Android P Will Encourage OEMs to Adopt Stronger Biometric Systems
Starting with Android P, device makers will have to pass new security-focused benchmarks for their biometric authentication systems if they want their customers to have a better biometric authentication experience.
FAR And SAR Biometric Benchmarks
The smartphone industry has used two primary metrics to benchmark the accuracy and precision of biometric authentication: the False Acceptance Rate (FAR), and the False Rejection Rate (FRR).
The first one tells you how likely it is for the phone to incorrectly recognize a biometric input as belonging to you. For instance, if the FAR is 1 in 50,000, then one random fingerprint in 50,000 could unlock your phone, even if that person’s fingerprint wasn’t registered with the device.
The FRR, on the other hand, tells you how often the phone will fail to recognize you, its registered owner. The two metrics can be see in conflict with each other, as the “easier” you make it for the phone to recognize your fingerprint or face, the more likely it will be that other people will be recognized as the owners of that device.
SAR and IAR: New Security-Oriented Biometric Benchmarks
Google mentioned that the FAR and FRR metrics don’t tell the whole story, nor are they too relevant against attackers. This is why in Android 8.1, Google introduced the Spoof Accept Rate (SAR) and Imposter Accept Rate (IAR) metrics, too. These two metrics measure how easily an attacker can bypass a biometric authentication system.
As this author mentioned in previous posts on Apple’s bypassed Face ID system, Apple’s “1 in a million” FAR was quite misleading, because an attacker would have a much better success rate at bypassing an iPhone’s Face ID than just throwing 1 million random faces at the system.
An attacker who wants to bypass your phone, specifically, would likely also gather your public online photos, try to make a 3D profile out of them, and shape it with machine learning until they succeeded in bypassing the system.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Google’s SAR addresses spoofing techniques such as an attacker using a victim’s voice recording or a picture of the device owner’s face or fingerprint. Similarly, the IAR metric addresses the fact that attackers could also try to mimic the user’s biometric features (such as generating the voice through machine learning, etc).
Strong Vs Weak Biometric Authentication Systems
Starting with Android P, Google will classify biometrics systems of Android devices based on their SAR and IAR scores. If a biometric system gets less than 7% on these metrics, it will be considered “strong.” If it gets a score above 7%, it will be considered weak.
Google admitted that the 7% threshold is quite arbitrary, so it doesn’t necessarily mean that a system just slightly below 7% has good enough security. The company started with the 7% threshold because the biometric implementations on the market today can score lower than that number. However, users would do well to prefer devices with as low SAR/IAR scores as possible.
Google also noted that the SAR/IAR scores are still an oversimplification of how secure a biometric system actually is, because there are a range of factors that determine that security. Presumably one of them would be code quality, too, or whether or not the biometric data is isolated within a hardware security module. The company uses the SAR/IAR scores despite those limitations because they are scalable across the ecosystem, which makes it easier to determine the overall risk Android devices on the market pose, at least when it comes to biometric security.
Google will also impose certain restrictions on the devices that have a SAR/IAR above 7%:
- Users will have to enter a PIN, pattern, or passphrase if the phone is not unlocked for four hours straight. This is in addition to the the same thing being required of all devices after 72 hours.
- The devices will not be supported by the Android P BiometricPrompt API, so the owners of devices with weak SAR/IAR will not be able to authenticate to third-party apps with biometrics
- The devices can't authenticate payments or participate in other transactions that involve a KeyStore auth-bound key
- The phones must show users a warning when enabling biometric authentication on them.
All of these measures are meant to allow weaker biometric authentication, but still minimize the risk of unauthorized access, according to Google.
BiometricPrompt API
Google announced the BiometricPrompt API at its latest Google I/O developer event. The API will allow developers to integrate their applications with biometric authentication in a device-agnostic way, which means the developers won’t have to care about each individual implementation of biometric authentication from multiple smartphone vendors.
