Tech Industry
Latest about Tech Industry
-
-
 PremiumAI is starting to out-design chip engineers in narrow areas as LLMs accelerate software chip design tool developmentBy Chris Stokel-Walker Published
PremiumAI is starting to out-design chip engineers in narrow areas as LLMs accelerate software chip design tool developmentBy Chris Stokel-Walker Published -
 Europol's Operation Saffron takes down privacy-focused First VPN serviceBy Bruno Ferreira Published
Europol's Operation Saffron takes down privacy-focused First VPN serviceBy Bruno Ferreira Published -
 Nvidia's memory costs soar 485%, latest AI systems now cost $7.8 million to buildBy Anton Shilov Published
Nvidia's memory costs soar 485%, latest AI systems now cost $7.8 million to buildBy Anton Shilov Published -
 EU forced to exempt banned Chinese chipmaker after auto industry warns of supply crisisBy Luke James Published
EU forced to exempt banned Chinese chipmaker after auto industry warns of supply crisisBy Luke James Published -
 Samsung reportedly set to distribute up to $26.6 billion to staff in AI-driven semiconductor bonuses after last-minute union dealBy Etiido Uko Published
Samsung reportedly set to distribute up to $26.6 billion to staff in AI-driven semiconductor bonuses after last-minute union dealBy Etiido Uko Published -
 PremiumThe custom AI ASIC state of play (May 2026) — Broadcom deals, Google TPUs, Meta MTIA & beyondBy Luke James Published
PremiumThe custom AI ASIC state of play (May 2026) — Broadcom deals, Google TPUs, Meta MTIA & beyondBy Luke James Published -
 AMD begins production ramp of 256-core EPYC VeniceBy Luke James Published
AMD begins production ramp of 256-core EPYC VeniceBy Luke James Published
-
Explore Tech Industry
Artificial Intelligence
-
-
 PremiumAI is starting to out-design chip engineers in narrow areas as LLMs accelerate software chip design tool developmentBy Chris Stokel-Walker Published
PremiumAI is starting to out-design chip engineers in narrow areas as LLMs accelerate software chip design tool developmentBy Chris Stokel-Walker Published -
 Nvidia's memory costs soar 485%, latest AI systems now cost $7.8 million to buildBy Anton Shilov Published
Nvidia's memory costs soar 485%, latest AI systems now cost $7.8 million to buildBy Anton Shilov Published -
 Nvidia no longer reports gaming GPU sales as a separate segmentBy Anton Shilov Last updated
Nvidia no longer reports gaming GPU sales as a separate segmentBy Anton Shilov Last updated -
 Russia's Sberbank wants Chinese chips for its GigaChat AI in the face of Western sanctionsBy Luke James Published
Russia's Sberbank wants Chinese chips for its GigaChat AI in the face of Western sanctionsBy Luke James Published -
 Pizza Hut's AI delivery system cooks up $100 million franchisee lawsuitBy Bruno Ferreira Published
Pizza Hut's AI delivery system cooks up $100 million franchisee lawsuitBy Bruno Ferreira Published -
 Jury throws out Elon Musk's lawsuit against OpenAI after less than two hours of deliberationBy Luke James Published
Jury throws out Elon Musk's lawsuit against OpenAI after less than two hours of deliberationBy Luke James Published -
 College students drown out AI-praising commencement speeches with boosBy Ben Stockton Published
College students drown out AI-praising commencement speeches with boosBy Ben Stockton Published -
 China bypasses US GPU bans with 1.54-exaflops 'LineShine' supercomputerBy Anton Shilov Last updated
China bypasses US GPU bans with 1.54-exaflops 'LineShine' supercomputerBy Anton Shilov Last updated -
 LinkedIn recruitment spam becomes Olde English prose after user hides AI prompt injection in bioBy Mark Tyson Last updated
LinkedIn recruitment spam becomes Olde English prose after user hides AI prompt injection in bioBy Mark Tyson Last updated
