AMD Quietly Lists 31 New CPU Vulnerabilities, Issues Patch Guidance
Patch your Ryzen and EPYC systems.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
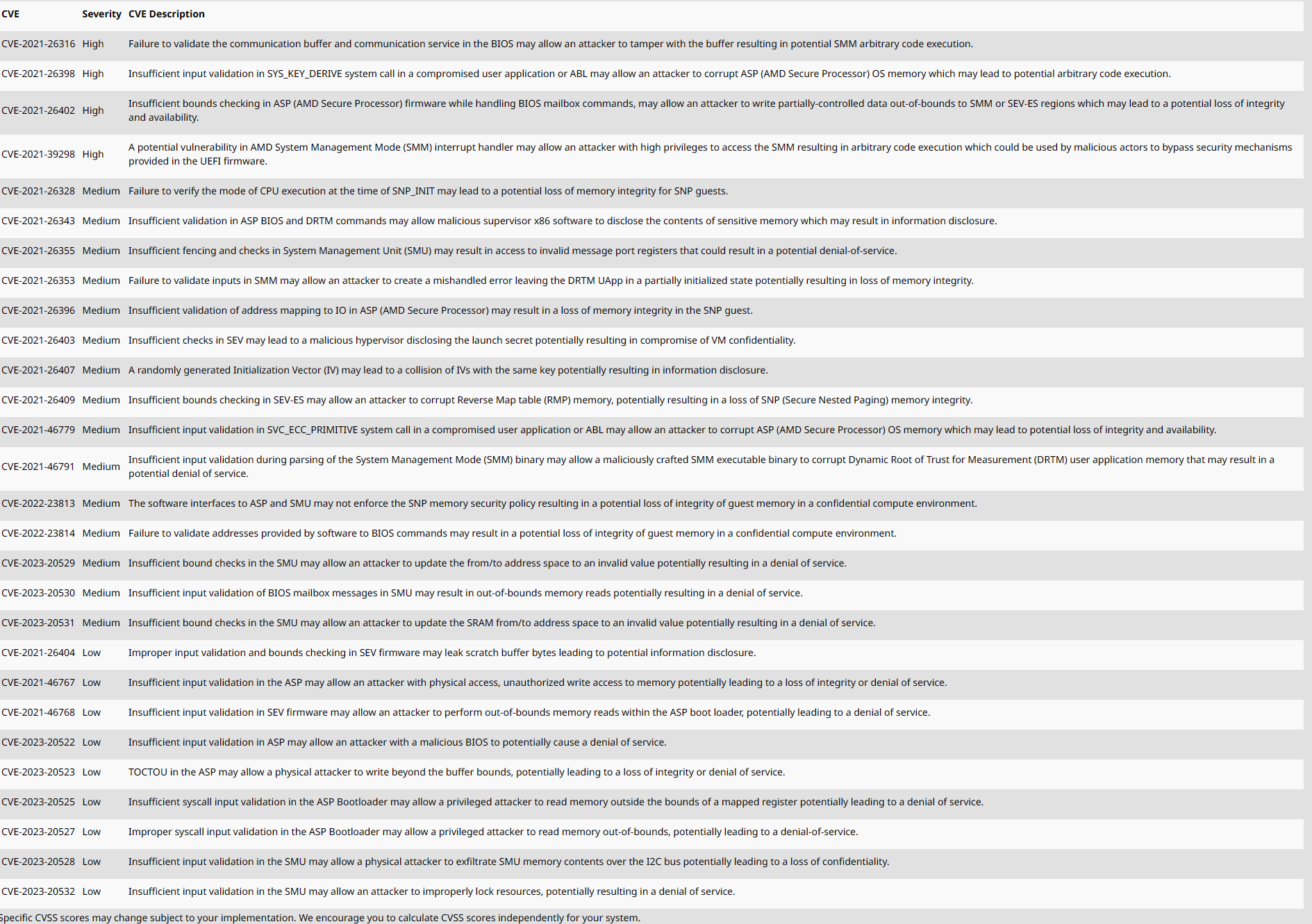
AMD quietly divulged 31 new CPU vulnerabilities in a January update, spanning its Ryzen chips for consumers and the EPYC data center processors. The vulnerability update also includes a list of AGESA versions, with mitigations for the impacted processors. AMD revealed the vulnerabilities in a coordinated disclosure with several researchers, including teams from Google, Apple and Oracle, which gave the company time to develop mitigations prior to the public listings. However, AMD didn't announce the vulnerabilities with a press release or other outreach — it merely posted the lists — so we're working to tease out the details and will update when we have more information.
