Cyberattack Steals PC Data Through Its Power Supply
Security research finds vulnerability in air-gapped systems
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful

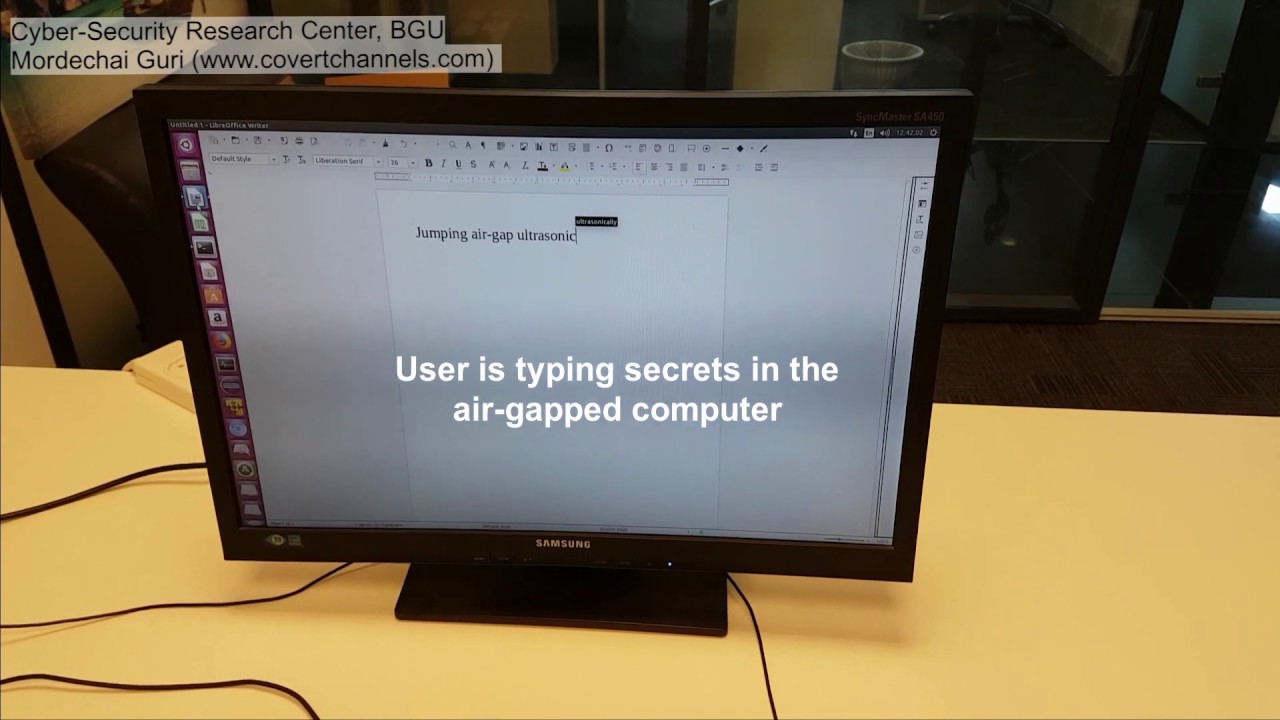
Just two weeks ago Dr. Mordechai Guri from the Ben Girion University in Israel published a paper detailing how to steal data from a PC through fan vibrations, and now he's found another way to snoop on your computer. This time, the reserarcher's done it by making a power supply sing data in ultrasonic [PDF].
The attack is used to siphon data from a totally air-gapped system. For those not familiar, an air-gapped computer is essentially one that's not connected to the internet, Wi-Fi, Bluetooth, or any other remote data connection, such as speakers, and is typically considered impossible to extract data from.
Guri's hack for extracting data through your best power supply is called, quite simply, POWER-SUPPLaY, and works in an equally simple manner. Malware present on the target PC reads out system data, and then alters the CPU's workload to cause changes in the system's load on the power supply. Although you can't hear the power supply, changing loads on it does alter the ultrasonic frequencies they produce, which the attacker then reads out using a mobile phone capable of recording the frequencies at a maximum distance of 5m (16.4 feet). The attack doesn't require any special hardware privileges to work.
