Nissan Leaf Cars Can Be Hacked Through A Web Link
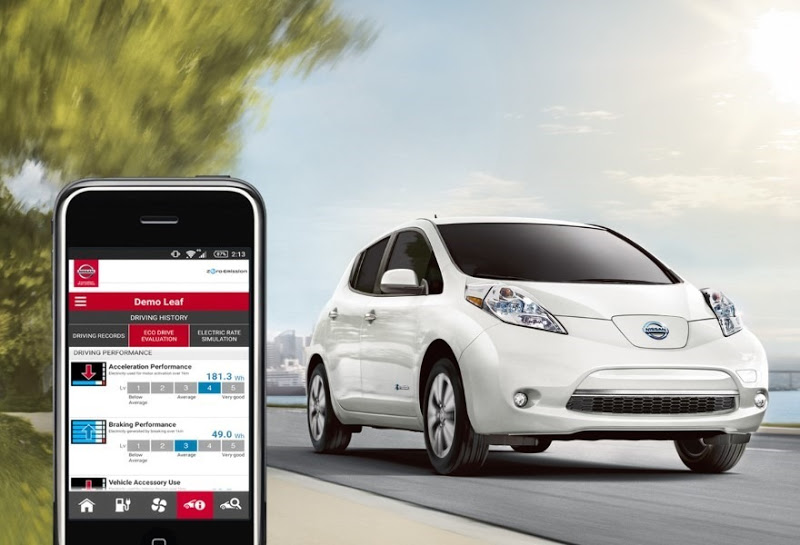
Troy Hunt, a security researcher uncovered a vulnerability in the NissanConnect app, which can allow attackers to connect to a car if they know their car's ID number. After that, they can hijack the car's air conditioning and heating systems. The fault lies in the complete lack of authentication for the application that enhances the car's dashboard with Internet-connected features.
The vehicle identification number (VIN), which is written on each Nissan Leaf's windshield, can be copied by anyone that passes by that car. However, the VIN is composed of characters that refer to the brand, make of car, and the country where it was manufactured. Only the last five digits vary between different Leaf cars in the same region, so someone could just build a script to attack all of the Nissan Leafs in a given region.
"There's nothing to stop someone from scripting a process that goes through every 100,000 possible cars and tries and turn the air conditioning on in every one," said Troy Hunt. "They would then get a response that would confirm which vehicles exist."
The security expert also noted that attackers don't even need to use the NissanConnect app, because they can deliver the attack through a web browser by spoofing the app. The Australia-based researcher tested this on a Nissan owned by his friend Scott Helme, who lives in the U.K.
"As I was talking to Troy on Skype, he pasted the web address into his browser and then maybe 10 seconds later I heard an internal beep in the car,” said Helme. "The heated seat then turned on, the heated steering wheel turned on. And I could hear the fans spin up and the air-conditioning unit turn on."
Hunt said that the test didn't work when the car was in motion, but it did show the owner's registered username, which could help reveal their identity. Times and distances of recent journeys were also revealed.
When Helme unregistered the app, Hunt's attack no longer worked. This is why Hunt suggested that this vulnerability could be easily fixed if the company disables the ConnectNissan service.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The researcher said that although this isn't a life-threatening attack, it could be used in ways that could put the cars' owners in danger. For instance, if the attackers hijack the car this way, they could see over the course of a week where the driver goes to work, and then they could drain the car's battery to make it so the driver can't get back home.
Hunt alerted Nissan about the flaw a month ago, but so far he hasn't gotten a proper response about it, so he decided to make it public to force the company to fix the issue. He said he has already seen some Canadian Leaf owners share information about this vulnerability online, so the issue is already out there, whether he would've kept it a secret or not.
This is why sometimes security researchers, who discover vulnerabilities in some products, can't wait for the companies to provide a fix if it takes longer than a few months and it looks like they are dragging their feet. Usually, it's not just one person that finds that vulnerability, but many others, who exploit it for their own purposes; therefore allowing the company to drag the process of fixing the issue doesn't mean that others aren't taking advantage of that vulnerability during that time.
This case also shows that although most car manufacturers are rapidly trying to build connected cars, electric vehicles that are almost completely controlled by software, and even self-driving cars, where the danger of software insecurity is even bigger, they aren't taking security all that seriously.
Software security in these modern cars should be treated at least as seriously, if not more so (because software security is so hard), as any other safety mechanism in a car. A software feature that could slightly increase the owner's convenience in using such a modern car could be turned into something that's used to crash that car. That's why car manufacturers need to think very carefully about each new software feature that they add to their cars, and it always needs to be written in a context of high security.
Lucian Armasu is a Contributing Writer for Tom's Hardware. You can follow him at @lucian_armasu.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
rantoc Well this proves that IoT in everything is stupid, everyone with any IT knowledge already knew that but to the public ... perhaps next time it will be way more sinisterReply -
dstarr3 ReplyThey can attack the climate control systems? Talk about turning up the heat!
You could do this to someone, except remotely:
https://www.youtube.com/watch?v=9ftrk9cjJgw -
chicofehr Security wont be taken seriously till someone dies as a result of a car hack unfortunately.Reply -
skit75 Reply17559781 said:Security wont be taken seriously till someone dies as a result of a car hack unfortunately.
Even then, a settlement with a gag order typically keeps that under wraps.
-
targetdrone This is why the Galactic a had manual water faucets and to lites AND why Adama would not allow the school teacher to have a networked computer on board!!!!Reply
Doesn't anyone watch Sci Fi any more?
-
DeadlyDays ReplySecurity wont be taken seriously till someone "important" dies as a result of a car hack unfortunately.
Fixed -
hoofhearted Damn cylons in our midst!Reply
This is why the Galactic a had manual water faucets and to lites AND why Adama would not allow the school teacher to have a networked computer on board!!!!
Doesn't anyone watch Sci Fi any more?