Fake Cell Towers Could Be Attacking Your Cellphone Up To 80-90 Times Per Hour
If you have a phone that isn’t a CryptoPhone 500 and live in the U.S., you’re likely to have your phone “attacked” by an “IMSI catcher” up to 80-90 times per hour, according to ESD America, the company promoting the CryptoPhone 500 in the U.S. The CryptoPhone is a security-"hardened" Galaxy S3 device, and the company has removed 468 vulnerabilities removed from the stock operating system.
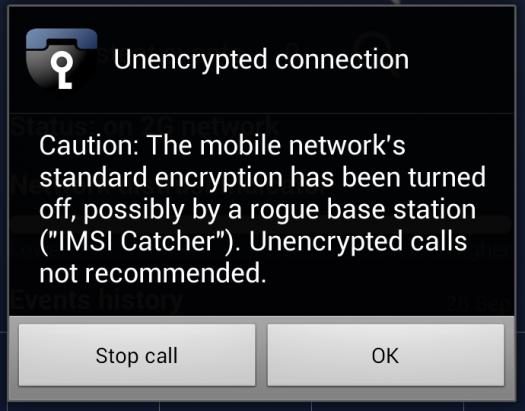
An IMSI catcher is a device that acts as a fake cell tower and forces your phone to connect to it when in range, gaining access to much of your communications (including SMS, voice and video-calls) because of vulnerabilities in the baseband software of the device and poor encryption algorithms.
The 2G network is by far the most vulnerable, using three-decades-old encryption algorithms that can be decrypted on the fly, but the new IMSI catchers being sold by private companies to authorities in the U.S. also promise to acquire access to 3G, and even the more recent 4G networks, which are supposed to have much better security.
Article continues belowGSMK, the German company making an ultra-secure Android-based smartphone meant to foil surveillance by governments or anyone else, says it detected 17 such fake cell towers in the U.S. on a casual drive through the country.
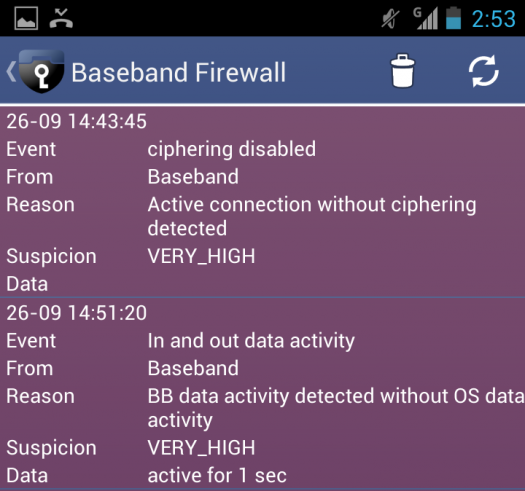
Most of the attacks from these fake cell towers happen against the baseband processor of the phones. The software for these baseband processors is usually just a proprietary black box that doesn’t allow anyone to see what’s happening inside other than the company making the baseband processor or hackers who have found vulnerabilities in it.
GSMK has developed a baseband firewall technology for the CryptoPhone’s baseband processor that allows the phone to catch all attacks from fake cell towers and block them. While the CryptoPhone 500 was able to block these attacks, an iPhone and a Galaxy S4 couldn’t, and in fact didn’t even know the attacks were happening in the first place:
”As we drove by, the iPhone showed no difference whatsoever. The Samsung Galaxy S4, the call went from 4G to 3G and back to 4G. The CryptoPhone lit up like a Christmas tree,” ESD America CEO Les Goldsmith told PopSci.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
A phone like CryptoPhone doesn’t come cheap, though. GSMK sells each unit for $3,500, which obviously most people can't afford. The next best thing these days in terms of a secure phone is the Blackphone. However, so far the Blackphone doesn’t provide anything that protects against baseband attacks. If the attackers can get inside the phone through the baseband OS, then it won’t matter much if the communication is encrypted.
Phones like CryptoPhone 500 or Blackphone usually end up being used by companies or government officials rather than regular individuals, so to make sure most people’s communications are protected by default (rather than vulnerable by default), we need companies like Google, Apple and Microsoft to stand behind their users and add similar protections to all the phones using their platforms.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
koga73 I believe this mainly affects GSM networks such as AT&T and T-Mobile. The encryption between your phone and tower is completely controlled by the tower so it's easy enough for a fake tower to disable encryption. Your phone will naturally connect to the fake tower if it's closer. The fake tower has the ability to intercept communications as well as push firmware / software updates to your phone. For more info look at Defcon 18 - Practical Cellphone SpyingReply -
Vorador2 ReplyHackers everywhere are thinking, Why didn't I think of that?
Because it's not cheap. Those IMSI catchers start from 3k up to 100k, and have a limited range.
It's much cheaper to use social engineering. People are dumb, and are willing to install "Free Whatsapp with themes!!" way too easily. -
f-14 most of these fake towers operated by the american government are turned off unless there is an imminent threat to national security, then big brother starts screening calls.Reply
so if some of these towers are on, it's because there's a legitimate threat going on near you. minneapolis and saint paul are specifically being monitored right now that i know of, with possible kansas city los angels and new york city.
the ISIS/ISIL threats are being taken seriously. -
f-14 oh, i don't know that the fake ones in detroit were ever turned off since 9/11, but i do know they can pick up all the way into torontoReply -
junkeymonkey turned off, that's funny -- leave on collect data sell data to pay back project or invest in more towers onr thing you got to remember is that with a hard line = require a warrant on the air waves = free for allReply -
bob9951 Bring on those gov'mint false towers! I got nothing to hide and I don't want me or my friends blown up in the next ISIS attack attempt.Reply -
bob9951 Sorry about your privacy but ... F you for thinking it's more important than my safety. Some of us are actually the terrorists.Reply