Cyberhack Hides Malicious Code in Your Graphics Card's VRAM
Undetectable by antivirus
Cybercriminals are looking to exploit your graphics cards by hiding malicious code inside of its VRAM. This would stop the code from being detected by antivirus scanners sweeping the PC's main RAM. Just a few days ago, a proof-of-concept (PoC) for a tool that makes this possible was sold online, Bleeping Computer reported today.
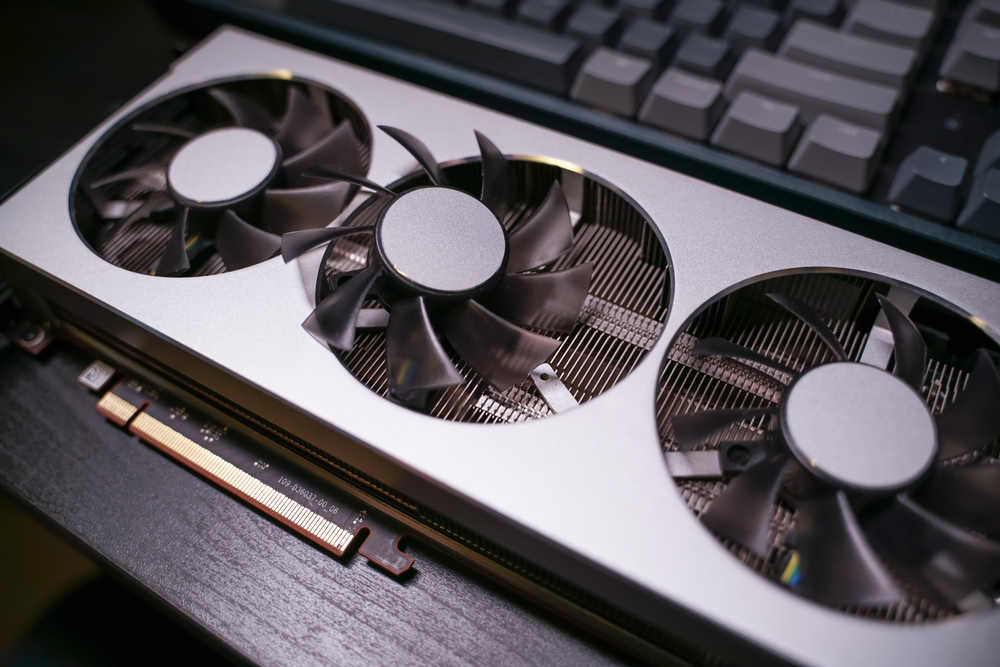
Graphics cards are dedicated to one task: providing and accelerating 3D workloads. However, modern and the best graphics cards represent their own complete ecosystems that are just focused on accelerating graphics. They contain thousands of cores for video acceleration, few control cores for managing it all and, of course, their very own memory buffer (VRAM) to load all of those game textures.
According to the recent hacker forum listing cited by BleepingComputer, it's possible to hide the malicious code in the graphic card's memory buffer without the rest of the system detecting it. Details were limited, but the posting hit the web on August 8, and was reportedly sold by August 25 for an undisclosed amount.
While we don't exactly know how the exploit works, the hacker offered the toolkit with the PoCdescribing it as an exploit that allocates address space in the GPU VRAM and stealthily inserts and executes the code from there, since antivirus can not scan a GPU's VRAM.
For the exploit to run, a user needs a Windows PC that supports OpenCL 2.0 or higher. It has allegedly been tested and works with Intel's UHD 620/630 integrated graphics and Radeon RX 5700 and GeForce GTX 740M and GTX 1650 graphics cards.
Research group Vx-underground tweeted this week that it will demonstrate this technique soon.
Recently an unknown individual sold a malware technique to a group of Threat Actors.This malcode allowed binaries to be executed by the GPU, and in GPU memory address space, rather the CPUs.We will demonstrate this technique soon.August 29, 2021
It's important to note that this is not the first time we are seeing a similar exploit happening. A few years back, researchers published the open-source Jellyfish attack that exploited the LD_PRELOAD technique from OpenCL to connect system calls and the GPU and force malicious code execution from the GPU. You can check out the Jellyfish attack on GitHub here. This code shows that you can use OpenCL to hide the code in GPUs without PC detection.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
It'll be interesting to see what new ways researchers find to embed malicious code. We may have opened Pandora's box with these exploits.
-
digitalgriffin Not surprising. You can hide malicious code inside a graphics file like png or jpg.Reply -
BogdanH Of course you can hide malicious code (or anything else) inside image file. But in that case, that code can't be self executable -that is, image file is only a container (carrier) . To actually execute code (inside image file), separate app (exe, bat, etc.) is needed. And that is then a matter of "don't run an app you don't know and trust" -should be written on front of every PC case.Reply
In my opinion, in 99.9% cases, PC's get infected because users are just opening every stuff they get. -
AjayAB Is linux and mac os safe? does this only work on windows or it affects everything that has a gpu , and what about apu s?Reply -
USAFRet Reply
From the article:AjayAB said:Is linux and mac os safe? does this only work on windows or it affects everything that has a gpu , and what about apu s?
"For the exploit to run, a user needs a Windows PC that supports OpenCL 2.0 or higher. It has allegedly been tested and works with Intel's UHD 620/630 integrated graphics and Radeon RX 5700 and GeForce GTX 740M and GTX 1650 graphics cards. " -
Joseph_138 I'm sure the people who make anti-malware are already hard at work on a solution for this. They are usually pretty fast on the uptake when new threats present themselves.Reply -
Todd Sauve They ought to be able to track down these hackers posting malicious code and tools and toss them in the clink. I have no sympathy for them when they get caught.Reply -
vacavalier ReplyTodd Sauve said:They ought to be able to track down these hackers posting malicious code and tools and toss them in the clink. I have no sympathy for them when they get caught.
Problem with hackers is, they reside on all continents and some are group-hacks sponsered by their homeland governments ; i.e Russia, China, etc. This type of code presents obvious and direct ramifications for coin-ming operations/ farms.