Article continues belowThe noise generated by the power supply comes from its transformers and capacitors, typically somewhere in the 20 kHz to 20 MHz range, according to the researcher. It is kind of like coil whine but beyond the audible range of human hearing.
However, this attack wouldn't be particularly effective in a real-life scenario. Although the success rate is high, the data rate of the attack is a measly 50 bits per second, or equivalent to about 22.5 kB per hour. That works out to about 10,000 words stored in plain text.
Another factor limiting the attack is that it requires malware to be installed on the target computer, as well as access to a nearby mobile phone for recording the data. It's also worth noting that if an attacker had access to all these devices, there'd be easier and more effective ways to extract data.
Therefore, we wouldn't worry about going to extreme measures to prevent this type of attack. Guri's research is meant primarily to showcase what could be done by attackers were they so inclined, with his work showing how to extract data when there are no viable alternatives, due to extreme security.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Next to siphoning your PC's data through its power supply, Guri's past methods for overcoming the security of air-gapped PCs include extracting data through fan vibrations, monitor brightness changes, HDD activity LEDs, data transmission through your PC's internal buzzer and keylogging through reading electromagnetic signals.
Niels Broekhuijsen is a Contributing Writer for Tom's Hardware US. He reviews cases, water cooling and pc builds.
-
drtweak I remember reason something a while back about a major power cable manufacture that moved out of china, because all the OEM were pressuring it because malicious chips could be installed in the power cable. Wonder how true that is and wonder if it could pair with this. Its amazing the kinds of way people try to compromise systems.Reply -
InvalidError Before you can send data over audio or visual air-gap side-channels, you also need access to the data on the system itself. All the side-channels in the world won't do you much good if you cannot beat access controls and encryption.Reply -
bit_user ReplyHowever, this attack wouldn't be particularly effective in a real-life scenario. Although the success rate is high, the data rate of the attack is a measly 50 bits per second, or equivalent to about 22.5 kB per hour. That works out to about 10,000 words stored in plain text.
The author lacks imagination. This data rate is more than fast enough for nuclear launch codes, encryption keys, or certain other extremely high-value data.
Heck, the SARS-CoV-2 virus is only 30k base-pairs. If I'm not mistaken, that would take only 10 minutes to copy. And the key molecules in a vaccine could be much smaller, depending on the data format. -
bit_user Reply
Yeah, we had this whole discussion in the comments of the previous article (steal data from a PC through fan vibrations ).InvalidError said:Before you can send data over audio or visual air-gap side-channels, you also need access to the data on the system itself. All the side-channels in the world won't do you much good if you cannot beat access controls and encryption.
Basically, you need a vector to get malware into the target machine, such as an infected USB stick used by a witting or unwitting insider.
However, especially if the insider is unwitting, just because you can get malware onto the target doesn't mean you can get data off of it. That's where these sorts of exploits come into the picture.
And before someone brings this up (which I'm sure they will, anyhow): if you're not in possession of data that a government agency or extremely motivated non-state actors would want, the exploit should be of no concern to you. -
InvalidError Reply
In a proper air-gapped system, you shouldn't have access to USB ports without extra layers of verification and supervision. Whatever external data you want to bring in would likely get screened and transferred to a separately approved USB key to prevent hidden malware. Ideally, the whole system would also be locked away in a separate room from where people access the monitor, PS/2 keyboard and mouse.bit_user said:Basically, you need a vector to get malware into the target machine, such as an infected USB stick used by a witting or unwitting insider. -
bit_user Reply
Yeah, of course. It was just a simple example that everyone can understand.InvalidError said:In a proper air-gapped system, you shouldn't have access to USB ports without extra layers of verification and supervision.
At some point in its life, even an air-gapped system must be installed. The malware could even have been incorporated into the installation image, or perhaps into some updates/drivers/etc. that get installed at some later point in the machine's life.
