'Five Eyes' Governments Planned To Hack Google's App Store To Send Malware To Users
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
According to new findings in Snowden's documents, the "Five Eyes" nations, which includes the U.S., UK, Canada, Australia and New Zealand planned to hack Google's mobile app store in order to infect Android smartphone users with malware.
The documents showing the project are dated between November 2011 and February 2012, so it's possible the intelligence agencies have succeeded in their goals, or at least they may have until Google implemented stronger security measures in 2013 when it found out its whole network was hacked by the NSA.
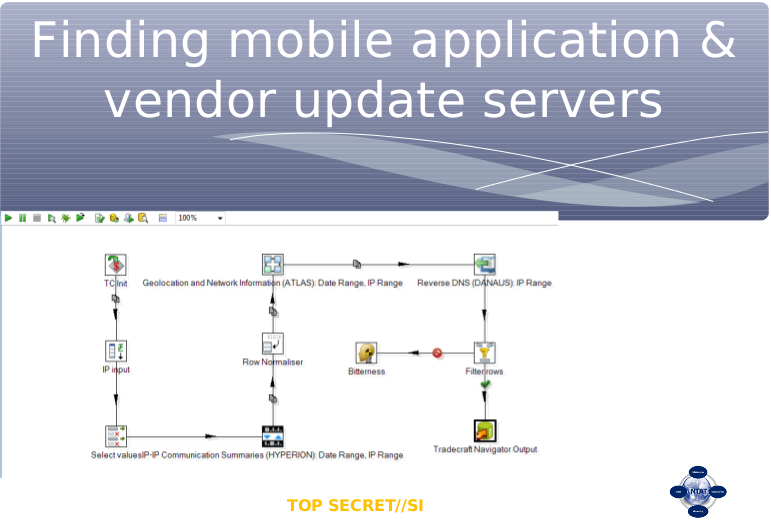
The agencies used a spying program called XKEYSCORE that seems to appear again and again in such revelations. This is a "passive surveillance" program that captures (mainly unencrypted) Internet traffic that passes through cables, which are tapped by the NSA and other Five Eyes agencies.
Article continues belowAfter the program identified which traffic represents user connections to Google's app store, the agencies could then use other programs such as IRRITANT HORN to break those connections and send their own malware to the agencies' targets. The malware, or "implants," would then grab sensitive information from smartphones such as emails, texts, web history, call records, videos, photos or other files.
It seems the main motivation for grabbing this kind of information was to avoid being blindsided in case an Arab Spring-like mass unrest happened again in the Middle East or Africa. This is why the agencies focused on Senegal, Sudan and the Republic of the Congo, at least at the time. However, the agencies also used the same programs to hack targets from France, Cuba, Morocco, Switzerland, the Bahamas, the Netherlands and Russia.
Within the same project, the agencies also managed to exploit some major vulnerabilities within Alibaba's UC Browser, a popular web browser in China and India used by half a billion people. The UC Browser was leaking information such as users' search queries, phone numbers and UIDs that can be used to track people, as well as location information protected by encryption that could easily be broken with publicly available tools.
Citizen Lab, a human rights and technology research group, contacted Alibaba last month, and the company has since fixed these security issues with an update launched on May 15. Alibaba said it has found no evidence that customer data has been leaked, although it's unlikely the surveillance of this data could have been detected.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
According to Citizen Lab Director Ron Deibert, this vulnerability could have been used by criminals as well, which makes the agencies' decision not to disclose the vulnerability reckless from a cybersecurity point of view.
"Of course, the security agencies don't [disclose the information]," Deibert said. "Instead, they harbor the vulnerability. They essentially weaponize it." Taking advantage of weaknesses in apps like UC Browser "may make sense from a very narrow national security mindset," Deibert added, "but it's at the expense of the privacy and security of hundreds of millions of users worldwide."
Last year, Snowden's documents also showed that the NSA likes to masquerade as Facebook servers in order to send malware to hack into the users' computers, so Google's app store isn't the only target of such kind. Both reports also deal with information that is a few years old, so more companies could be affected by this sort of attack.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
merikafyeah More and more reasons why Snowden was and is a hero. Without him we may have never learned about so much fvckery happening behind the scenes that even our fiction fails to horrify as much as plain reality does. The real traitors are those subverting the constitution and spying on anyone and everyone without any real oversight or control.Reply -
cats_Paw ReplyPlanned? How do we they haven't already succeeded?
They already have... NSA has malware in almost every HDD on the planet, Russia had a VIrus in the USA Stock Exchange... what is a weak APP for them?
If you got some secret plans to dominate the world or enslave humanity, you might be smart NOT TO TALK about it.
And that is true in E-Mail, normal Mail, or person to person conversation.
Oh and.... If you ahve any Private photos, keep them on a separate PC, that you never connect to the Internet or your phone... -
vir_cotto ReplyIf you ahve any Private photos, keep them on a separate PC, that you never connect to the Internet or your phone...
You forget about Howler Monkey though, even if you have them connected to nothing if they have implanted this device they will be able to access it anyways! Howler Monkey is old tech too, I'm sure they have improved and shrunk it down!
"HOWLERMONKEY is a custom Short to Medium range implant RF Transceiver. It is used in conjunction with a digital core to provide a complete implant" -
jimmysmitty Reply15905648 said:More and more reasons why Snowden was and is a hero. Without him we may have never learned about so much fvckery happening behind the scenes that even our fiction fails to horrify as much as plain reality does. The real traitors are those subverting the constitution and spying on anyone and everyone without any real oversight or control.
Only in the US does the constitution even apply. Anywhere else, well a lot of other countries are base on much older laws so civilians don't have as many supposed rights.
And while I would agree with you that what is being done is wrong, the one problem I have with Snowden is that some of the information he revealed put peoples lives at risk, even people who are doing only what they are told.
Either way, what he did will change nothing. People will eventually forget about it and move on and the same thing will happen again. Hell I don't think the majority of Americans even care. Look at how openly they use the internet and post/send pictures. Sending a picture via text means it will be on a server somewhere forever. It doesn't just go from phone to phone. Even the text messages are there. Same with emails.