-
Big Tech
-
-
 Samsung reportedly set to distribute up to $26.6 billion to staff in AI-driven semiconductor bonuses after last-minute union dealBy Etiido Uko Published
Samsung reportedly set to distribute up to $26.6 billion to staff in AI-driven semiconductor bonuses after last-minute union dealBy Etiido Uko Published -
 Angry tiny Texas town council member proposes total ban on cellular and GPS devices in protest over AI disputeBy Jowi Morales Published
Angry tiny Texas town council member proposes total ban on cellular and GPS devices in protest over AI disputeBy Jowi Morales Published -
 Samsung narrowly avoids 18-day chip strike after last-minute wage deal with 48,000-worker unionBy Etiido Uko Published
Samsung narrowly avoids 18-day chip strike after last-minute wage deal with 48,000-worker unionBy Etiido Uko Published -
 Samsung and SK Hynix employees are reportedly abandoning overseas training programs to qualify for performance bonusesBy Etiido Uko Published
Samsung and SK Hynix employees are reportedly abandoning overseas training programs to qualify for performance bonusesBy Etiido Uko Published -
 US FTC reportedly launches antitrust probe into Arm following its launch of its own AGI CPUBy Jowi Morales Published
US FTC reportedly launches antitrust probe into Arm following its launch of its own AGI CPUBy Jowi Morales Published -
 Texas county passes data center ban for rural areas for a year, move comes in wake of AI data centers moving to remote areas to skirt regulationsBy Jowi Morales Published
Texas county passes data center ban for rural areas for a year, move comes in wake of AI data centers moving to remote areas to skirt regulationsBy Jowi Morales Published -
 Pennsylvania residents complain they are being 'bulldozed' over AI data center concernsBy Jowi Morales Published
Pennsylvania residents complain they are being 'bulldozed' over AI data center concernsBy Jowi Morales Published -
 Intel announces McLaren F1 partnership, will battle AMD-powered MercedesBy Mark Tyson Published
Intel announces McLaren F1 partnership, will battle AMD-powered MercedesBy Mark Tyson Published -
 70% of Americans oppose data centers near their homes, now less popular than nuclear power plantsBy Jowi Morales Published
70% of Americans oppose data centers near their homes, now less popular than nuclear power plantsBy Jowi Morales Published
-
Cryptocurrency
-
-
 Korean funeral services company loses $33 million in secret crypto bet against EthereumBy Hassam Nasir Published
Korean funeral services company loses $33 million in secret crypto bet against EthereumBy Hassam Nasir Published -
 Physical attacks against crypto holders, including kidnap and assault, up 75% in 2025By Jowi Morales Published
Physical attacks against crypto holders, including kidnap and assault, up 75% in 2025By Jowi Morales Published -
 Bitcoin trader recovers $400,000 using Claude AI after losing wallet password 11 years agoBy Jowi Morales Last updated
Bitcoin trader recovers $400,000 using Claude AI after losing wallet password 11 years agoBy Jowi Morales Last updated -
 Tennessee bans crypto ATMs that have become 'payment portal of choice for scammers'By Jowi Morales Published
Tennessee bans crypto ATMs that have become 'payment portal of choice for scammers'By Jowi Morales Published -
 Crypto scam takes advantage of Strait of Hormuz crisis by taking fake payments, leading to two ships being fired uponBy Jowi Morales Published
Crypto scam takes advantage of Strait of Hormuz crisis by taking fake payments, leading to two ships being fired uponBy Jowi Morales Published -
 Inventor showcases 3D printer filament dryer that mines Bitcoins and dries filament with waste heat, capable of 6 TH/sBy Mark Tyson Published
