Microsoft Ditches Windows 10's Password Expiration Policies
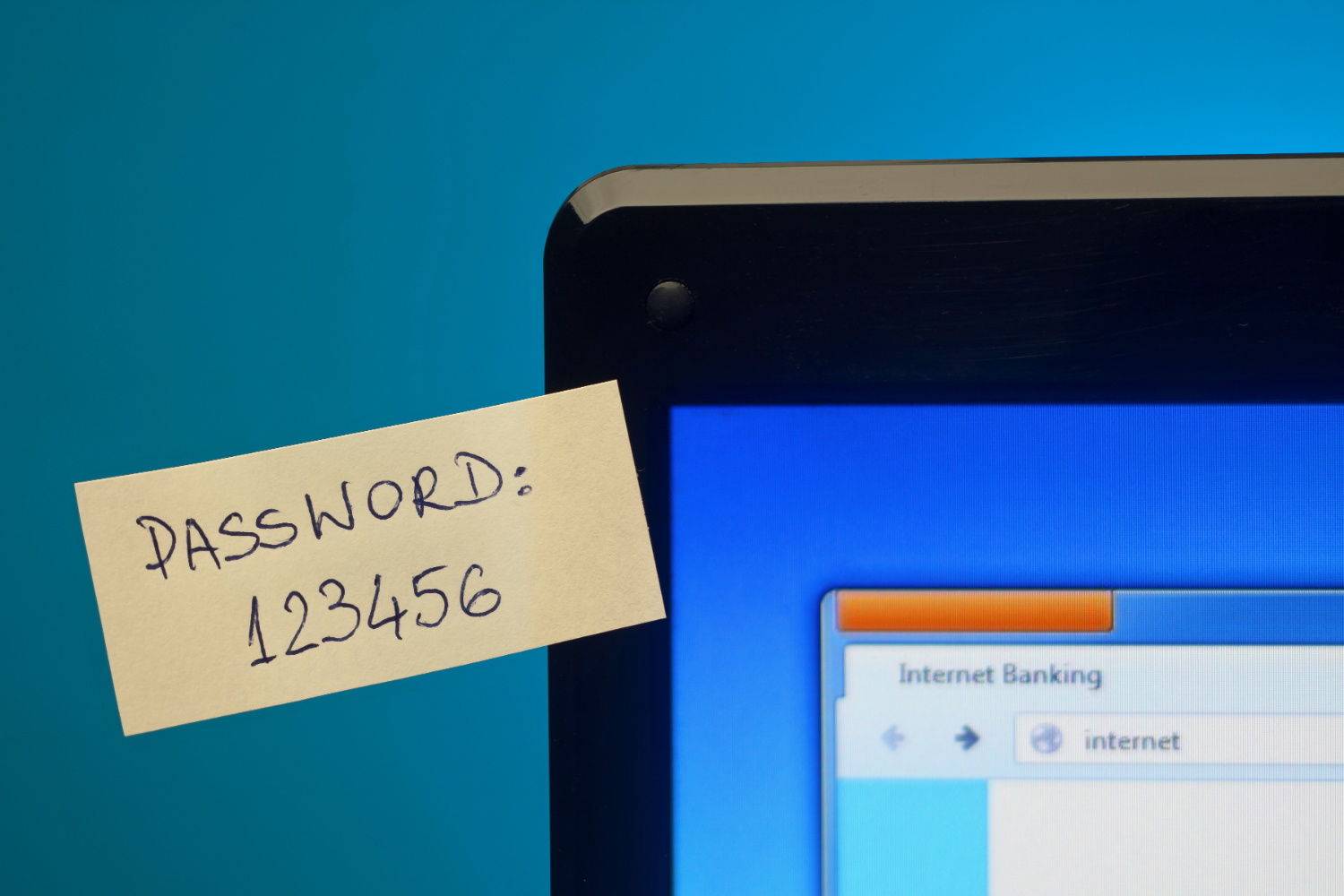
It's no secret that most people are bad at creating, remembering and storing passwords. Companies have tried all sorts of ways to address this problem, from increasingly complex password requirements to forced password resets following high-profile data breaches. But perhaps none are more frustrating than expiring passwords. Which is why Microsoft has decided to ditch Windows 10's password expiration polices.
The company said on its Microsoft Security Guidance blog on May 23 that Windows' password expiration policies often frustrate people without actually keeping them that much safer. "Periodic password expiration is an ancient and obsolete mitigation of very low value," Microsoft principal consultant Aaron Margosis wrote, "and we don’t believe it’s worthwhile for our baseline to enforce any specific value."
Microsoft reached that conclusion by reconsidering how password expiration policies work in the real world. It turns out that having passwords work for a set interval isn't particularly helpful from either a convenience or a security perspective. So rather than continuing to contribute to the problem, Microsoft decided to remove its baseline and encourage other companies to think of their individual needs.
Here are the problems:
Forcing people to regularly change their passwords encourages them to use minor variations of the same "base" password (like changing "Ilovemydog12" to "Ilovemydog13") because they're easier to commit to memory. This defeats the purpose of setting a new password, though, because any hacker worth their ominous grey hoodie is going to test variations of a compromised password to see if they work.
Password expiration policies assume that it's okay for a password to be compromised for a certain length of time. This is going to vary by organization; we suspect Mom and Pop's Misc. Shop cares less about the security of its systems than a Fortune 500 company. It's especially troublesome when someone relies on expiring passwords as their only form of defense against unauthorized access via stolen credentials.
People forget their passwords all the time. While this is related to the first issue, it can also present new challenges for organizations that automatically expire passwords at set intervals. Should those forgetful workers have to create new accounts? Does the IT department get to reset passwords willy-nilly? How many times can someone enter the it-was-right-last-week password before causing a problem?
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
It's true that people are bad at using password-based security systems. But password expiration policies solve the problem of 'We can't trust these people to keep their passwords safe' by having those people create more passwords. That's about as helpful as periodically changing the locks on someone who already struggles to keep track of their keys. Let's hope that Microsoft's decision to nix Windows' password expiration policies will encourage more organizations to reconsider what they actually need to do to keep themselves secure.

Nathaniel Mott is a freelance news and features writer for Tom's Hardware US, covering breaking news, security, and the silliest aspects of the tech industry.