AMI's UEFI Signing Key and BIOS Source Code Leaked
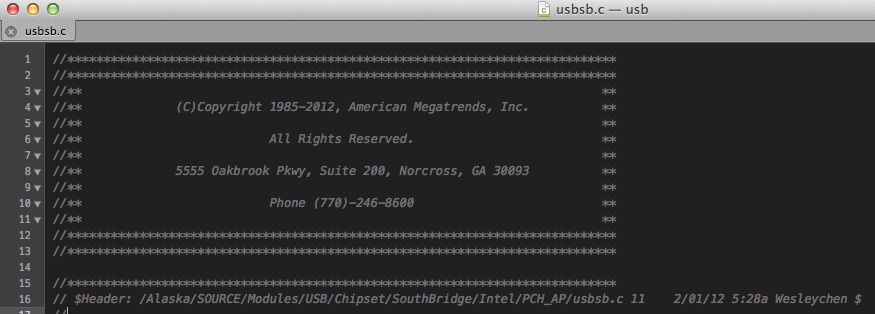
A publicly accessible FTP server in Taiwan has leaked the source code for AMI’s Aptio UEFI BIOS.
AMI’s Aptio UEFI BIOS source code and its unique UEFI signing key has been leaked onto a publicly accessible FTP server in Taiwan, an event that may have compromised the security of every motherboard running AMI Aptio. The release of the latter item malware gives developers the ability to develop “signed” malicious BIOS updates, replace legitimate system BIOS updates, and gain access to most ring-0 OS functions.
Adam Caudill, who discovered the open FTP server along with Brandon Wilson, characterized the leak as a “dream come true for advanced corporate espionage or intelligence operations” and further added that “the ability to create a nearly undetectable, permanent hole in a system's security is an ideal scenario for covert information collection.”
The industry blogger also cited motherboard vendor, Jetway, as being responsible for placing the files on the unsecured FTP server, a claim that has yet to be conclusively verified. In AMI’s official statement, the company confirmed that the leak took place and noted that the "leaky FTP server" was run by one of AMI's customers. Therefore, the leak of the data was not "the fault of AMI and by extension not a result of a security lapse on AMI’s behalf."
With regard to the severity of the threat, AMI seemed to disagree with Adam Caudill, as they do not view it as a "general security threat" which could “create a nearly undetectable, permanent hole in a system’s security" and advised all concerned parties to contact an AMI Sales Representative or AMI Technical Marketing for further information.
Subramonian Shankar, American Megatrends CEO and President, further commented that “while today’s news is certainly distressing, AMI would like to reassure its customers and partners in no uncertain terms that this should not be a security concern for them. If they follow standard operating procedure for BIOS signing, the security features in our BIOS source code and secure signing process will function as designed and remain 100% secure.”
Contact Us for News Tips, Corrections and Feedback
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Tarun Iyer was a contributor for Tom's Hardware who wrote news covering a wide range of technology topics, including processors, graphics cards, cooling systems, and computer peripherals. He also covered tech trends such as the development of adaptive all-in-one PCs.
-
ssd_pro All test keys, not production keys. Unless your motherboard mfg is as shady as Jetway and didn't follow standard procedure and convert test keys to production keys, there is little concern here.Reply
http://ami.com/News/PressRelease/?PrID=392 -
A Bad Day ReplySubramonian Shankar, American Megatrends CEO and President, further commented that “while today’s news is certainly distressing, AMI would like to reassure its customers and partners in no uncertain terms that this should not be a security concern for them. If they follow standard operating procedure for BIOS signing, the security features in our BIOS source code and secure signing process will function as designed and remain 100% secure.”
1. Trick user into visiting an trusted but infected website, or a website with infected advertisements.
2. Load a self-replicating rootkit onto the computer, which then identifies what mobo the computer has. Any USB drives or external storage will also be compromised.
3. Detect AMI mobo, start BIOS replacement when the computer is restarted so Windows can install updates. Many users won't suspect anything, thinking it's just the Windows update. Only experienced users will become suspicious.
4. Open backdoors after BIOS is replaced. Let the fun begin. -
A Bad Day EDIT: I'm fairly sure experienced malware writers could come up with a quicker and more stealthy method of delivery.Reply -
randomizer Reply...advised all concerned parties to contact an AMI Sales Representative or AMI Technical Marketing for further information
Telling customers to call sales reps about security issues. That's good advice. -
ttcboy This news lacks of one thing, " WHAT ARE THE AFFECTED MOTHERBOARDS ???"Reply
We don't want to worry if our mobo is not affected and we want to be cautious if ours is. -
DRosencraft I am generally opposed to capitol punishment... but these hackers certainly tempt a guy to reconsider... In all seriousness, I would be helpful to know what boards might be effective, and if there is going to be a "fix" any time soon. I wasn't planning on replacing my board, but apparently now I might have to.Reply -
Jeff Burns The only way to secure this kind of thing is to use YOUR own keys. You have to assume somebody nefarious has the "secure" keys from the Mfg since its use is so widespread. This one is public, which is great, but what about the ones that you don't know about. Just imagine SIGNED Malware that bypasses everything under a secure moniker....Reply -
utroz Hmm maybe this will open up the "custom" OS on PC's again... Granted they are test keys but if you are really smart and reverse engineer current keys with the test keys you could work out the way they make them.....Reply -
smeezekitty The way I look at it is this will be good for the open source community.Reply
UEFI does not really add much security and secure boot lockout is a terrible idea.