception Vs. Reality Next Page Fine-Grained Access ControlsDavid Strom is the former editor-in-chief at Tom's Hardware and the founding editor-in-chief of Network Computing magazine. He has written thousands of articles for dozens of technical publications and websites, and written two books on computer networking.
-
fstrthnu Answer: It's safe IF you play your cards right, but almost all of the time you can forget about decent securityReply -
You haven't really addressed many of the security concerns IT pros have about "the cloud". Who potentially has access to my data, what controls are in place to keep that data safe (ie could a rouge employee rip backup of my DB and take it home)? How are other legal situations handled, such as warrants/requests for data from law enforcement, will the customer be notified, will the vendor simply comply, etc? What happens *IF* the cloud vendor goes out of business one day, where is my data (one would assume there would be warning signs before this happens, but stranger things have happened)? There are tons of questions with not many good answers out there.Reply
-
babachoo This article has been brought to you by domestic datamining organizations and the people they have in their pockets.Reply -
gonebamboo Check out this cloud-based (Software as a Service) platform and its security architecture.Reply
http://www.otakhi.comhttp://www.otakhi.com/pages/security.html -
ludikraut This article barely scratches the surface of security issues surrounding cloud computing. It reads more like an executive summary than something I would expect to see on Tomshardware - very disappointing.Reply -
Cloud computing is overrated. Your data will never be secure in someone else's hands. Any encryption can be broken with time.Reply
-
I didn't really see any mention of on-site encryption in this article, only transport encryption. Also, who assures us that claims made regarding security are entirely true instead of being marketing word-play which seems so popular these days. Only when a cloud service publishes results done by a third party auditor that I trust will I use them.Reply
-
gtaker If you are in the external cloud with your company your data will be compromise.. I'm 100% sure of that... we look at this cloud stuff 8 years ago and came to that conclusion if you need to do it, do it inside your company not outside...Reply -
sadams04 Security is always a concern, but my main concern with the cloud is around someone else being responsible for up-time / availability. Those priorities rarely line up across multiple companies. While you may recover lost revenue through a breach in service level agreements, you can't recover customer perceptions and experiences in the same way.Reply -
perrakis There's an updated version of the Ponemon Cloud Security Study available from the report's sponsor, Dome9: http://www.dome9.com/resources/ponemon-cloud-security-study.Reply
Incidentally, Dome9 offers free cloud security for an unlimited number of servers. You can check them out at http://www.dome9.com. Essentially, their value prop is the ability to close administrative ports on a remote cloud server and make access available on demand. This is important in the cloud where your servers operate outside your traditional network, and leaving ports open exposes them to hackers, brute force attacks, and exploits.