Fed Recovers $30 million in Stolen Crypto Thanks to Chain Analysis
Who says crypto can't be seized?

A joint effort by the US government and blockchain firm Chainalysis has resulted in the recovery of around $30 million in stolen cryptocurrencies. The effort showcases that crypto can and will be subject to greater scrutiny and concerted investigative efforts between the government and private institutions. Advancements in blockchain analysis are key to increasing security in a field that has already seen $1.3 billion hacked away by bad actors in 2022 alone.
According to Chainalysis, 30$ million was recovered from the prominent hacking squad Lazarus, which is thought to operate with the North Korean government's blessing (the US specifically says the group acts under North Korea's Reconnaissance General Bureau). The recovered funds were part of the $625 million siphoned from popular NFT game Axie Infinity, whose Ronin sidechain was hacked earlier this year. Adjusting for the cryptocurrency price downtrend since the hack, the recovered $30 million only amounts to 12% of the stolen crypto assets.
The senior director of investigations at Chainalysis, Erin Plante, said the seizure demonstrates that "it is becoming more difficult for bad actors to successfully cash out their ill-gotten crypto gains. We have proven that with the right blockchain analysis tools, world-class investigators and compliance professionals can collaborate to stop even the most sophisticated hackers and launderers."
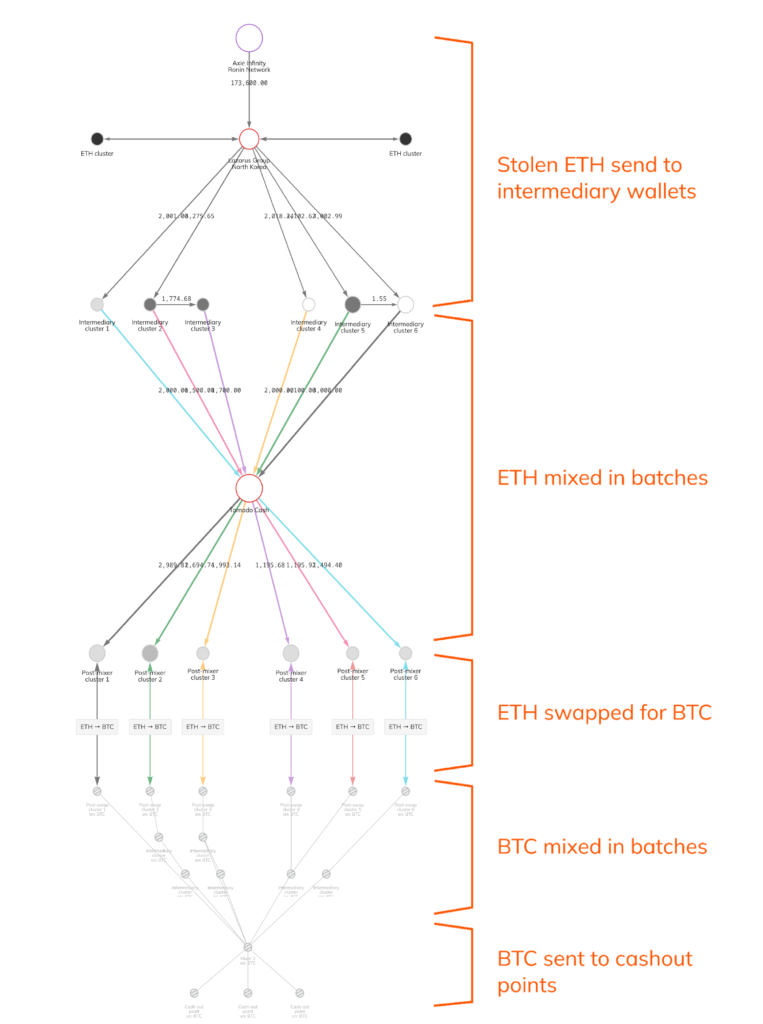
In the process, Chainalysis helped investigators read the blockchain to follow the money across several obfuscation techniques. The company said that Lazarus' money laundering scheme used more than 12,000 unique crypto addresses across several crypto assets. Cryptocurrency mixers (which aggregate funds to make them fungible, i.e., indistinguishable) such as the recently sanctioned Tornado Cash app (which resulted in the detention of one of its lead programmers, Alexey Pertsev) were also used, as were several cryptocurrency bridges that further served to obfuscate the stolen funds across multiple cryptocurrencies.
The partial recovery is, of course, less than ideal. But even so, the increasing numbers of government and law enforcement cryptocurrency and NFT seizures show that even decentralized technologies are subject to centralized choke points. This is where checks and balances can be put into effect.
Sky Mavis, developers of Axis Infinity and the Ronin sidechain, took to Twitter to announce the seizure, expecting the stolen funds to be returned to the treasury "after some time." The company recently partnered with Google Cloud as a validator node for its Ronin sidechain, with Google becoming an independent enterprise validator for Ronin in a node pool. The firm will take on the role of monitoring validator uptimes and contribute to the collective security of the network. It's an interesting take — Sky Mavis thus takes advantage of Google's cybersecurity expertise, adding a (hopefully) incorruptible node to its relatively limited pool of validators, which was the principal reason why the initial attack ever took place.
Important update regarding the Ronin incident. 30 M USD of crypto has been recovered. The current total value of the stolen funds is ~250 M. So this is ~12% of the total amount.It will take some time for these funds to be returned to the Treasury.https://t.co/Q7cLUsgYskSeptember 8, 2022
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Francisco Pires is a freelance news writer for Tom's Hardware with a soft side for quantum computing.
