Windows 10 Users May Be Forced To Reinstall Office (But Maybe Not)
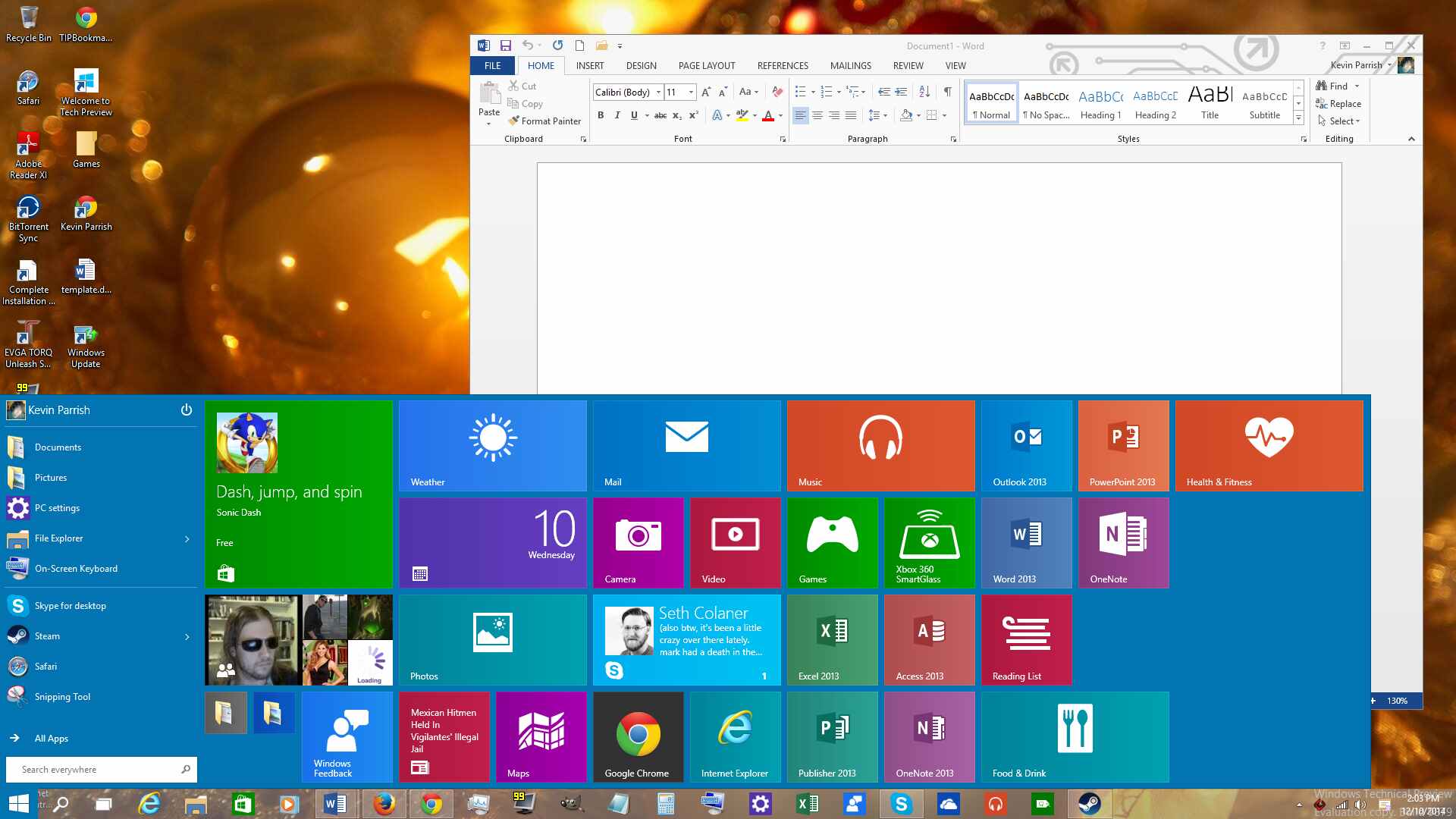
Are you part of Microsoft's Insider program and using the technical preview of Windows 10? Gabriel Aule of the Windows Preview team is now warning testers that they may need to uninstall Office before installing the recent security updates of Build 9879. He indicated that if the suite is installed, the security update will fail.
"Rather than rolling a new fix (losing several days in the process) we're going to publish it as is," he said via Twitter. "The workaround is painful: uninstall Office, install the hotfix, and reinstall Office. Sorry. We're working hard to fix. Please try to install KB3022827 *before* the workaround to uninstall Office first. It will work for many, no harm if not."
On a personal note, Windows 10 automatically installed the updates to Windows 10 on Wednesday morning. When the system rebooted, Office refused to work correctly, shutting down with an error. However, I simply used the "repair" option and Office began to work normally. There was no need to uninstall and reinstall the software.
Problems related to Windows 10 Technical Preview are not unexpected. Microsoft previously warned that the platform would have its share of glitches given that it's an early, unpolished build of Windows 10. Features will break as others are added or fixes are applied. The Insider program is meant for tech savvy users to provide feedback and help shape the final operating system.
Microsoft released seven updates on Patch Tuesday that address 24 vulnerabilities. Three patches are rated as "Critical," and the other four are listed as "Important." The top-most patch involves four privately reported vulnerabilities in Microsoft Exchange Server, one of which could provide hackers with elevated account privileges if the targeted user clicks on a "specially crafted URL."
"An attacker would have no way to force users to visit a specially crafted website. Instead, an attacker would have to convince them to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes them to the attacker's website, and then convince them to click the specially crafted URL," Microsoft reported.
Additional patches provided on Patch Tuesday included a huge update for Internet Explorer that addresses 14 privately reported vulnerabilities, an update for Microsoft Word and Microsoft Office Web Apps (two vulnerabilities), an update for Microsoft Office (one vulnerability), an update for Microsoft Excel (two vulnerabilities), an update to the VBScript Scripting engine (one vulnerability), and an update to the Microsoft Graphics Component (one vulnerability).
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Follow Kevin Parrish @exfileme. Follow us @tomshardware, on Facebook and on Google+.

Kevin Parrish has over a decade of experience as a writer, editor, and product tester. His work focused on computer hardware, networking equipment, smartphones, tablets, gaming consoles, and other internet-connected devices. His work has appeared in Tom's Hardware, Tom's Guide, Maximum PC, Digital Trends, Android Authority, How-To Geek, Lifewire, and others.
-
The3monitors Only bugs i have had with the os is the background settings refuse to be changed from landscape to stretch to others.Reply -
ssdpro I really enjoy the sharp "Windows 10 users may be forced" wording in the title. First, there are no Windows 10 users, there are users experimenting or testing the Windows Technical Preview. Also, I find it quite strange that this is being described this way: "the workaround is painful: uninstall office, install hotfix, reinstall office". Wow, really painful that they do this to a bunch of early voluntary testers. That might take almost 10 minutes.Reply