Windows 8 Picture Passwords Easy to Crack, say Researchers
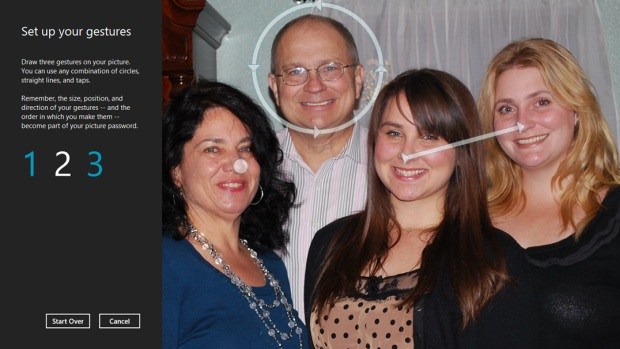
Researchers have found a way to get past Picture Gesture Authentication.
Recently during the USENIX Security Symposium, researchers from Arizona State University, Delaware State University and GFS Technology Inc. presented "On the Security of Picture Gesture Authentication," a paper (pdf) showing that most unique picture password gestures used in Windows 8 aren't quite so unique. In fact, it may not really matter what picture the Windows 8 account holder uses: the login screen can still be easily bypassed.
"Based on the findings of our user studies, we also propose a novel attack framework that is capable of cracking passwords on previously unseen pictures in a picture gesture authentication system," the paper states. "Our approach is based on the concept of selection function that models users' password selection processes. Our evaluation results show the proposed approach could crack a considerable portion of collected picture passwords under different settings."
Through online studies, the researchers analyzed picture gesture authentication on more than 10,000 picture passwords collected from over 800 subjects. They discovered that one of the most common methods used in this authentication process was with a photo of a person and triple tapping on the face, one of which lands on the eyes. The study also discovered that users would rather upload one of their own photos than use an image provided by Microsoft.
Article continues belowThe study determined that there is a relationship between the background images and the user's identity, personality or interests. Images used in the study ranged from celebrity wallpapers to in-game screenshots, but most users chose pictures of people. Around 60 percent of the users surveyed selected areas on the image where "special objects" were located. Even more, eyes were the most frequently used area followed by the nose, hand or finger, jaw and face.
"It is obvious that pictures with personally identifiable information may leak personal information," the paper states. "However, it is less obvious that even pictures with no personally identifiable information may provide some clues which may reveal the identity or persona of a device owner. Traditional text-based password does not have this concern as long as the password is kept secure."
At the end of the study, the researchers had gathered enough evidence to develop an attack framework capable of cracking passwords on previously unseen pictures in a picture gesture authentication system. The researchers want this framework to serve as a picture password strength meter so that users can better protect their systems. Microsoft could impose a no three-tap rule to help ensure a better tap-based password, but rule-based passwords typically are ineffective for traditional text-based versions, the researchers said.
"The cornerstone of accurate strength measurement is to quantify the strength of a password," the paper states. "With a ranked password dictionary, our framework, as the first potential picture-password-strength meter, is capable of quantifying the strength of selected picture passwords. More intuitively, a user could be informed of the potential number of guesses for breaking a selected password through executing our attack framework."
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
To read the full paper, check out the pdf document here.

Kevin Parrish has over a decade of experience as a writer, editor, and product tester. His work focused on computer hardware, networking equipment, smartphones, tablets, gaming consoles, and other internet-connected devices. His work has appeared in Tom's Hardware, Tom's Guide, Maximum PC, Digital Trends, Android Authority, How-To Geek, Lifewire, and others.
-
DRosencraft I would say the first obvious step would be to require more than just three points of interest for the gesture entry. I don't know that you really need a research paper to point out that someone who is lazy about their password settings is going to pick the three most noticeable spots on the picture. Having five or six points should help a significant amount.Reply
Further from that, however, alpha numeric passwords still seem to be the most logical and functional password protection so long as the user is smart about it and not putting in the obvious strings (QWERTY, 12345, Password, etc.).
But, this is mostly a moot point anyway since I don't know that most criminals are bothering with trying to crack your Windows password. I suspect that this story is meant less about Windows specifically, and more as a general warning to any company looking to use gesture input as an authentication method for any type of account (i.e bank, credit cards). -
althaz If a password has only 7-8 digits it's the exact opposite of secure. 12+ characters are a requirement for a secure password (there's a lot more, but 8 or less characters is absolutely worthless as it can be easily brute forced, which isn't realistically feasible for 12 character passwords yet).Reply -
I find it rather silly to first use 800 subjects to study their patterns and then execute ill intent conclusions.Reply
Firstly, if anyone with ill intention had access to 800 Win 8 machines why in their right mind would they care to crack a password. This is like saying that 60% of 800 bank customers use a pin consisting of "1234", and then go on to conclude that bank X has a poor security system. If a crook knew that there is a 60% chance that a bank debit card has 1234 pin then why would the crooks resort to steeling pin codes with various contraptions. -
Grandmastersexsay Log on passwords are relics of a bygone era when multiple people used one computer. Today, one person uses multiple computers. Most work computers are actually company issued laptops that are brought home each day.Reply
Log on passwords are useless and ineffective. If you are one of the few people today who leave their computer vulnerable to physical attack, you would be better served with a drive encryption based password setup.
For the other 99% of us I recommend auto login. If your computer gets stolen, the criminal doesn't care about your work projects that you should have backed up anyway or your minecraft saves. Anyone who keeps sensitive information on their computer or information they can't easily replace is doing it wrong, and will probably get screwed over by a virus long before a physical attack on their computer would. -
_Cosmin_ Just because anyone can guess your "special objects" on login image of Kate Upton naked... does not mean that login system has a flaw!Reply -
apache_lives not as if passwords are secure either - normal Windows passwords can be stripped in under two minutes (XP - 8.1), Windows XP password protection is a jokeReply