How Hardware-Based Security Protects PCs
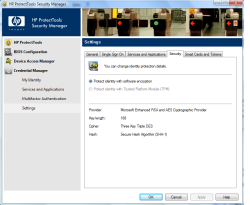
Security systems like biometrics can work without a Trusted Platform Module, but they're more secure with it. Click the image to see a larger version.
Using Hardware For Security:from Palladium To VPro
Secure online banking, password protected documents, secure remote access to your work PC - they all rely on encryption at some point. But running that whole security process in software is like leaving a spare front door key somewhere in your yard - you're relying on being able to think of a key-sized hiding place that a burglar won't find.
Random numbers, traditionally stored on disk or in standard memory, are used to encrypt the private keys, also stored on disk or in memory, that secure documents and connections. Back in 2000, encryption specialist nCipher showed that a Trojan like Back Orifice could easily find those random numbers and the private keys they protect. And as long as you're running your operating system with administrator privileges, if malicious software can get onto your system, it can attack your encryption tools, anti-virus software and virtual machines the same way it can corrupt files or steal personal information.
Software can be changed by other software, on your hard drive or in memory; you can't rely on security software to warn you, because that could be changed as well. You need to add hardware that you can use as a reference point, which can't be altered by malicious software. Some businesses secure user log on with smart cards like the SIM in a GSM phone, or dongles that calculate random numbers based on a seed known only to the server to which they connect. But adding security hardware to an existing PC is expensive, and relies on a security system designed to use it; it's better to build in hardware-based security from the start.
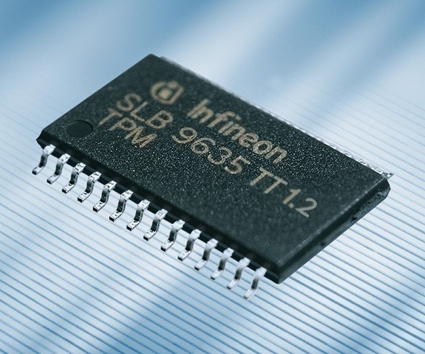
That was the idea behind the security system once known as "Palladium". Over the years, plans for Palladium and the Next Generation Secure Computing Base included embedding a secure OS in hardware, so it would be protected from malicious software. But design issues and concerns that this might be used to enforce systems like digital rights management or other controls meant the aims were scaled back. What you get now is a dedicated chip known as the Trusted Platform Module (TPM), which is used to secure key pairs used for options like encrypting your whole hard drive with software like PGP and BitLocker.
Intel, VIA and AMD all support the TPM, but Intel also has extra hardware-level security and management features, like Trusted Execution Technology (TXT); this was previously codenamed LaGrande, and used for checking that virtualized software hasn't changed since you last ran it. There is also Active Management Technology (AMT), which is used for remote management, and isolating and updating PCs that might be infected. These features are implemented in a combination of the CPU, chipset, TPM and network controller, plus software, all of which Intel calls a "platform". Today, these features are designed for business, so they're in desktop systems under the vPro platform brand, and in notebooks as Centrino Pro (or Centrino with vPro), but they'll come to consumer systems like VIIV in the future. And while the TPM is a separate chip now, Intel plans to incorporate it into the I/O Controller Hub directly later this year, adding extra features like AES encryption done in hardware.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: Security systems like biometrics can work without a Trusted Platform Module, but they're more secure with it. Click the image to see a larger version.
Next Page Trusting The Trusted Platform Module-
isaacio Yes,the security system once known as "Palladium".Discount Security Systems protect your own home against danger, damage, loss and criminal activity.Reply