How Hardware-Based Security Protects PCs
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
The Future Of TPM In The Chipset
Even with the TPM generating key pairs for encryption, the actual encryption of files or an entire hard drive is done in software; that's slower than doing it in hardware, and the cryptography software could be attacked. And even though the TPM is well protected, it's still sending information across the motherboard. In the next generation of vPro, codenamed McCreary and due in the second half of 2008, Intel will integrate the TPM directly into the chipset.
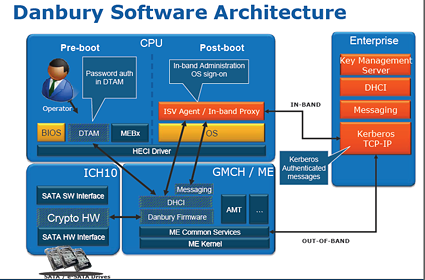
This feature, codenamed Danbury, moves more of the key management and encryption into the Eaglelake chipset. It will be able to fully encrypt SATA and eSATA drives without needing drivers in the operating system. Intel predicts that encrypting through Danbury will be faster than using software alone, because it does 128-bit and 256-bit AES encryption in hardware, and everything that's read from or written to the hard drive will be decrypted or encrypted by the chipset. Danbury will also help when you want to remove all your data from a hard drive; without the keys, the encrypted files can't be read but it will have a function to erase them securely.
Danbury will add hardware AES encryption to the disk controller as well as putting the TPM and associated firmware to the chipset. Click the image to see a larger version.
Encryption software vendors Credant, PGP, Pointsec, SafeBoot and Utimaco have all said that they'll support Danbury hardware encryption. Danbury will also work in what Intel calls "standalone" mode, where password protecting your hard drive will also encrypt the contents using Danbury, so you won't need separate software for basic encryption.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: The Future Of TPM In The Chipset
Prev Page Trusting The Trusted Platform Module, Continued Next Page Encrypt Everything With TPM-
isaacio Yes,the security system once known as "Palladium".Discount Security Systems protect your own home against danger, damage, loss and criminal activity.Reply