Why iOS 12 May Be More Secure
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Apple’s latest major mobile operating system revision, iOS 12, is here, and it comes with several significant security improvements that should make iPhones and iPads safer to use.
Automatic iOS 12 Updates
Most security experts agree that automatic software updates are a good thing for the vast majority of users and devices out there (except for the times it isn’t). The latest iOS version comes with automatic software updates that download and install silently in the background without inconveniencing the user.
The automatic updates aren’t enabled by default. Presumably this is to avoid potential unexpected issues that could affect a large portion of the iOS user base. Apple may turn this feature on by default for future iOS updates, just as Google has done with Android updates for its Nexus and Pixel devices.
Article continues belowCustom Numeric Code
Initially, iOS allowed only four-digit PINs, which have been easy to brute force for many years. However, devices would also lock after a certain number of failed login attempts, which significantly reduced this issue. Nevertheless, Apple introduced six-digit PINs in iOS 9, which increased the difficulty of brute forcing but didn’t make it impossible.
The automatic locking should work as long as the feature is enabled, but if attackers find a bug in that feature, they could, presumably, disable it. Then, they’ll still be able to brute force the device. Removing the brute force limiter is also something the FBI has asked Apple to do in the infamous San Bernardino case.
In iOS 12, Apple introduced a “custom numeric code” feature, which allows you to input a PIN of any length. This is a nice addition that should further strengthen PIN security, but it’s ultimately still less secure than a proper long and unique passphrase with lowercase and uppercase letters, numbers and symbols.
Plus, it’s been scientifically proven that most humans can’t remember numbers that are much longer than seven digits. Remembering full words or a sentence is much easier in contrast.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Auto-filling SMS 2FA Codes
Apple also introduced auto-filling of two-factor authentication passcodes sent via text messages. This is more of a convenience feature because you no longer have to type the code you receive yourself. Google also introduced this feature in Android 8.0 and backported it all the way to Android 4.3 via its Play Services APIs.
The U.S National Institute of Standards and Technology (NIST) recommended the deprecation of SMS 2FA codes back in 2016 because it’s no longer considered secure. Apple making it easier for its customers to use SMS 2FA could have the effect of increasing SMS 2FA support by app developers, something that may or may not be such a good thing in the long term.
You will be asked to turn on 2FA when you set up your phone, but you can also change it from Settings > Your name > Password & Security > Turn on two-factor authentication. Then follow the prompts.
New Password Security Features
The Safari browser in iOS 12 will start suggesting stronger passwords, which probably means longer and more unique default passwords for new website accounts.
The new iOS will also alert you when you’re using the same password on two or more websites. Password reuse is dangerous because even if you use a strong password for a website you know is secure, that password could be leaked from another less secure website for which you used the same password.
Encrypted FaceTime Group Video Chat
FaceTime chats and one-on-one voice and video calls are end-to-end encrypted, which means neither malicious hackers trying to intercept the messages nor Apple itself can read them (unless they are automatically backed up to iCloud, which is set as default on iOS devices).
Apple uses its own end-to-end encryption protocol and not an existing one, such as the Signal protocol, which has supported end-to-end encrypted video calls for several years. However, starting with iOS 12, FaceTime group video chat will also be encrypted end-to-end.
Restricted USB Mode
In iOS 12, Apple has drastically increased protection against physical attacks affecting iOS devices. After transferring something from your device to a laptop, the Lightning port will be switched from a data connection to charging after only one hour. This window was drastically reduced from a seven-day period in previous iOS versions.
The only issue is that, according to Russian security firm Elcomsoft, cheap accessories that don’t support authentication can bypass this restriction. However, the attacker would still need to connect that accessory within the one-hour time window for this hack to work.
Tracking and Fingerprinting Protection
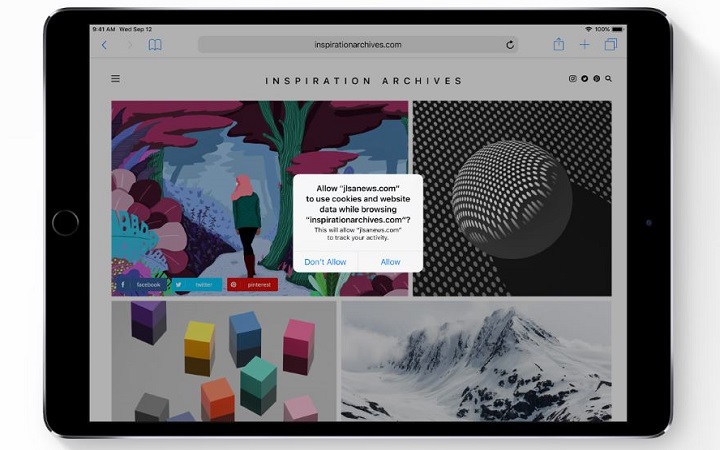
Safari has been blocking third-party cookies on iOS for a few years now. In iOS 12, Apple has taken some action against social media share buttons and comment systems that track users by default, even when they aren’t signed into their accounts for those services. Now, the browser will detect this type of tracking and prompt you to allow or block it.
Apple will also make it more difficult for advertising companies to “fingerprint” you. Fingerprint is done via collection of data about your hardware and browser configurations. This feature will also arrive in the Safari browser in macOS Mojave.
Automatic 911 Location Sharing
Apple has partnered with RapidSOS, a company that is working with over 6,500 emergency call centers across the country to update their systems so that when someone calls 911, their location is automatically sent to the call center operator.
Apple had previously developed a technology, called HELO, which can more accurately pinpoint an iPhone user’s location. This precise location data is what will be sent to the emergency call operators.
With iOS 12 Apple continues to show that security and privacy protections remain priority and that its customers can expect the company to work on increasing their safety both online and offline.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
velocityg4 Some of these features can increase security. Some are annoyances. Some need more work.Reply
Restricted USB Mode: Many people have no need for USB devices at all. All they use the port for is charging. There should be an option to set it to always off. No one hour window or one second window. It just won't make any attempt to connect to a USB device.
SMS 2FA: This is an improvement security wise. It is also a pain for users who don't want it. It keeps bothering you to enable two factor authentication without a permanent refuse option. Optional security is great, forced or high pressure security is not.
Automatic Updates: This is worrying. One can only hope they don't force this in the future or turn on permanent nagging. Sometimes updates fail or introduce new critical bugs. Then you are stuck with a useless phone until you have time to restore from a backup. Windows 10 is infamous for this. Especially when you are trying to work and need to reboot. Only to find out you have to wait updates with no option to override.
Password suggestions: It's a good idea. It can also be annoying on websites with backward policies which don't allow good passwords. There is also the issue of password managers autofill not being 100% reliable. My experience is closer to 50% reliable. I can work the manual fill copy/paste just fine. This is daunting to impossible for the average user.