iOS Default Hotspot Passwords Cracked in Less Than a Minute
iOS tethering password can be cracked in under 1 minute, but it requires four very expensive graphics cards.
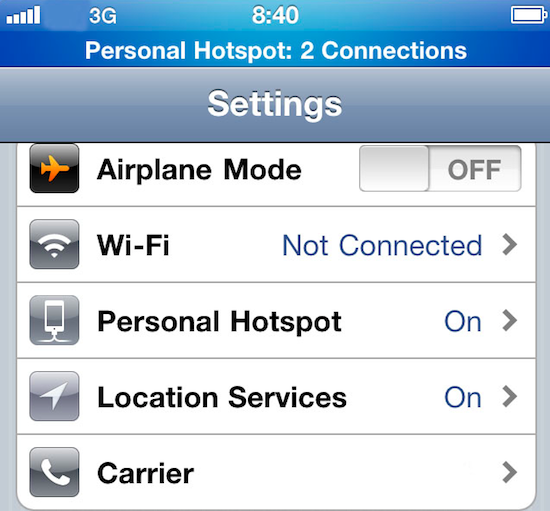
Anyone who has an iPhone or iPad has probably noticed the interesting passwords that iOS managed to generate for its tethering hotspots. It now appears that the collection of words consists of about 52,500 entries, and as true random generation is not possible where computers are concerned, it means that the words and numbers count must be cracked backwards to decipher the security generation algorithm. And that is precisely what happened.
Three German researchers from FAU (Friedrich-Alexander-Universität) acquired a WiFi connection created by iOS, and then they set an AMD Radeon HD 6990 GPU to work trying to crack it. After taking only 50 minutes to get in with brute force, the researchers subsequently realized that only a handful (1,842) of the short English words were actually being used, and were able to streamline a cracking algorithm for the process. Now using four AMD Radeon HD 7970 GPUs, they can crack a default generated password in a mere 50 seconds. The reasoning behind using a GPU is that, while CPUs have faster speeds over fewer cores, most GPUs have over 300 cores that allow incredibly parallel processing power for graphics and evidently brute force attacks as well.
Now before we start freaking out, let's just realize that most people don't walk around with $1,600 worth of graphics cards in their pockets, along with a 1,200 watt rated battery to power it all for long enough to coincidentally find an iOS tethering point and crack it. That being said, it does raise an important security issue of not only changing your default passwords, but also that commercially used password generation needs to step up its game with more complexity and length of its passwords. And, to be fair to Apple, at least it attempted a password generation technique, unlike some companies who have a single standard password all the time.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Tom's Hardware is the leading destination for hardcore computer enthusiasts. We cover everything from processors to 3D printers, single-board computers, SSDs and high-end gaming rigs, empowering readers to make the most of the tech they love, keep up on the latest developments and buy the right gear. Our staff has more than 100 years of combined experience covering news, solving tech problems and reviewing components and systems.
-
abrzezi2 You could use your phone to ssh into your home or work HPC and use that to crack the password. A few minutes later you'll be hooked up on somebody else's hotspot.Reply -
greghome ReplyAnyone who has an iPhone or iPad has probably noticed the interesting passwords that iOS managed to generate for its tethering hotspots.
The iPad has hotspot ? -
Killroyjenkins Reply11010206 said:Anyone who has an iPhone or iPad has probably noticed the interesting passwords that iOS managed to generate for its tethering hotspots.
The iPad has hotspot ?
They have cell radios and are sold with data plans.
This title is rather misleading. Sensationalism I guess. -
patrik kasten I hope that problem will be resolved before the release of the <a href="http://iphone5-fr.com/?rel=ugc" >iphone 5s</a>Reply