AMD has listed the various AGESA revisions it has issued to its OEMs to patch the vulnerabilities (AGESA code is used to build BIOS/UEFI code). However, the availability of new BIOS patches with the new AGESA code will vary by vendor. That means you'll have to check with your motherboard or system vendor to see if it has posted new BIOS revisions with the correct AGESA code.
AMD tells us that it typically issues its vulnerability disclosures twice a year, in May and November, but chose to release some in January due to the relatively large number of new vulnerabilities and the timing of the mitigations. It isn't clear yet if there will be performance penalties as we've seen with other mitigations, like Spectre and Meltdown.
As we've seen at times with older systems, some might not be updated. It also appears that some impacted models don't yet have mitigations.
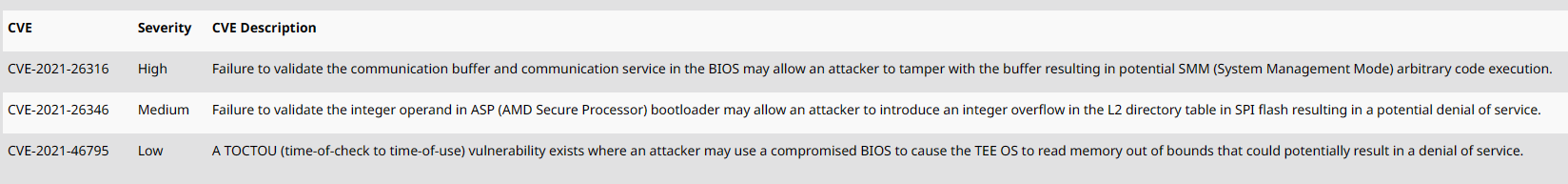
The vulnerabilities include three new variants for the consumer-geared Ryzen desktop PC, HEDT, Pro, and Mobile processors. One of the vulnerabilities is listed as high severity, while the other two are ranked as Medium or Low severity. These vulnerabilities can be exploited through either BIOS hacks or an attack on the AMD Secure Processor (ASP) bootloader.
The vulnerabilities span the Ryzen 2000-series Pinnacle Ridge desktop chips, along with the 2000- and 5000-series APU product lines that come with integrated graphics (Raven Ridge, Cezanne). In addition, AMD's Threadripper 2000- and 3000-series HEDT and Pro processors are also impacted, along with numerous Ryzen 2000-, 3000-, 5000-, 6000- and Athlon 3000-series mobile processors.
AMD has also listed 28 vulnerabilities for its EPYC processors, four of which are high severity. Three of the high-severity variants enable arbitrary code execution through various attack vectors, while one allows writing data to certain regions that can lead to loss of data integrity and availability. Researchers also unearthed 15 other vulnerabilities ranked as medium severity and nine low-severity vulnerabilities.
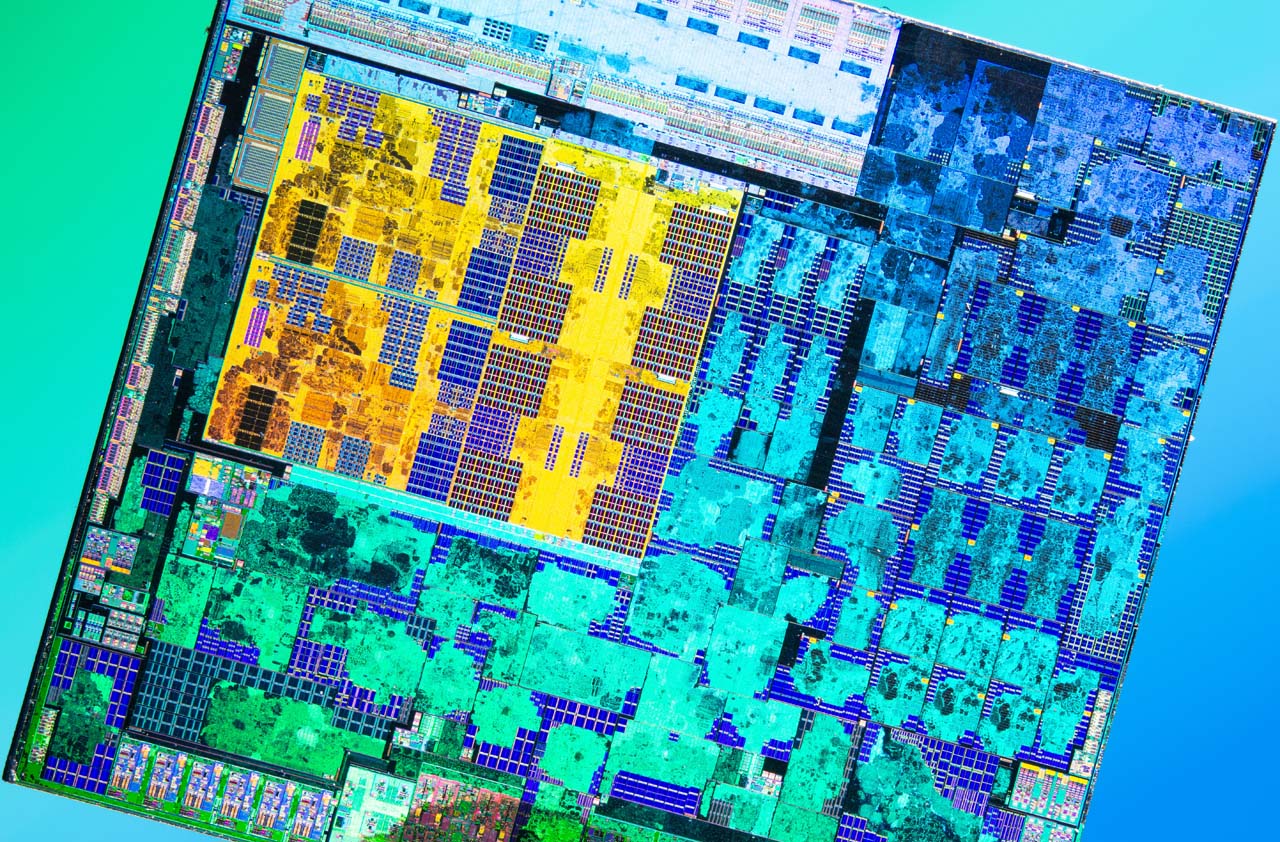
AMD's chips have long been known for having fewer known vulnerabilities than Intel's models. However, it's hard to ascertain if the initially limited discoveries in AMD processors were due to a security-first approach to hardened processor design, or if researchers and attackers merely focused on Intel's processors due to their commanding market share: Attackers almost always focus on the broadest cross-section possible.
