Thermal Cameras and Machine Learning Combine to Snoop Out Passwords
AI-driven ‘thermal attack’ analyzes touch-input heat signature after you have gone.
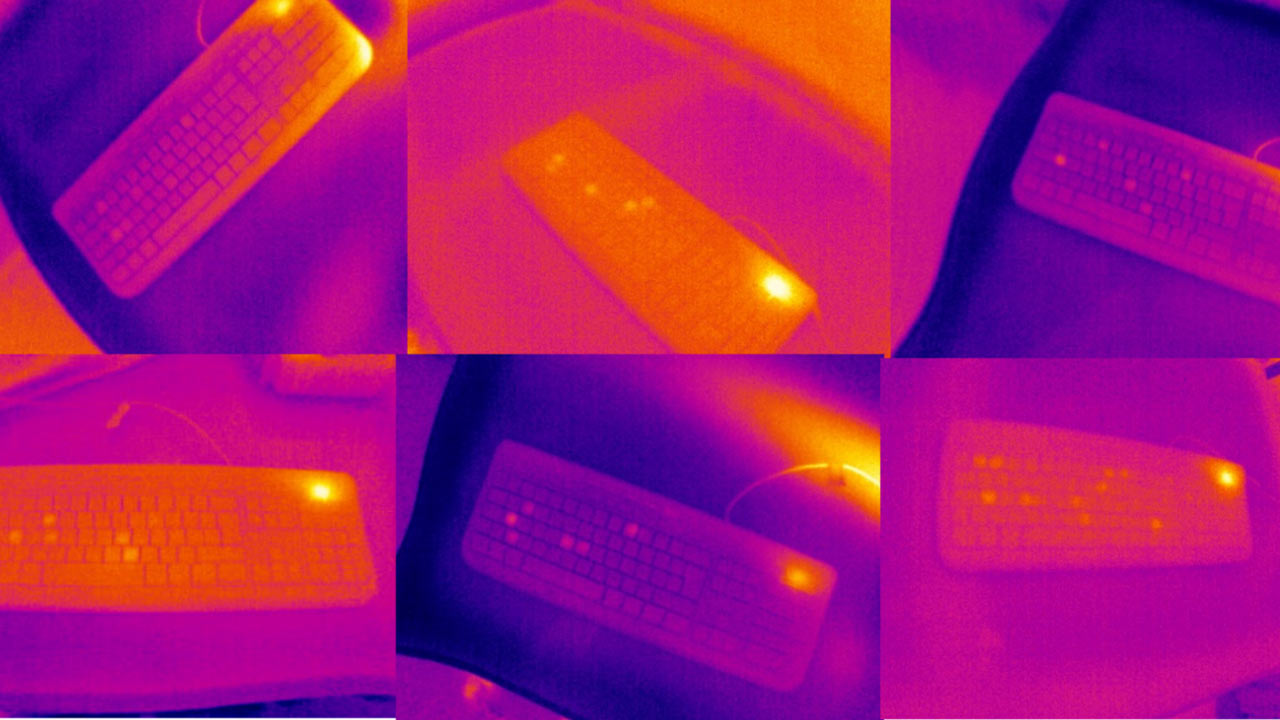
Researchers at the University of Glasgow have published a paper that highlights their so-called ThermoSecure implementation for discovering passwords and PINs. The name ThermoSecure provides a clue to the underlying methodology, as the researchers are using a mix of thermal imaging technology and AI to reveal passwords from input devices like keyboards, touchpads, and even touch screens.
Before looking at the underlying techniques and technology, it's worth highlighting how impressive ThermoSecure is for uncovering password inputs. During tests, the research paper states: "ThermoSecure successfully attacks 6-symbol, 8-symbol, 12-symbol, and 16-symbol passwords with an average accuracy of 92%, 80%, 71%, and 55% respectively." Moreover, these results were from relatively ‘cold’ evidence, and the paper adds that "even higher accuracy [is achieved] when thermal images are taken within 30 seconds."
