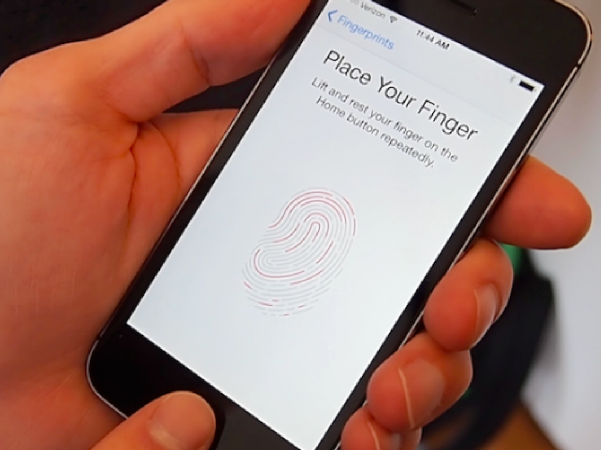
How Did Chaos Computer Club Reportedly Hack Apple's TouchID?
According to the Chaos Computer Club's Gerd Eist, the hardest part about defeating Apple's new TouchID reader was getting an iPhone 5S.
Less than two weeks after Apple touted its new Touch ID fingerprint reader as a "convenient and highly secure way to access your phone," the biometrics team of the European hacking group, the Chaos Computer Club (CCC), has reportedly been able to successfully circumvent the sensor using the "Starbug" approach that was documented by the CCC back in October 2004. So how did they do it?
According to the group's release, this approach involves a number of remarkably simple steps that only require materials that can be found in any household:
- A fingerprint of the enrolled user was photographed with a 2400 dpi resolution.
- The resulting image was cleaned up, inverted and laser printed at 1200 dpi onto a transparent sheet with a thick toner setting.
- Pink latex milk or white wood glue was smeared into the pattern created by the toner onto the transparent sheet.
- After curing, the thin latex sheet was lifted from the transparent sheet, breathed on to make it a bit moist, and placed onto the sensor to unlock the phone.
The group further noted that this process has been used with minor refinements and variations against the vast majority of fingerprint sensors on the market and that the press had been dominated by "bogus speculation about the marvels of the new technology" while in reality, defeating Apple's higher resolution sensor simply required a higher resolution fake.
The Chaos Computer Club has promised that further details about the hack will be made available at the source link; you can view their demonstration video below.
Follow us @tomshardware, on Facebook and on Google+.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Tarun Iyer was a contributor for Tom's Hardware who wrote news covering a wide range of technology topics, including processors, graphics cards, cooling systems, and computer peripherals. He also covered tech trends such as the development of adaptive all-in-one PCs.
-
MKBL It sounds like a 19th century thief making a copy of an original key to a lock, rather than "hacking" in IT sense. Key to this "hacking" is to get the original key, the finger print of the owner of the phone. I'm not downplaying the work of the group, but the title can be misleading.Reply -
mikat Soooo this requires the fingerprint of the correct user??? It's no more hackable than other fingerprint biometric system out there? Oh noes.Reply -
MKBL It sounds like a 19th century thief making a copy of an original key to a lock, rather than "hacking" in IT sense. Key to this "hacking" is to get the original key, the finger print of the owner of the phone. I'm not downplaying the work of the group, but the title can be misleading.Reply -
i don't think our physical finger print need that high resolution, i think event 300-400 dpi is enough already :)Reply
-
ap3x this is interesting. So what was represented in terms of how the sensor works is incorrect then. They should be really careful with how this is positioned then. If this is part of a 2 factor authentication strategy then it is fine (something you have, something you know) but by itself it will not cut mustard for payments. It is however fine to authenticate to the phone with it.Reply
Criminal's that are snatching phones are not all that sophisticated. Looking forward to hearing more about this. -
house70 Can lift fingerprints from a whole bunch of objects (cigarette packs, glasses, etc), no need for the actual finger, LOL. Then hijack the phone and profit. With the right tools it could be done even before the victim starts missing the device.Reply
Awesome. -
ingtar33 i liked how the mythbusters were able to fool about every fingerprint scanner on the market with a simple photocopy of someone's fingerprint (they didn't even have to do all those elaborate steps to make a "living" copy like the CCC did). Till they can make biometrics locks a bit more dependable it seems like this is a tech that's not quite ready for primetime.Reply -
brettms71 @house70, yes you can lift fingerprints of most items like you say. You can EVEN lift fingerprints off iPhones. Great that when you take someones iPhone now, the person has supplied everything you need to break into it, saving you time. Thanks Apple. They just make everything easier.Reply