Duo Peers Inside The Phishing Economy
Everybody is goin' phishing. Campaigns have attempted to steal information by masquerading as Netflix, using stolen LinkedIn credentials, and impersonating Brazilian and Swiss banks. Or, you know, convincing people to hand over their personal data by pretending to be Google Docs. There's an entire phishing economy, and the Duo security company analyzed thousands of sites to see how things operate behind the scenes.
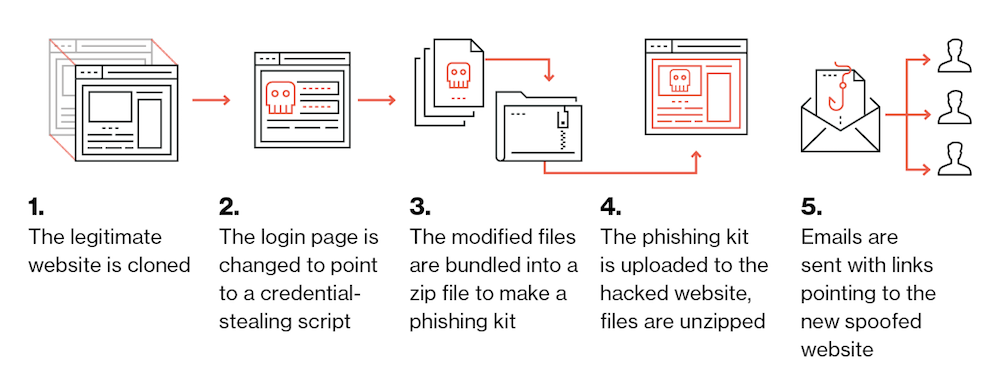
Duo found that many attackers use phishing kits that allow them to quickly compromise a site, spoof it, and steal personal data from their visitors. These kits can be removed from the affected websites to help the hackers cover their tracks, but Duo found that many left the kits on the site and available to download, which allowed the company to connect the dots between phishing sites and the people who profit off them.
In the report, Duo said it found 3,200 unique phishing kits across 66,000 compromised URLs tracked by Phishtank and OpenPhish. The company said there could be more identical kits, however, because it matched them based on their SHA-1 hash. A change to a single file would result in a mismatch even though the rest of the kit is the same. It also noted that this was over a 30-day period; longer analysis would find more matches.
Here are some of the highlights from Duo's report:
We parsed each phishing kit for email addresses indicating both where the credentials are being sent as well as who may have originally created the phishing kit. We tracked individual attackers across multiple phishing campaigns, including one actor whose email address was found in over 115 unique phishing kits.We identified over 200 instances of backdoored phishing kits. This shows that attackers who are selling or distributing these phishing kits to other criminals are actively backdooring them to give themselves access to the compromised hosts. Clearly there's no honor among thieves!
Duo also noted that the majority of compromised sites were running WordPress—which is unsurprising when you consider the platform's popularity—and that 16% of the phishing kits were found on sites using HTTPS. That's important to note because many people might assume an HTTPS website is automatically secure, but that isn't the case; it simply means your connection to the site is harder to tamper with.
These findings highlight just how well-oiled the phishing economy is. There are people making phishing kits, people using them, and people using or selling any information they gather. (Which could in turn be stolen by the people who backdoored their own phishing kits.) That's in addition the targeted attacks—spear-phishing—that attempt to gather information from specific people instead of hoping someone surfs into a wide net.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
There's no easy solution to this problem. Even large companies like Google and Facebook have lost $100 million to phishing scams, too, so odds are good that many individuals won't be able to defend themselves. The only thing you can do is remain vigilant, avoid suspicious content, and keep your fingers crossed. There's a whole industry just waiting for you to slip up so it can find a way to make money off your personal info.

Nathaniel Mott is a freelance news and features writer for Tom's Hardware US, covering breaking news, security, and the silliest aspects of the tech industry.