As such, AMD's recent success in clawing away market share from Intel, especially in the security-focused data center market, will find researchers turning their eyes more toward AMD's architectures in search of potential security gaps. AMD has also had several other new vulnerability disclosures in the recent past, including a Meltdown-esque variant that requires software re-coding, along with Hertzbleed and Take A Way.
We're following up with AMD regarding several of the listings, as it appears that some processors don't have mitigations yet. Also, we're keen to learn more about any possible performance penalties.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Paul Alcorn is the Editor-in-Chief for Tom's Hardware US. He also writes news and reviews on CPUs, storage, and enterprise hardware.
-
YouFilthyHippo I'm not patching if there's a performance hit. If someone wants to hack my PC and steal all my memes, let them.Reply -
DavidLejdar No BIOS update available here yet.Reply
Yeah, sometimes it seems best to wait out an update for a bit, when it all works fine as is. But then again, in regard to malicious code, that can impact performance. I.e., if someone is stealing that perhaps even 1 TB of memes, that would take up quite some of the performance of your storage device and of your internet connection.YouFilthyHippo said:I'm not patching if there's a performance hit. If someone wants to hack my PC and steal all my memes, let them. -
USAFRet Reply
Or if someone wants to use your system to burn bitcoin, or host illegal content, or be part of a botnet.YouFilthyHippo said:I'm not patching if there's a performance hit. If someone wants to hack my PC and steal all my memes, let them.
All is good, right? -
Amdlova Amd has more breaches than intel... just don't have exploited. More user... more news...Reply -
drivinfast247 Reply
I don't think the kid playing Fortnite is their main concern. LolYouFilthyHippo said:I'm not patching if there's a performance hit. If someone wants to hack my PC and steal all my memes, let them. -
ohio_buckeye Well my ryzen pc is usually only on if I’m gaming. Other than that I shut it off. So I shouldn’t be effected either way.Reply -
Sleepy_Hollowed Outside the ones that don’t have much info, a chunk are resolved with the .7 firmware, then others with .8 but I think that’s new, not widely available.Reply
good on them to release it instead of leaving it to users to hunt individually, and Toms for listing this.