Intel vPro: Three Generations Of Remote Management
It's common to manage PCs remotely in today's business environment. Intel's vPro technology aims to simplify that task by giving IT professionals hardware-level tools to make remote management easier. Today we look at three generations of vPro.

An Introduction To Intel vPro And Active Management Technology
In today’s enterprise environment, desktop management is an area where CIOs are constantly evaluating ways to lower costs. If you look at a typical mid- to large-sized organization, there is usually a mobile sales force and support staff, multiple buildings and locations, and every employee has either a desktop or notebook.
Over the past few years, IT organizations have looked for ways to help combat rising costs associated with managing common IT problems. Although their approaches may differ, the common ideology permeating IT these days is to move service and support away from desk-side visits to save time and money.
Beyond the logistic issues that eat up valuable resources, IT is also constantly contending with security threats and more maintenance-oriented tasks like taking component inventories. Many years ago, Intel conceptualized vPro as a means of simplifying all of those tasks, arming the VARs who help manage SMBs and the dedicated IT departments in larger organizations at the very same time.
Intel’s vPro technology is fairly unique as a set of capabilities that facilitate serviceability and security in end-user computing environments. Given Intel’s position selling CPUs, chipsets, and network controllers, the company is in a unique position to get a number of disparate hardware components working together. Over time, those technologies have evolved to include more advanced controls, which enable some pretty interesting features that we've never seen compared back to back before.
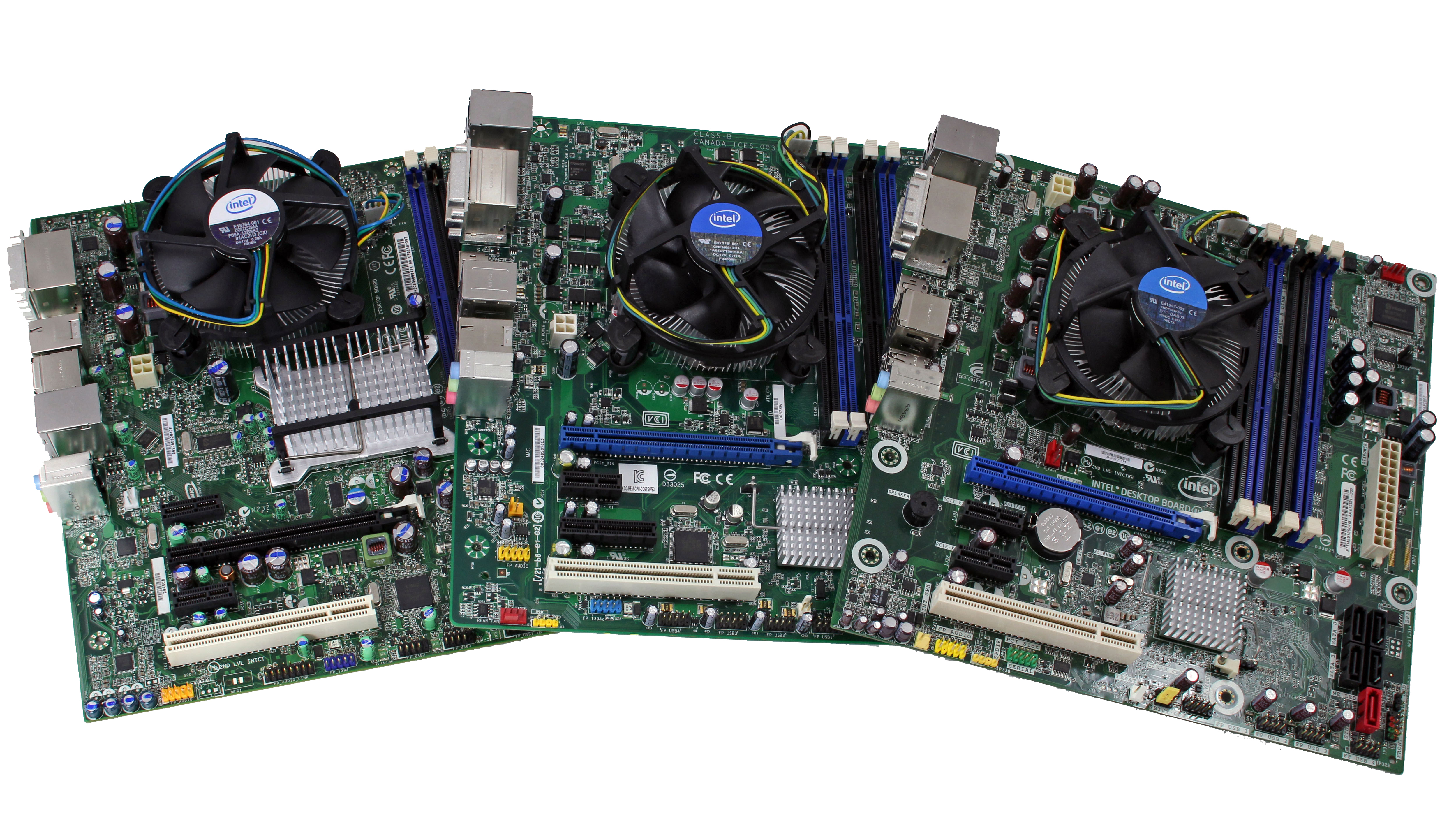
Intel sent over three generations of Intel vPro platforms to show how its business platform has evolved, from the Wolfdale-based Core 2 generation up to the current Sandy Bridge architecture. The economic recession has seen a number of companies shrinking their employee's work spaces, so the microATX form-factor chosen for all three setups is a good way to also facilitate a smaller PC footprint compared to larger ATX boards.
First, we'll take a look at the hardware itself before delving into the successive capabilities introduced by vPro itself.
One thing is for sure: Intel clearly intends vPro technology to be as usable in the enterprise space as it is in small- and medium-sized businesses. With that said, the feature set of Intel vPro might even appeal to anyone who wants to manage a family member's PC from afar due to inclusions like the Intel KVM found in its Clarkdale and Sandy Bridge vPro generations.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: An Introduction To Intel vPro And Active Management Technology
Next Page Unique vPro Hardware Requirements-
cngledad Can I suggest an article comparing different remote access tools we can use? From the freeware TeamViewer, VNC Viewer to such things like WebEx? I think that would be a very good topic.Reply -
One correction: DQ57TM *does* contain a v1.2 TPM, the same as found on DQ67SW and DQ67EP. It's required to be vPro compliant (necessary for Intel TXT).Reply
-
jhansonxi Nifty but I don't like the single-vendor lock-in. I can see real improvements in IT efficiency if this was combined with AoE. Would like to see SSH support, however.Reply -
extremepcs Hopefully they have improved the activation mechanism. Kind of a PITA if you don't buy a certificate from a trusted CA. I used an internal cert and had to activate each machine by booting from a flash drive.Reply -
chovav If my hard drive is encrypted using TrueCrypt pre-boot authentication, would I be able to fill in the password using Intels vPro?Reply -
jowunger The voice of the guy in the video is bad. The guy talks like he is speedreading a book...Reply -
cangelini cdw-vproOne correction: DQ57TM *does* contain a v1.2 TPM, the same as found on DQ67SW and DQ67EP. It's required to be vPro compliant (necessary for Intel TXT).Reply
Fixed, thanks!