Oh, you're not being nearly paranoid enough. No, I submit that the machine and its windowless room should be in a two-layer Faraday cage, so it remains protected even while the operator is entering & exiting. The machine, itself should be locked in another cage, that prevents physical access.InvalidError said:Ideally, the whole system would also be locked away in a separate room from where people access the monitor, PS/2 keyboard and mouse.
...not to mention lasers - you gotta protect it with lasers! And thermal cameras, drones, and drones with thermal cameras. And maybe an access tunnel that you can only reach when the tide is out. Because it's guarded by sharks, of course. Sharks with lasers. And probably thermal imaging implants, as well.
And no Lady Gaga fans should be allowed near it. That should've been a red flag, right there! -
derekullo Solution 1Create audio distortion on the 20khz - 20Mhz range.Reply
Something is simple as a mechanism for blowing a dog whistle automatically
https://en.wikipedia.org/wiki/Dog_whistleFrom the quick google research I've read most speakers tap out at 20khz.
I am unsure if speakers are capable of going above 100khz or even into the 1Mhz range, but if we are securing nuclear codes, let's assume we spent the money to develop some 20khz - 20Mhz 0hz - 20Mhz speakers.
If we are spending millions of dollars developing super speakers we might as well allow them to play Bohemian Rhapsody in all its glory.
Of course our white noise 20khz - 20Mhz would still be playing in the inaudible background during our music.
Solution 2Place the computer in a vacuum.
You can't hear coil whine or screams in space.
Keeping components cool in a vacuum could be difficult but satellites appear to have no issue, even nuclear powered ones.
According to https://physics.stackexchange.com/questions/149832/cooling-a-satellite/149836Applying a black coating and using an ammonia in a loop heat pipe should be sufficient.
Peltier cooling also comes to mind.
Solution 3Mine bitcoin/altcoins to keep your power supply at a steady power state.
Not a maxed out power supply (that would be bad) but one that is incapable of being given any more work due to GPU and CPU being at 100%.
Something like a 500 watt load on a Corsair AX1600i, which also has the benefit of no fan noise/vibration when below 640 watts.
https://www.kitguru.net/wp-content/uploads/2018/01/L1003218.jpgBitcoin saves the world!!! -
bit_user Reply
Instead of making a high-pitched noise and hoping it drowns out the PSU, it'd be better to look at the spectral distribution of the PSU and target those specific bands via some combination of active and passive means.derekullo said:Solution 1Create audio distortion on the 20khz - 20Mhz range.
Something is simple as a mechanism for blowing a dog whistle automatically
Now you're talkin'! And put a Xenomorph in there, to guard it, in case the intruder gets past the sharks.derekullo said:Solution 2Place the computer in a vacuum.
You can't hear coil whine or screams in space.
But take care not to fry the guard-alien.derekullo said:Applying a black coating and using an ammonia in a loop heat pipe should be sufficient.
Peltier cooling also comes to mind.
This is good, except requires network connectivity. However, plenty of workloads don't, such as computing digits of Pi.derekullo said:Solution 3Mine bitcoin/altcoins to keep your power supply at a steady power state.
Not a maxed out power supply (that would be bad) but one that is incapable of being given any more work due to GPU and CPU being at 100%.
Just keep the CPU continuously at max TDP by scheduling a low-priority task for each hyperthread. Then, buy a PSU with plenty of excess capacity.
Not working, for me.derekullo said:https://www.kitguru.net/wp-content/uploads/2018/01/L1003218.jpg -
Magical.Enema About 2 months ago I needed to oil my fan on my PSU as it was barely, and I mean barely, turning. And it was just starting to let out the magic smoke! But anyhow, I took it all apart and a piece of a fan blade fell out. I cleaned it up, oiled it and put it back together. Only 2 nights in the last 2 months has the computer been shut off, it's been running continuously since the cleaning and oiling. The broken blade is still laying on my workbench down in the shop!Reply
I would be willing to wager that if "they" were listening and recording my PSU vibes, I would be locked away for a very long time.
It's Magical!