Welcome to Your Worst Malware Nightmare
Spyware Defined
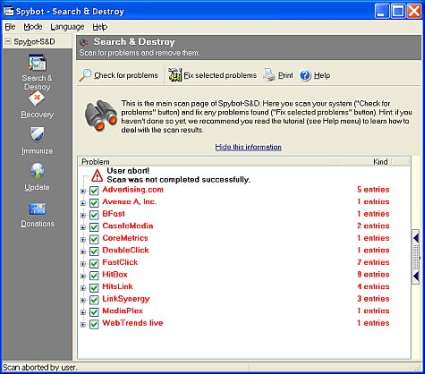
Spybot Search&Destroy combats spyware
The term spyware conjures mental images of rogue cold war agents veiled in secrecy subverting control of communications equipment to fulfill some evil agenda. Perhaps this was the original intent of whoever first introduced the term to computer culture but its use came to term around the mid 1990s. Today we know spyware as the catch-all term to categorize any sort of software program that monitors, collects and distributes information without explicit permission, knowledge or invocation.
Observable aspects of spyware infestation include:
- personal Web or email client settings change unexpectedly
- unwanted accessories or tool bars appear spontaneously
- unsolicited advertisements crop up at random
Some less savory and less apparent aspects of spyware behavior include:
- targeted data harvesting to collect personal or financial data
- secretive backdoor capability to allow surreptitious reentry
- complete or partial remote control over the infected computer
The Effects Of Spyware
Spyware is a costly form of malware, both in terms of time and money spent resolving the problems it causes. Most spyware is commercially produced and distributed, which explains why it has become such a pervasive form of malware. Ultimately, spyware can take away more than just time or money from infested end-users. Certain types of spyware are designed to steal ad revenue from legitimate sites or modify search queries by redirecting them to channels specified by the spyware's creator.
The various forms and implementations of spyware range from the generally frowned-upon to the outright illegal. A presumably benign form may collect statistical data on Website visits for marketing purposes - perhaps to formulate better target demographics for an upcoming campaign of adware or spam solicitations. Another form of spyware collects more than just statistical data, and harvests financial information, bank and credit card numbers, logon credentials and other personal information to redistribute to third-parties with bad intent. Ouch!
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Tom's Hardware is the leading destination for hardcore computer enthusiasts. We cover everything from processors to 3D printers, single-board computers, SSDs and high-end gaming rigs, empowering readers to make the most of the tech they love, keep up on the latest developments and buy the right gear. Our staff has more than 100 years of combined experience covering news, solving tech problems and reviewing components and systems.