Inventor showcases 3D printer filament dryer that mines Bitcoins and dries filament with waste heat, capable of 6 TH/sBy Mark Tyson Published -
 British cryptographer Adam Back is the secret creator of Bitcoin, claims new reportBy Hassam Nasir Published
British cryptographer Adam Back is the secret creator of Bitcoin, claims new reportBy Hassam Nasir Published -
 Crypto platform Drift suffers from hack suspected to total $270 millionBy Jowi Morales Published
Crypto platform Drift suffers from hack suspected to total $270 millionBy Jowi Morales Published -
 Hacker charged for stealing $53 million in crypto, faces up to 30 years in prisonBy Jowi Morales Published
Hacker charged for stealing $53 million in crypto, faces up to 30 years in prisonBy Jowi Morales Published
-
Cybersecurity
-
-
 Europol's Operation Saffron takes down privacy-focused First VPN serviceBy Bruno Ferreira Published
Europol's Operation Saffron takes down privacy-focused First VPN serviceBy Bruno Ferreira Published -
 Hacker group hits 3,800 internal GitHub repositories via poisoned developer pluginBy Etiido Uko Published
Hacker group hits 3,800 internal GitHub repositories via poisoned developer pluginBy Etiido Uko Published -
 First Apple M5 memory exploit discovered using Anthropic AI, gives root access on MacOSBy Bruno Ferreira Published
First Apple M5 memory exploit discovered using Anthropic AI, gives root access on MacOSBy Bruno Ferreira Published -
 Microsoft BitLocker-protected drives can now be opened with just some files on a USB stickBy Bruno Ferreira Published
Microsoft BitLocker-protected drives can now be opened with just some files on a USB stickBy Bruno Ferreira Published -
 Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infectionBy Etiido Uko Published
Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infectionBy Etiido Uko Published -
 90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacksBy Bruno Ferreira Published
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacksBy Bruno Ferreira Published -
 Google cybersecurity boffins found at least one AI-developed zero-day exploitBy Bruno Ferreira Published
Google cybersecurity boffins found at least one AI-developed zero-day exploitBy Bruno Ferreira Published -
 Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning givenBy Bruno Ferreira Published
Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning givenBy Bruno Ferreira Published -
 College student hacks Taiwan high-speed rail line, stopping four trainsBy Bruno Ferreira Published
College student hacks Taiwan high-speed rail line, stopping four trainsBy Bruno Ferreira Published
-
Manufacturing
-
-
 PremiumThe custom AI ASIC state of play (May 2026) — Broadcom deals, Google TPUs, Meta MTIA & beyondBy Luke James Published
PremiumThe custom AI ASIC state of play (May 2026) — Broadcom deals, Google TPUs, Meta MTIA & beyondBy Luke James Published -
 AMD begins production ramp of 256-core EPYC VeniceBy Luke James Published
AMD begins production ramp of 256-core EPYC VeniceBy Luke James Published -
 Intel kicks off development on next-decade 10A and 7A process technologiesBy Anton Shilov Published
Intel kicks off development on next-decade 10A and 7A process technologiesBy Anton Shilov Published -
 PremiumSMIC founder and AMEC CEO urge Chinese fabs to test domestic chipmaking tools on active production linesBy Luke James Published
PremiumSMIC founder and AMEC CEO urge Chinese fabs to test domestic chipmaking tools on active production linesBy Luke James Published -
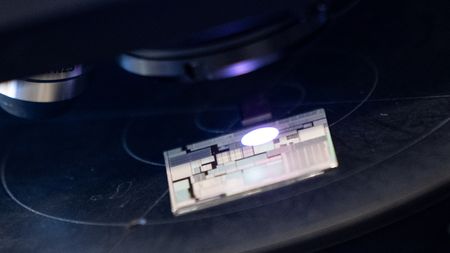
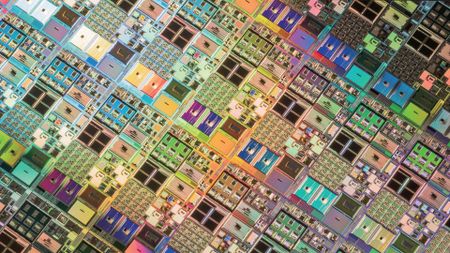
 Russia’s Mikron is selling framed test wafers with up to 120,000 processors as souvenirsBy Mark Tyson Published
