Microsoft gave customers' BitLocker encryption keys to the FBI — Redmond confirms that it provides recovery keys to government agencies with valid legal orders
BitLocker isn't as safe as you think it is.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
The FBI served a search warrant to Microsoft in early 2025 to recover the encryption keys on three laptops, with the company complying to allow the agency to access the data on the devices that it otherwise would have been unable to read. According to Forbes, Microsoft spokesperson Charles Chamberlayne said that it receives around 20 requests for BitLocker keys annually, but most of them fail because the user did not store their recovery key in the cloud.
Although there have been many requests through the years, with one Microsoft engineer even claiming that the U.S. government approached him way back in 2013 to install a backdoor in the encryption system (which he declined), this is the first recorded instance where the tech company complied and resulted in a breakthrough for the government.
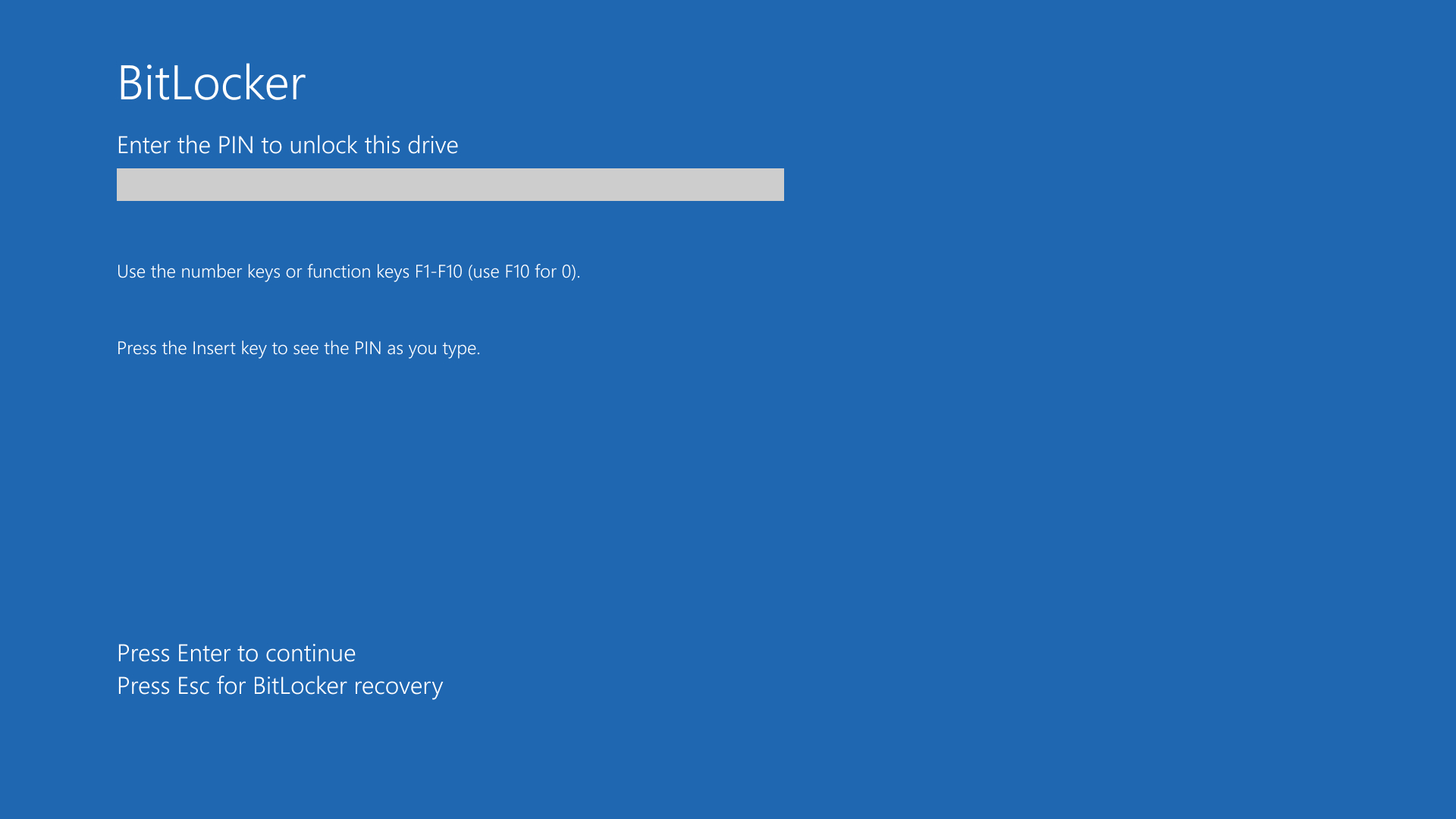
BitLocker is Microsoft’s built-in drive encryption system to protect Windows 11 users. And while it’s mostly designed to prevent unauthorized access to a drive’s contents, it has also experienced some bugs that can cause a significant loss of data, especially if you forget your encryption key. Nevertheless, Microsoft backs up your BitLocker keys online by default, making it more convenient for users to unlock their drives for situations like this. However, this also makes them vulnerable to valid government requests — not just from the U.S., but from other governments, as well, with less than stellar reputations, especially in human rights.
“While key recovery offers convenience, it also carries a risk of unwanted access,” Chamberlayne told Forbes. “So, Microsoft believes customers are in the best position to decide… how to manage their keys.” Americal Civil Liberties Union (ACLU) surveillance and cybersecurity counsel Jennifer Granick also said, “Remote storage of decryption keys can be quite dangerous.”
