FIDO Alliance Wants European Payments Industry To Use Its Own Modern Authentication Protocols
Recently, the FIDO Alliance, which designs and develops strong authentication protocols, criticized the European Commission (EC) for proposing that a non-secure “screen scraping” protocol be introduced in the upcoming regulation for payments services, called the Payment Services Directive 2 (PSD2).
The EC wanted to allow this protocol to be used at the request of financial technology (fintech) companies as a fallback option until banks adopt more secure protocols. However, FIDO warned that because this protocol would essentially become part of a new EU directive, companies will continue to use it for many years, even after all the banks adopt the stronger authentication methods. This situation could potentially expose millions of banking customers to financial theft.
FIDO’s Own Proposal
The main purpose for the creation of the FIDO Alliance was to design and develop strong authentication protocols that can be used in any device, and easily by their users. FIDO is now encouraging the banking and payments industry to adopt these protocols, too.
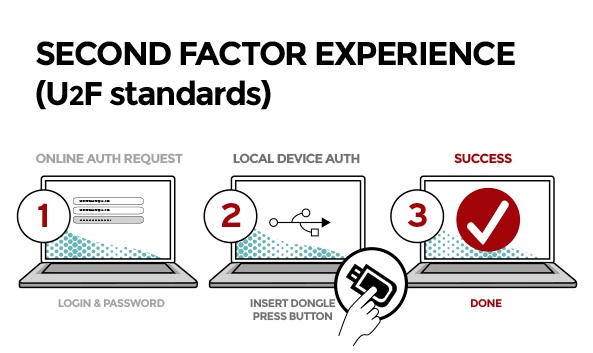
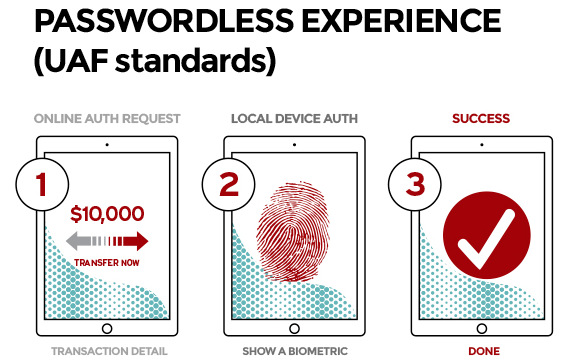
Article continues belowThe PSD2 regulation normally requires two secure and distinct factors of authentication to payment services. However, it also recognizes that a single device could also house two different factors at the same time, as long as “separate secure execution environments” such as trusted execution environments (TEEs), secure elements (SEs), or trusted platform modules (TPMs) are used.
FIDO argues that many devices already comply with this requirement and also use biometric authentication, which means that the payments industry could already implement support for FIDO’s existing authentication protocols in their payment applications.
Any organization can use the FIDO authentication protocols freely. Banks and payment service providers can also accept FIDO-compliant devices on the market. All FIDO-certified products are interoperable, so a user could use FIDO authentication inside a browser, via a security key, or with a smartphone.
A More Modern Authentication Solution
The FIDO Alliance believes that it offers a “best of both worlds” solution to multi-factor authentication. First of all, the FIDO authentication protocols are based on public key cryptography, which means that users don’t have to store credentials on a third-party server that can be hacked in one massive data breach or another. They only have to store a private key safely, which can be either on a secure hardware token, such a Yubikey, or in the SE/TEE/TPM of a laptop or smartphone.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
FIDO is also addressing the usability problem with authentication by supporting biometric authentication in its protocols. Additionally, FIDO’s biometric protocols have privacy built in so that the biometric data is never shared when used, but is always kept on the local device.
If adopted on a large scale, including by the banking and payments industry, the FIDO protocols could save us from having to deal with alternative biometric protocols that may store everyone’s fingerprint data or facial profiles in a centralized database. These solutions are typically used by governments right now, and they are at great risk of exposing everyone’s biometric data, if hacked.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.