SupportAssist Software Exposed Dell PCs to Hackers
Attacks could remotely exploit a vulnerability in Dell’s SupportAssist application, found on all notebooks and PCs sold by Dell. The vulnerability, as shared by Bill Demirkapi via GitHub, allows hackers to gain administrative privileges on the machines and execute malicious code to take over users’ systems. A patch was released on April 23.
Most Dell Customers Affected
The exact number of affected users is not known, but considering Dells puts the SupportAssist application on all of its new Windows computers, then anyone who still has it running would be vulnerable to this kind of attack. Devices that the company sells without Windows are not affected, since the app doesn’t come pre-installed.
The tool is normally used for Dell automatic driver updates, debugging and diagnostics the company may perform on its customers’ machines, when needed. However, debugging tools also tend to have deeper access to a device’s systems, so when attackers can exploit them, especially remotely, that gives them full control over the computers.
Article continues belowHow the Attack Works
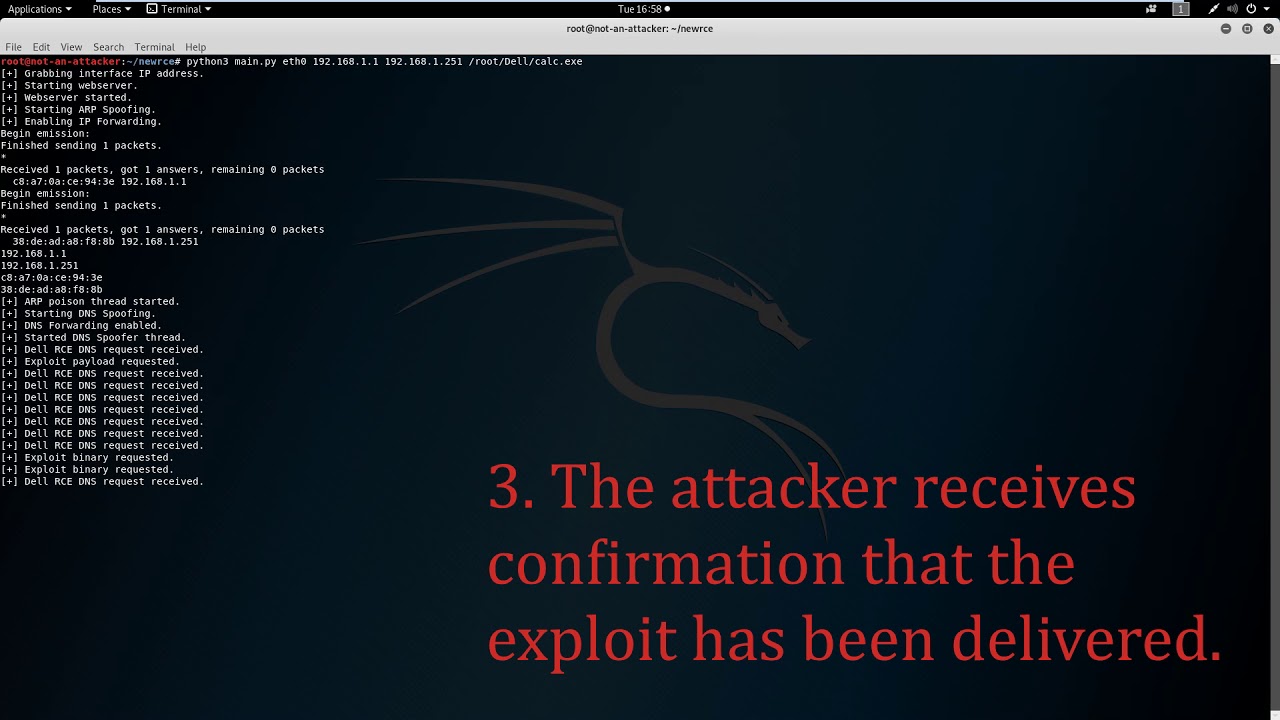
The attack works by first getting users into accessing a malicious web page, from which Dell’s SupportAssist is then tricked into downloading and running malware on the users’ PCs.
The Dell SupportAssist application runs with administrative privileges by default, something that doesn’t apply to the vast majority of Windows applications. Because of this, the attackers who get to exploit the app also get gain administrative rights on the users’ PCs.
The most likely scenarios in which the attacker can exploit the app’s vulnerability remotely is when the victims are on a public Wi-Fi network or on a large enterprise network, to which the attack has access.
From there, the attacker can launch Address Resolution Protocol spoofing attacks, giving them access to legitimate IP addresses within the network, as well as DNS attacks. DNS attacks seem all too easy to do recently due to the poor state of security on the vast majority of existing routers.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Update to Latest Dell SupportAssist Version
Bill Demirkapi, a 17-year old security researcher that discovered the SupportAssist app vulnerability, notified Dell about the bug a few months earlier and Dell has been working since then to fix the flaw. The company patched the vulnerability and released version 3.2.0.90 of the SupportAssist application, which it encourages its customers to install.
However, ideally, the application wouldn’t use administrative rights by default, until the Dell customer encounter themselves with an issue that needs to be resolved by Dell’s support. Until then, Dell customers may just be safer uninstalling the app or preventing it from running in the background, as other similar vulnerabilities that allow attackers to take advantage of its administrative privileges may appear in the future. After all, this wasn't the only time Dell's customers were put at risk due to Dell giving its own pre-installed applications full access to the user's PCs.
Coincidentally, Dell’s own network suffered a data breach weeks after Demirkapi found the vulnerability in the SupportAssist application. Presumably the two incidents are unrelated, unless Dell also ran the SupportAssist application on its own internal computers with the same privileges, allowing attackers to take over its network through the same vulnerability.
Demirkapi wrote a full vulnerability report on his GitHub blog, released a proof-of-concept for the attack and also published a video demo in which he shows how a malicious actor could take full control of a Dell computer via this vulnerability. You can see the video below.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.