Russia’s Mikron is selling framed test wafers with up to 120,000 processors as souvenirsBy Mark Tyson Published -
 Trump calls $14 billion Taiwan arms deal a 'negotiating chip' with China after Xi said Taiwan issue could lead to 'clashes and even conflicts'By Luke James Published
Trump calls $14 billion Taiwan arms deal a 'negotiating chip' with China after Xi said Taiwan issue could lead to 'clashes and even conflicts'By Luke James Published -
 PremiumLeading-edge foundry roadmaps for TSMC, Intel and Samsung — outlining the path to 1.4nm nodes and beyondBy Anton Shilov Published
PremiumLeading-edge foundry roadmaps for TSMC, Intel and Samsung — outlining the path to 1.4nm nodes and beyondBy Anton Shilov Published -
 TSMC allocates $20 billion to Arizona expansionBy Anton Shilov Published
TSMC allocates $20 billion to Arizona expansionBy Anton Shilov Published -
 NASA partners with Microchip to build next-generation spaceflight chips with 100x the power of current offeringsBy Jowi Morales Published
NASA partners with Microchip to build next-generation spaceflight chips with 100x the power of current offeringsBy Jowi Morales Published
-
Quantum Computing
-
-
 China's Hanyuan-2 debuts as 'world's first' dual-core quantum computerBy Luke James Published
China's Hanyuan-2 debuts as 'world's first' dual-core quantum computerBy Luke James Published -
 PremiumQuantum photonics roadmap — how Xanadu and PsiQuantum are looking to transfer qubits through beams of lightBy Francisco Pires Published
PremiumQuantum photonics roadmap — how Xanadu and PsiQuantum are looking to transfer qubits through beams of lightBy Francisco Pires Published -
 PremiumThe future of Quantum computing — the tech, companies, and roadmaps that map out a coherent quantum futureBy Francisco Pires Published
PremiumThe future of Quantum computing — the tech, companies, and roadmaps that map out a coherent quantum futureBy Francisco Pires Published -
 Quantum computing firm dangles $22,500 Bitcoin prizeBy Mark Tyson Published
Quantum computing firm dangles $22,500 Bitcoin prizeBy Mark Tyson Published -
 PremiumIBM and Cisco agree to lay the foundations for a quantum internetBy Luke James Published
PremiumIBM and Cisco agree to lay the foundations for a quantum internetBy Luke James Published -
 New Chinese optical quantum chip allegedly 1,000x faster than Nvidia GPUs for processing AI workloadsBy Aaron Klotz Published
New Chinese optical quantum chip allegedly 1,000x faster than Nvidia GPUs for processing AI workloadsBy Aaron Klotz Published -
 IBM's boffins run a nifty quantum error-correction algorithm on conventional AMD FPGAsBy Bruno Ferreira Published
IBM's boffins run a nifty quantum error-correction algorithm on conventional AMD FPGAsBy Bruno Ferreira Published -
 Trump administration to follow up Intel stake with investment in quantum computing, report claimsBy Anton Shilov Published
Trump administration to follow up Intel stake with investment in quantum computing, report claimsBy Anton Shilov Published -
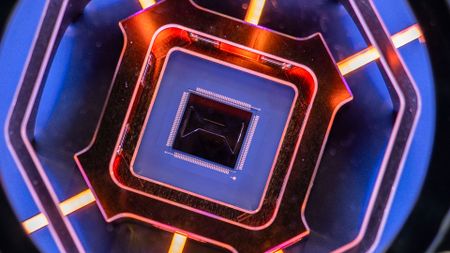
 Google's Quantum Echo algorithm shows world's first practical application of Quantum Computing — Willow 105-qubit chip runs algorithm 13,000x faster than a supercomputerBy Bruno Ferreira Published
Google's Quantum Echo algorithm shows world's first practical application of Quantum Computing — Willow 105-qubit chip runs algorithm 13,000x faster than a supercomputerBy Bruno Ferreira Published
-
Supercomputers
-
-
 Elon Musk restarts Dojo3 'space' supercomputer project as AI5 chip design gets in 'good shape'By Aaron Klotz Published
Elon Musk restarts Dojo3 'space' supercomputer project as AI5 chip design gets in 'good shape'By Aaron Klotz Published -
