Qubes OS 4.0 Launches With Fully-Virtualized VMs, Admin API
Qubes OS, a secuity-focused operating system, reached version 4.0 after two years in development. Qubes OS brings a novel idea in the operating systems world of isolating most of the system components and user data into separate virtual machines (VMs). This compartmentalization idea and the project team's singular focus on security is what makes Qubes OS a favorite of Edward Snowden, the NSA whistleblower, too.
New Features
The new edition brings new features such as:
The Qubes Admin APIQubes Core Stack version 3Fully virtualized VMs for enhanced securityMultiple, flexible Disposable VM templatesA more expressive, user-friendly Qubes RPC policy systemA powerful new VM volume manager that makes it easy to keep VMs on external drivesEnhanced TemplateVM security via split packages and network interface removalMore secure backups with scrypt for stronger key derivation and enforced encryptionRewritten command-line tools with new options
Article continues belowQubes Admin API
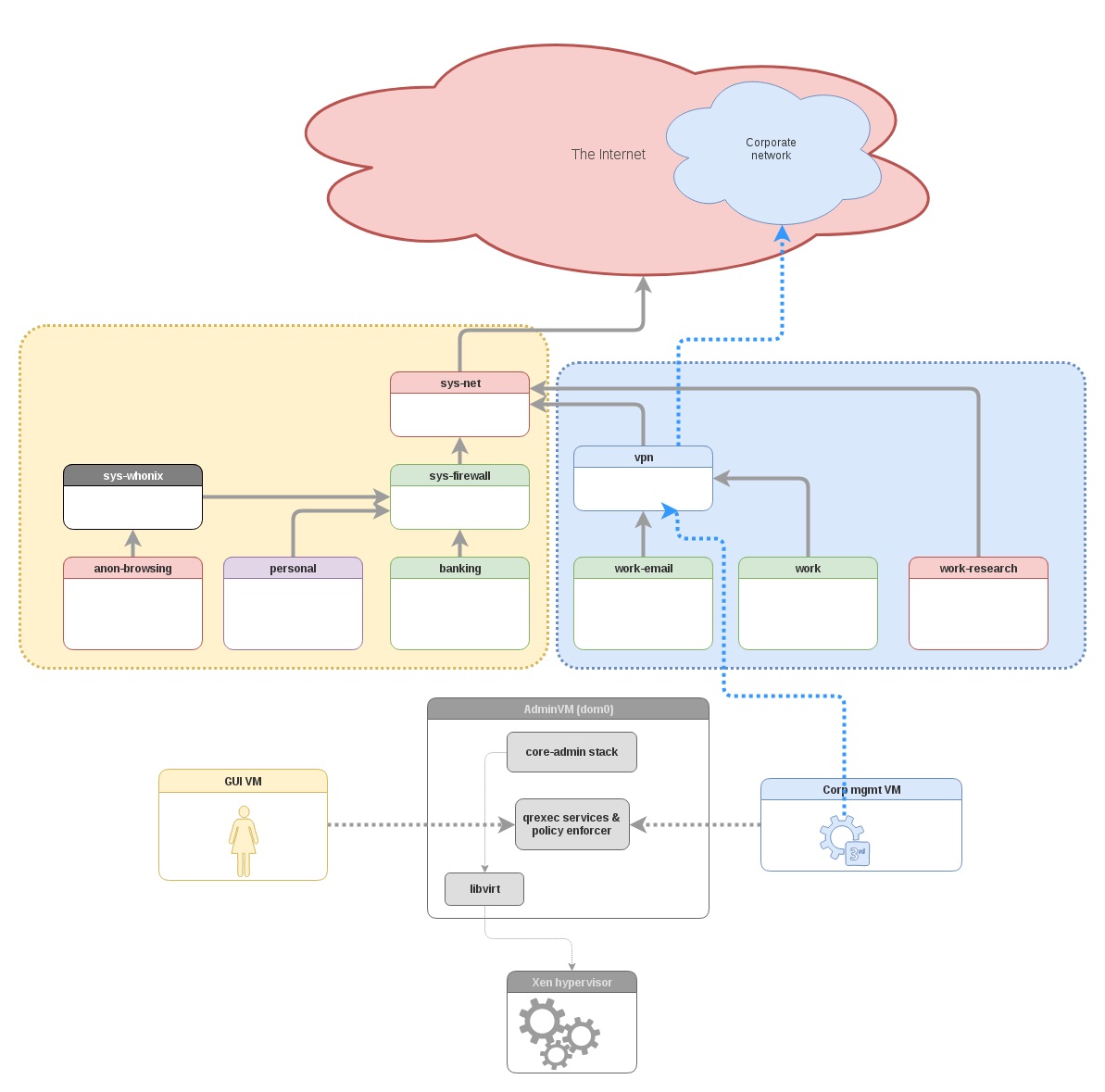
Two years ago, around the same time development of version 4.0 started, the group behind Qubes OS started to focus on targeting enterprise customers as the primary way of funding the project. One of the features that the group thought would be useful to enterprise customers was the Admin API, which can allow IT administrators to remotely manage multiple Qubes machines.
The Admin API would also allow the creation of a multi-user system on a Qubes machine, where each user can have a different set of secure domains/environments. The project’s co-founder, Joanna Rutkowska, said that the Admin API wouldn’t get access to the lowest level of the system, called dom0, and that Qubes OS’ security should be preserved. According to Rutkowska, the Admin API could even be limited so that it can still allow an administrator to configure VMs, but without being able to read the system user’s data.
Fully Virtualized VMs With Meltdown Protection
By default, Qubes OS’ VMs were using “para-virtualization” technology, chosen before for being easier to implement and having higher performance. However, Qubes OS 4.0 implements “fully virtualized” or hardware-assisted VMs to offer better protection against Meltdown attacks.
According to the Qubes team, virtualization may also offer protection against at least one of the Spectre vulnerabilities. The attacker would need to exploit the hypervisor, which is considerably more difficult than exploiting a full operating system. Potential attacks would also be only read-only and they malicious hackers wouldn’t be able to install a backdoor in the system through either Meltdown or Spectre.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
An Update For Qubes OS 3.2 And Qubes OS 4.1
The Qubes team previously announced that version 3.2 would receive extended support, so that companies can rely on a build that’s stable and only receives security patches. The team is also updating this version to 3.2.1, by giving it a newer kernel and updated TemplateVMs (VMs that supply the root filesystem to another VM) that include newer versions of Fedora, Debian, Whonix, Ubuntu, and Archlinux.
The company said that it will now set its sights on developing a growing list of features for Qubes OS 4.1, which should bring enhancements for “nearly every aspect of Qubes OS.” The Qubes team also asked everyone that values the existence of the Qubes OS project to donate so that the OS can continue to see security improvements and support.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.