Google will also make available a support library that will enable the BiometricPrompt API for Android O devices. However, as mentioned above, those devices will also need to have an SAR/IAR score below 7%.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
InvalidError I personally don't care how strong biometrics are: no matter how good they are, relying on biometrics mean you can be strong-harmed into unlocking your devices against your will. With reasonably strong passwords only known to you on a secure device, your data is as safe as you are willing it to be.Reply -
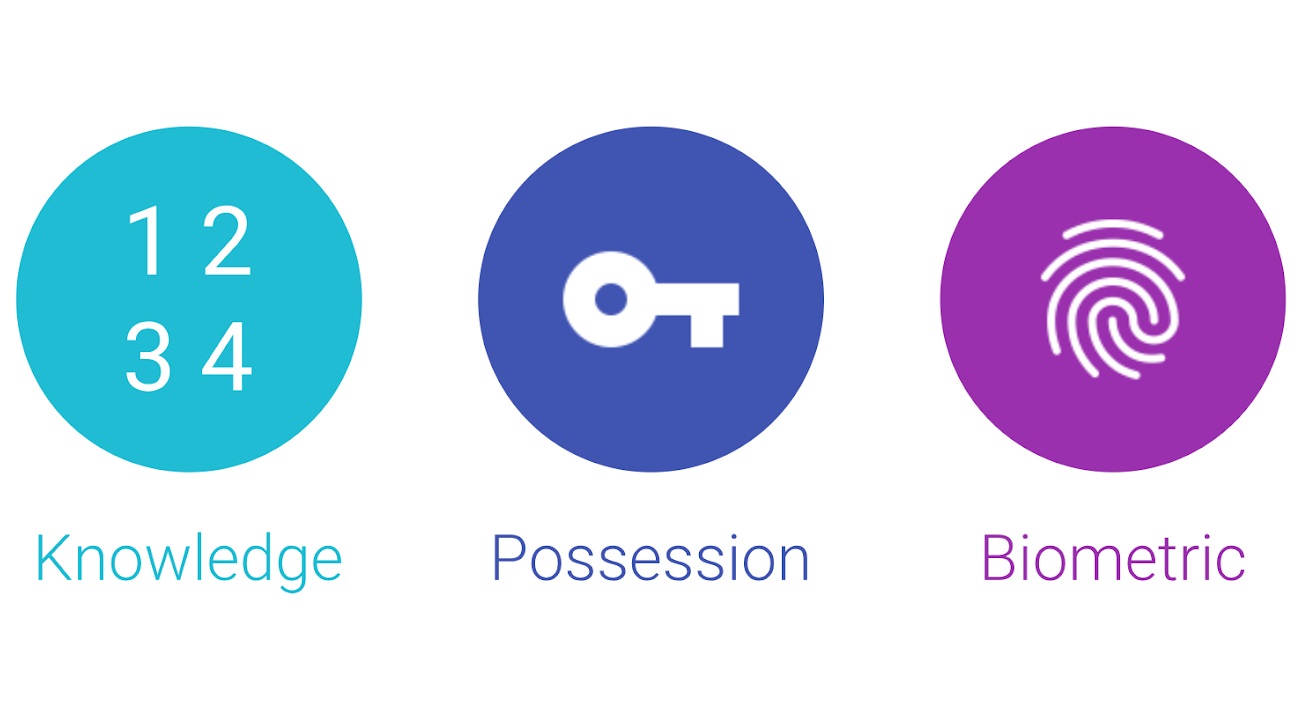
mrjhh INVALIDERROR - And you think a password is safe from a strong-arm approach? Passwords can also be captured from taking a video of you entering the password. This is why a strong authentication is recommended to have two factors from the three options of what you know, what you have, and biometrics. But, with strong authentication, bad guys look for weaker links, like someone at your bank who uses a password of abc123.Reply -
TJ Hooker @InvalidError If an attack is willing/able to grab you, force your eye/face/thumb up to your phone and steal your device, I wouldn't put it past that person to just beat any password out of you instead if required. Unless you're including 'standing up to torture' as part of "as safe as you are willing it to be".Reply -
InvalidError Reply
I was.21080311 said:Unless you're including 'standing up to torture' as part of "as safe as you are willing it to be".
With biometrics only, you have very limited capability of preventing forceful unlock and once your biometrics are compromised by whatever means, you can't change them either. With passwords or "things only you know", you have the option of taking your passwords and your data all the way to the grave if you want to.
Personally, I would be mainly concerned with warrantless searches. If police wants to break into my phone, I'll have them produce proof of plausible cause before I give them access. -
randomizer Reply
I think this is the biggest issue with biometrics. They're convenient but they're basically static. It's comparable to using the same password everywhere and being unable to change it when it's compromised.21080518 said:With biometrics only, you have very limited capability of preventing forceful unlock and once your biometrics are compromised by whatever means, you can't change them either.
It's a nice option to have but in practice few people would take it. I only need one of your fingers to pass the biometric scan. I can use the other nine to extract the password from your head. :)21080518 said:With passwords or "things only you know", you have the option of taking your passwords and your data all the way to the grave if you want to.
-
InvalidError Reply
For people who are mainly concerned about resisting warrantless searches, the torture option is generally not available to law enforcement in civilized countries :)21083666 said:It's a nice option to have but in practice few people would take it. I only need one of your fingers to pass the biometric scan. I can use the other nine to extract the password from your head. :)
-
Mr5oh Reply21079595 said:I personally don't care how strong biometrics are: no matter how good they are, relying on biometrics mean you can be strong-harmed into unlocking your devices against your will. With reasonably strong passwords only known to you on a secure device, your data is as safe as you are willing it to be.
Not to mention in the US, you can plead the 5th on a password, you can not on a fingerprint. You can be forced to unlock your phone by finger print if it will. At least this has been the way this has gone down historically. -
InvalidError Reply
Pleading the fifth only comes after you have been indicted and are facing possible criminal charges. With biometric unlock, police can perform multiple breaches of due process such as wrongful arrest, arrest under false pretense and warrantless search, then charge you of other stuff based on what it finds on your devices, then you have tons of extra accusations to deal with while building your violation of due process case to get the whole thing thrown out of court.21087686 said:Not to mention in the US, you can plead the 5th on a password, you can not on a fingerprint. You can be forced to unlock your phone by finger print if it will. At least this has been the way this has gone down historically.
With a strong password, the police will have to prove just cause to want your devices decrypted before there are any consequences to denying access and you have a fair chance of not getting to the point of needing to plead the fifth. (At least not for reasons completely unrelated to your original arrest.)
Got to love how the privately run prison system in the USA has corrupted or is colluding with large chunks of the legal system to imprison as many people as possible for as long as possible for profit. -
electronicbineries What difference does it make when all the CPU's in the market are plagued with security holes that allows hackers to steal passwords and encryption keys.Reply