 AMD and Eviden unveil Europe's second exascale systemBy Anton Shilov Published
AMD and Eviden unveil Europe's second exascale systemBy Anton Shilov Published -
 Nvidia to build seven AI supercomputers for the U.S. gov't with over 100,000 Blackwell GPUsBy Anton Shilov Published
Nvidia to build seven AI supercomputers for the U.S. gov't with over 100,000 Blackwell GPUsBy Anton Shilov Published -
 Nvidia unveils Vera Rubin supercomputers for Los Alamos National LaboratoryBy Anton Shilov Published
Nvidia unveils Vera Rubin supercomputers for Los Alamos National LaboratoryBy Anton Shilov Published -
 U.S. Department of Energy and AMD cut a $1 billion deal for two AI supercomputersBy Bruno Ferreira Published
U.S. Department of Energy and AMD cut a $1 billion deal for two AI supercomputersBy Bruno Ferreira Published -
 China's supercomputer breakthrough uses 37 million processor cores to model complex quantum chemistry at molecular scaleBy Anton Shilov Last updated
China's supercomputer breakthrough uses 37 million processor cores to model complex quantum chemistry at molecular scaleBy Anton Shilov Last updated -
 Start-up hails world's first quantum computer made from standard siliconBy Luke James Published
Start-up hails world's first quantum computer made from standard siliconBy Luke James Published -
 Nvidia GPUs and Fujitsu Arm CPUs will power Japan's next $750M zetta-scale supercomputerBy Hassam Nasir Published
Nvidia GPUs and Fujitsu Arm CPUs will power Japan's next $750M zetta-scale supercomputerBy Hassam Nasir Published -
 AMD's massive GPU VRAM on its Instinct cards has broken Linux's hibernation featureBy Hassam Nasir Published
AMD's massive GPU VRAM on its Instinct cards has broken Linux's hibernation featureBy Hassam Nasir Published
-
Superconductors
-
-
 New 3D printing process could improve superconductorsBy Ash Hill Published
New 3D printing process could improve superconductorsBy Ash Hill Published -
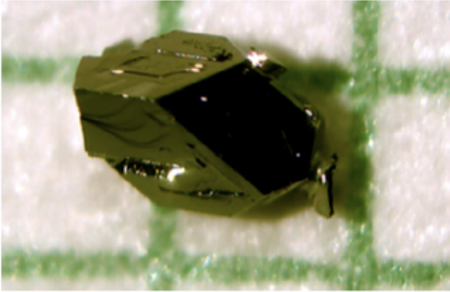 New research shows naturally occurring mineral is an 'unconventional superconductor' when purifiedBy Christopher Harper Published
New research shows naturally occurring mineral is an 'unconventional superconductor' when purifiedBy Christopher Harper Published -
 New research reignites the possibility of LK-99 room-temperature superconductivityBy Francisco Pires Published
New research reignites the possibility of LK-99 room-temperature superconductivityBy Francisco Pires Published -
 U.S. Govt and researchers seemingly discover new type of superconductivity in an exotic, crystal-like materialBy Francisco Pires Published
U.S. Govt and researchers seemingly discover new type of superconductivity in an exotic, crystal-like materialBy Francisco Pires Published -
 Nature Retracts Controversial Room Temperature Superconductor Paper (But Not LK-99)By Francisco Pires Published
Nature Retracts Controversial Room Temperature Superconductor Paper (But Not LK-99)By Francisco Pires Published -
 What is a Superconductor?By Francisco Pires Published
What is a Superconductor?By Francisco Pires Published -
 MIT's Superconducting Qubit Breakthrough Boosts Quantum PerformanceBy Francisco Pires Published
MIT's Superconducting Qubit Breakthrough Boosts Quantum PerformanceBy Francisco Pires Published -
 LK-99 Research Continues, Paper Says Superconductivity Could be PossibleBy Francisco Pires Published
LK-99 Research Continues, Paper Says Superconductivity Could be PossibleBy Francisco Pires Published -
 Is LK-99 a Superconductor After All? New Research and Updated Patent Say SoBy Francisco Pires Published
Is LK-99 a Superconductor After All? New Research and Updated Patent Say SoBy Francisco Pires Published
-