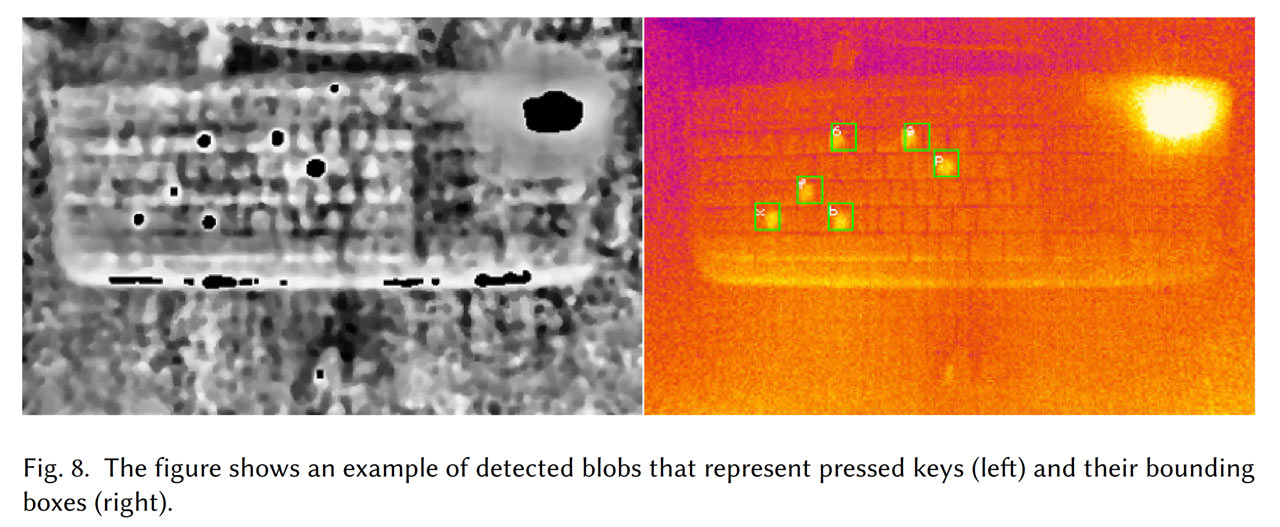
How does ThermoSecure work? The system needs a thermal camera, which is becoming a much more affordable item in recent years. A usable device may only cost $150, according to the research paper. On the AI software side of things, the system uses an object detection technique based on Mask RCNN that basically maps the (thermal) image to keys. Across three phases, variables like keyboard localization are considered, then key entry and multi-press detection is undertaken, then the order of the key presses is determined by algorithms. Overall it appears to work pretty well, as the results suggest.
Hunt-and-Peck Typists Become the Hunted
With the above thermal attack looking quite viable option for hackers to spy passwords, PINs, and so on, what can be done to mitigate the ThermoSecure threat? We've gathered the main factors that can impact the success of a thermal attack.
Input factors: Users can be more secure by using longer passwords and typing faster. "Users who are hunt-and-peck typists are particularly vulnerable to thermal attacks," note the researchers.
Interface factors: The thermodynamic properties of the input device material is important. If a hacker can image the input device in under 30 seconds, it helps a lot. Keyboard enthusiasts will also probably be interested to know that ABS keycaps retained touch heat signatures much longer than PBT keycaps.
Erase activity: The heat emitted from backlit keyboards helps disguise the heat traces from the human interaction with the keyboard. A cautious person could sometimes touch keys without actuating them and not leave the input area for at least a minute after they input the username / password.
Go passwordless: Even the best passwords are embarrassingly insecure compared to alternative authentication methods such as biometrics.
In summary, the accuracy of these thermal attacks is surprisingly high, even some time after the user has moved away from the keyboard / keypad. It is worrying but no more so than the other surveillance / skimming techniques that are already widespread. The best solution to these kinds of password and PIN guessing methods appears to be the move to biometrics, and / or two or more factor authentication. Preventing unauthorized access to your device in the first place (i.e. not leaving your laptop or phone unattended), especially not right after typing in your PIN/password, will also help thwart attackers.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Mark Tyson is a news editor at Tom's Hardware. He enjoys covering the full breadth of PC tech; from business and semiconductor design to products approaching the edge of reason.
-
georgebaker437 It would seem that warming the keypad to 37 degrees would instantly eliminate this problem. The waste of energy would be negligible when compared to the economic and legal costs of a security breach.Reply -
Reply
Why waste all that energy when there are already quite a few superior alternatives, such as using a password manager or going passwordless?georgebaker437 said:It would seem that warming the keypad to 37 degrees would instantly eliminate this problem. The waste of energy would be negligible when compared to the economic and legal costs of a security breach. -
Gam3r01 This really only seems applicable when you *only* enter the password.Reply
Most people arent going to cold start typing on a keyboard, enter exactly their password, then leave. You are going to typically have many other inputs either immediately after or before (I mash random keys to get windows to open the login page at boot, for example). Anything with a touch screen would also be mitigated by using a software that rotates the number combos every time. -
bit_user Reply
I mostly agree, but if you enter your password and then initially go for the mouse, there's a gap where someone could sneak a picture over your shoulder or from the side. This could be a relevant attack vector for cafe's and other public situations - even if you're using your own laptop!Gam3r01 said:This really only seems applicable when you *only* enter the password. -
USAFRet Reply
If they're close enough to do that, they're close enough to do a 3 second surreptitious video of your fingers.bit_user said:I mostly agree, but if you enter your password and then initially go for the mouse, there's a gap where someone could sneak a picture over your shoulder or from the side. This could be a relevant attack vector for cafe's and other public situations - even if you're using your own laptop! -
bit_user Reply
True, but whereas it could be hard to work out which keys you're hitting from a shaky video, one (relatively) clear thermal snapshot could (possibly in combination with the video) give a much clearer result.USAFRet said:If they're close enough to do that, they're close enough to do a 3 second surreptitious video of your fingers. -
USAFRet Reply
I don't know about you, but I can take a really clear stable video of you at an adjacent Starbucks table.bit_user said:True, but whereas it could be hard to work out which keys you're hitting from a shaky video, one (relatively) clear thermal snapshot could (possibly in combination with the video) give a much clearer result.
Later, at home, I can replay in whatever slomo I want.
Tomorrow, when you come in for your daily java and Team chat....I steal your laptop.
Then, revel in the plethora of crazy cat videos you have...;)
Don't get me wrong....this is an interesting concept.
But I'm not too worried about it.