Apple offers a similar encryption system to Microsoft’s BitLocker with FileVault and Passwords, while Meta also keeps encrypted backups of WhatsApp data. Both companies allow users to keep backup keys for these systems online, but they’re also kept in an encrypted file. So, even if a government agency requests a copy of the stored key, neither Apple nor the concerned agency can unlock it without the proper key. Furthermore, Forbes notes that neither Apple nor Meta is known to have acquiesced to a request for an encryption key.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Jowi Morales is a tech enthusiast with years of experience working in the industry. He’s been writing with several tech publications since 2021, where he’s been interested in tech hardware and consumer electronics.
-
Math Geek Anyone surprised by this or believes it the first time, really needs to wake up. The entire point of MS keeping your encryption key is so they can snoop on your files. Secondary reason is so the US gov can access whatever they want as well from users worldwide.Reply
This is not a secret, it's only unknown to those deliberately avoiding reality. -
jp7189 Reply
Thats a little over paranoid take on it. Bitlocker, like most "at rest" encryption is freely accessible when the device is powered on and unlocked. You don't need a key to snoop at that point.Math Geek said:Anyone surprised by this or believes it the first time, really needs to wake up. The entire point of MS keeping your encryption key is so they can snoop on your files. Secondary reason is so the US gov can access whatever they want as well from users worldwide.
This is not a secret, it's only unknown to those deliberately avoiding reality.
In this case the FBI physically confiscated the laptops. No snooping about it.
All this article is reaffirming is that key management is a B. How and where those keys are stored is important.
Moral of the story, don't store your keys in a place that's accessible by the people you're trying to hide data from. -
ezst036 Giving up the keys, not a surprise at all.Reply
Again, the need for distributed computing could not be more clear.(FOSS/Linux/etc) -
pcn1201 Reply
Am I missing something here or am I the only person who thinks this is normal? If the FBI has a warrant for those encryption keys, then would it not constitute an obstruction of justice for MS to not provide them?Math Geek said:Anyone surprised by this or believes it the first time, really needs to wake up. The entire point of MS keeping your encryption key is so they can snoop on your files. Secondary reason is so the US gov can access whatever they want as well from users worldwide.
This is not a secret, it's only unknown to those deliberately avoiding reality.
If someone's being investigated by the FBI they probably have a reason, and also a warrant. Is there something else going in this situation I'm not aware of? -
umeng2002_2 This all goes back to the absurdity of the 3rd party doctrine loophole in the Constitution.Reply
Courts have ruled that since you shared information with someone else, it means you magically approve of anyone (the government) getting it to. -
USAFRet Reply
Key phrase:umeng2002_2 said:This all goes back to the absurdity of the 3rd party doctrine loophole in the Constitution.
Courts have ruled that since you shared information with someone else, it means you magically approve of anyone (the government) getting it to.
"...and our partners..." -
waltc3 I keep reading this on some sites, bizarrely (not here, thankfully): "BitLocker is turned on by default in every Windows installation." Gaaaa....;) The ignorance here is astounding...;) No, it's not turned on by default. I've never used it. Poor folks apparently think BitLocker is nothing you'd notice when installing or running Windows!...;) They must see end-to-end drive encryption as an ordinarily invisible AV program. This proves them ignorant of both Windows and BitLocker, imo.Reply
WaltC's Rule of thumb: Do not put anything on the Internet, in any form, encrypted or otherwise, that you do not want the world to see. It doesn't matter whose encryption you use, it can be broken. Period. Have no thought to the contrary.
As one savvy user has pointed out, none of these companies can say no to law enforcement, ultimately. However, and this has to be stressed, you can bet your sweet bippy that all of these companies will insist that law-enforcement make an exceptionally compelling case to them as to why they should break encryption in a specific case. Simply saying: "Break this encryption" is wholly insufficient, as the government would be forcing a company to break its guarantees to its customers. Indeed, in the encryption fine print, you will see that the encryption is not guaranteed for illegal data--so, if you are plotting to blow up your neighbor's house because his kid broke your kid's game disk, be aware that the company is not compelled to maintain encryption in such a case...;) -
USAFRet Reply
On some systems, it IS there be default.waltc3 said:No, it's not turned on by default. I've never used it. Poor folks apparently think BitLocker is nothing you'd notice when installing or running Windows!
Generally, preinstalled systems like laptops. Especially if it comes with Win 11 S.
And it is mostly not noticeable. Log on to the system, the entire drive is unlocked. It is not something you need to interact with all the time.
Ant 'performance issue' is not seen, because you've never used that particular laptop without it.
Me buying a Surface laptop a couple of years ago, it was BL encrypted by default.
When the system is up and running, the whole drive is decrypted. The BL only comes in to play if that drive were to be removed and read attempts in some other system.
Yes, I eventually turned it OFF, but did not see any performance benefit. -
ezst036 Reply
It goes back to low-quality consumers.umeng2002_2 said:This all goes back to the absurdity of the 3rd party doctrine loophole in the Constitution.
Courts have ruled that since you shared information with someone else, it means you magically approve of anyone (the government) getting it to.
These are informed consumers, Microsoft has been this Microsoft for a long time. They didn't switch to being a new and aggressive Microsoft just yesterday. There are no excuses. -
palladin9479 Replywaltc3 said:I keep reading this on some sites, bizarrely (not here, thankfully): "BitLocker is turned on by default in every Windows installation."
It absolutely is enabled by default on Windows 10 and 11 Home edition. That is the whole point with quasi forcing the Microsoft Account requirement. The moment you put that in, the bitlocker recovery key and any TPM system keys are sent to MS and associated with said account. Just because you haven't told it to start encrypting doesn't mean it hasn't already generated the required encryption keys and enabled the service. Soon after the user logs in it will prompt them to "Secure their computer" by encrypting the drive, with the keys it previously generated. Some users click yes, others click no, I disabled the entire thing and use veracrypt instead.