Harden Up: Can We Break Your Password With Our GPUs?
Exploring Password Strength
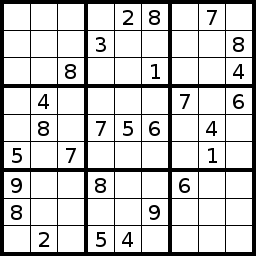
Recovering a password can be a complicated process. Think of encryption like a Sodoku puzzle. The larger and more complicated the puzzle, the harder it is to defeat an encryption scheme. There are two ways to go about trying, though.
In the first, hackers typically try to look for some sort of overall pattern. You can divide this further into different classes of attacks, some of which you may have heard of in the news, such as a side-channel attack. These methods are complex, and out of the reach for the everyday computer user. Only a select group of people have the skill set and drive to do that sort of work.
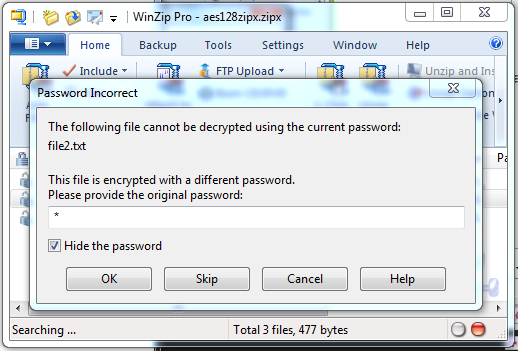
A much more primitive approach to defeating encryption is simple "guessing and checking." This is known as a brute-force attack. Think of this as generating every single combination of numbers that can be used to solve that same Sodoku puzzle, starting from an all ones all the way through all nines. There are ways to hide the "checking" part of the process to make the attack more complicated. But simple programs like WinZip and WinRAR don't have that luxury. If you are persistent, you can keep guessing passwords until hell freezes over. There is no limit on the number of guesses you get. So, the real problem in recovering a password is the speed at which you can guess the right answer.
Manually checking passwords is probably a foolish endeavor at best, especially if you're dealing with a long password. This is where password recovery tools come into play. They automate the process of guessing passwords.
| Available Characters Using The English Language | Possible PasswordsTwo Characters | Possible PasswordsFour Characters | Possible PasswordsSix Characters |
|---|---|---|---|
| Lower-case | 676 | 456 976 | 308 915 776 |
| Lower- and Upper-case | 2704 | 7 311 616 | 19 770 609 664 |
| Lower-case, Upper-case, and Numbers | 3844 | 14 776 336 | 56 800 235 584 |
| All ASCII Characters | 8836 | 78 074 896 | 689 869 781 056 |
Brute-force attacks rely on probability. The longer the password, the more passwords there are to check. This relies on the notion of permutations, which are the arrangement of objects in a particular order. So think of passwords as anagrams. If I gave you the letters a, b, and c, how many different ordered arrangements could you make? With only three letters, you can create a set of six permutations of the set {a,b,c}, namely [a,b,c], [a,c,b], [b,a,c], [b,c,a], [c,a,b], and [c,b,a].
Calculating the number of possible passwords is simple. Repetitions are allowed, so the formula is n(password length), where n is the number of possible characters. As you can see, at six characters, we're already in the billions if you include lower- and upper-case letters. If you also include special characters and numbers (all ASCII characters), you'll find that the number of password candidates explode to three-quarters of a trillion. And don't forget that that if you don't know the length of your password, you have to search all of the possible combinations from a single-character password to the length of your choosing.
Can you see where this is going?
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: Exploring Password Strength
Prev Page Archive Encryption: WinZip And WinRAR Next Page Password Cracking: CPU-Powered-
jeff77789 "While it would take a longer time to find a password made up of nine or 10 passwords, it's definitely doable between a few gaming buddies. "Reply
9 or 10 characters? -
ryandsouza "Think of this as generating every single combination of numbers that can be used to solve that same Sodoku puzzle, starting from an all zeros all the way through all nines. "Reply
Sudoku puzzles have numbers from 1 through 9! -
rpmrush This reminds me of Bitcoin GPU crunching. 6990s are favored right now. I wonder how many were sold specifically to Bitcoin miners? I tried it with my dual 6850s but the heat was rediculous. I didn't like the stress on my hardware so I gave up mining. I'm sure it's the same with password software. Maxing out your GPUs. Great for Winter, not Summer!Reply -
mediv42 I've always wondered about this: why don't they just code a delay into the decryption program, so you can't check a billion passwords a second?Reply
-
joshyboy82 I like the scale, but in your small example (a,b,c) you were right and wrong at the same time. Based on your configuration 6 possibilities are correct, but because you tell someone that they can use A or B or C in the password doesn't stop them from choosing aaa, therefor the combination is 9, not 6. Otherwise, interesting article.Reply -
acku Reply9515787 said:"Think of this as generating every single combination of numbers that can be used to solve that same Sodoku puzzle, starting from an all zeros all the way through all nines. "
Sudoku puzzles have numbers from 1 through 9!
Fixed! Sorry. I usually play Sudoku variants. :)
9515790 said:I like the scale, but in your small example (a,b,c) you were right and wrong at the same time. Based on your configuration 6 possibilities are correct, but because you tell someone that they can use A or B or C in the password doesn't stop them from choosing aaa, therefor the combination is 9, not 6. Otherwise, interesting article.
I could understand that, but I left out that since I was trying to show a simple example of how permutations differ from combinations. As you pointed out, repetitions are allowed in passwords. I actually mention that in the sentence that follows in the next paragraph. -
webdev511 Password Haystacks Yes Steve Gibson has already covered something like this. Passphrases with upper lower number and speical are the way to go. Yes, please avoid shortcuts.Reply -
acku Reply9515789 said:I've always wondered about this: why don't they just code a delay into the decryption program, so you can't check a billion passwords a second?
It wouldn't be easy from a design standpoint, cause now you're talking about fiddling with the design of the program.
The easiest way to slow down the verification portion of the password authentication process is increasing the number of transformation invocations for key generation. The problem is that this slows down the performance of your machine, even if you have the correct password.
jj463rdHow about adding some extended ASCII codes to a password.
That assumes WinZip and WinRAR supports them. To be honest, I haven't looked into that. Though, I'm inclined to believe that neither program supports them. -
shin0bi272 the tables in this review are horrible... they go from lengths of time to number of passwords and theres no discernible notation when they do.Reply