Webroot Discovers BIOS Rootkit
Security software company Webroot says a BIOS rootkit has been found in the wild.
Called Mebromi, the malware is reminiscent of the IceLord proof of concept BIOS rootkit in 2007, was a late 1990s virus that was able to erase the motherboard software. This new rootkit is a different caliber as it is appears to be one of the most persistent malware programs we have heard so far.
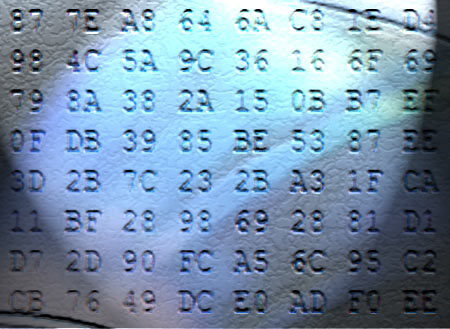
According to Webroot, Mebromi targets Award BIOS and attaches itself to it so it can infect a client computer over and over again. The malware then infects the master boot record to be able to infect winlogon.exe or winnt.exe to be able to use Windows to download additional malware. There is no easy way to get rid of Mebromi at this time as traditional anti-virus software won't reach down to the BIOS level.
Webroot said that the rootkit is targeting Chinese users and seems to be modeled closely after IceLord, which was demonstrated in 2007. The company stated that "storing the malicious code inside the BIOS ROM could actually become more than just a problem for security software, given the fact that even if an antivirus detects and cleans the MBR infection, it will be restored at the next system startup when the malicious BIOS payload would overwrite the MBR code again."
Webroot's Marco Giuliani noted that "developing an antivirus utility able to clean the BIOS code is a challenge, because it needs to be totally error-proof, to avoid rendering the system unbootable at all." He added: "The job of handling with such specific system codes should be left to the developers of the specific motherboard model, who release BIOS updates along with specific tool to update the BIOS code."
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Douglas Perry was a freelance writer for Tom's Hardware covering semiconductors, storage technology, quantum computing, and processor power delivery. He has authored several books and is currently an editor for The Oregonian/OregonLive.
-
HMRkingpin Remember..... The best line of defense is you. Be careful of what you open and click on.Reply -
amk-aka-Phantom HMRkingpinRemember..... The best line of defense is you. Be careful of what you open and click on.Reply
+over 9000. No antivirus will help you if you're stupid and careless. -
amk-aka-Phantom ReplyWebroot said that the rootkit is targeting Chinese users and seems to be modeled closely after IceLord, which was demonstrated in 2007. The company stated that "storing the malicious code inside the BIOS ROM could actually become more than just a problem for security software, given the fact that even if an antivirus detects and cleans the MBR infection, it will be restored at the next system startup when the malicious BIOS payload would overwrite the MBR code again."
Blah blah blah blah blah... flash the BIOS, format the hard drive, problem solved... /facepalm -
dalethepcman this would suck if it started spreading, imaging all the bricked machines that need their BIOS chips replaced. Thank god for UEFIReply -
ikyung Webroot discovers BIOS rootkit in the wild!Reply
Webroot uses tackle!
Webroot uses growl!
Webroot uses tackle!
BIOS rootkit faints.. -
11796pcs offerings12Flash the bios.... poof goneI don't really think the issue should be considered that simple. Can you imagine how long it would take you to find out that you had an infected BIOS? And if there's one thing I don't like to mess with on my PC it's the BIOS. BIOSes are perfect example of: if it ain't broke don't fix it". If I had an infected BIOS it would prbably be one of the last places I would look. Also: even though this virus is targeted towards the Chinese any person who has a virus on his/her computer affects us all.Reply -
jhansonxi amk-aka-phantomBlah blah blah blah blah... flash the BIOS, format the hard drive, problem solved... /facepalmAnd you're going to do that with a BIOS flash utility, running on an infected OS, connecting to an infected BIOS, and you think the malware writers didn't plan for that? The only program that has more control over your system than the BIOS is the CPU microcode (which the BIOS can also patch to fix CPU bugs). I think it's also possible to infect the BIOS boot recovery block so unless you have a system with a dual BIOS (like some server MBs), then you're not going to get rid of it. It's also possible to infect the system through the CMOS.Reply
In the old days the solution was to pull the BIOS ROM, reprogram it on a PROM burner with a clean BIOS copy, clear the CMOS, then reinstall the ROM. Not so easy to do on today's systems.
-
warezme jhansonxiAnd you're going to do that with a BIOS flash utility, running on an infected OS, connecting to an infected BIOS, and you think the malware writers didn't plan for that? The only program that has more control over your system than the BIOS is the CPU microcode (which the BIOS can also patch to fix CPU bugs). I think it's also possible to infect the BIOS boot recovery block so unless you have a system with a dual BIOS (like some server MBs), then you're not going to get rid of it. It's also possible to infect the system through the CMOS.In the old days the solution was to pull the BIOS ROM, reprogram it on a PROM burner with a clean BIOS copy, clear the CMOS, then reinstall the ROM. Not so easy to do on today's systems.Why not? You should be flashing the bios from either a bootable CD, thumbdrive or floppy. Windows shouldn't be in the way just for such reasons and more. Bios FLash - 5 minutes, tops.Reply -
beardguy Haven't had any antivirus software in 4+ years and never had a single problem.Reply
If you stay away from sketchy sites and know what you are doing, you don't need antivirus.