Microsoft's April patch puts Windows domain controllers into reboot loops — third known issue from KB5082063 is affecting Windows Server 2016 through 2025
Microsoft has confirmed the issue
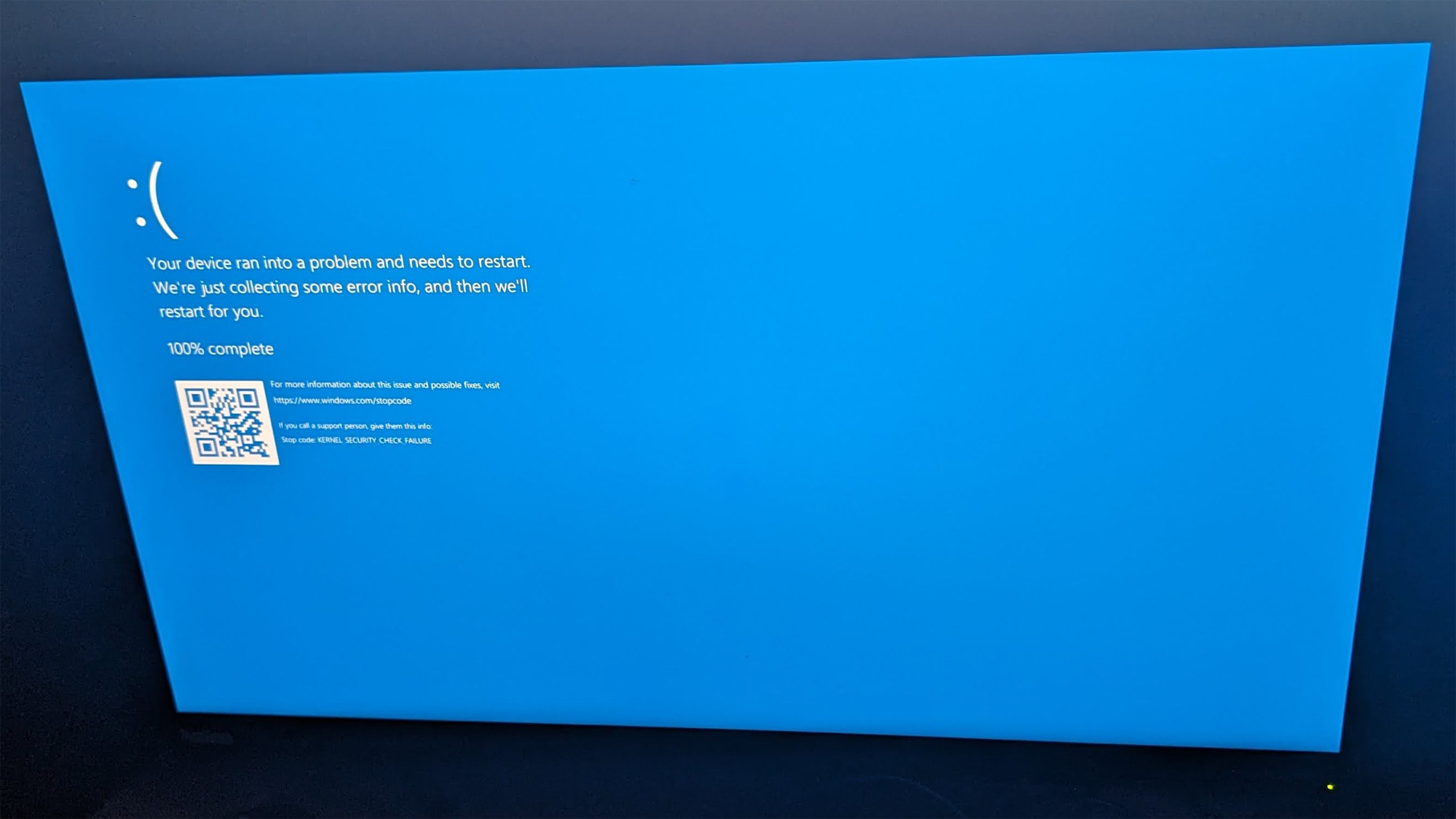
Installing this month's Windows Server security update has knocked some enterprise domain controllers into continuous reboot cycles, Microsoft confirmed in a release health dashboard entry.
The company says the April 2026 patch, KB5082063, triggers crashes in the Local Security Authority Subsystem Service (LSASS) on non-Global Catalog domain controllers used in Privileged Access Management (PAM) deployments, leaving Active Directory authentication and directory services unavailable on affected servers.
Microsoft's dashboard lists Windows Server 2016, 2019, 2022, 23H2, and 2025 as vulnerable to the fault, with the LSASS crash occurring during the startup sequence, which is what turns the failure into a loop: each automatic reboot re-enters the same faulty authentication codepath rather than recovering into a stable state.
The problem is only affecting managed enterprise environments that run PAM for Active Directory privilege delegation, and Microsoft said personal devices outside IT-managed domains aren’t exposed. The company hasn’t yet published a patch and has instead directed affected administrators to Microsoft Support for Business for mitigation guidance that can be applied if KB5082063 is already deployed.
KB5082063 now has three acknowledged bugs within a week of release, and Microsoft has warned separately that the same update prompts some Windows Server 2025 machines for a BitLocker recovery key after installation. The company is investigating reports that KB5082063 fails to install entirely on a subset of Windows Server 2025 systems.
April security updates have disrupted Windows Server domain controllers for three consecutive years. In March 2024, Microsoft shipped an emergency out-of-band fix after that month's Patch Tuesday caused DC crashes outright. The April 2024 patch cycle then broke NTLM auth across Windows Servers and forced unplanned DC restarts, which Microsoft corrected in a May 2024 rollout.
In June last year, the company released another correction for Active Directory authentication problems introduced by the April 2025 security update. This month's LSASS crash follows the same MO for the third year running: a general Patch release followed by post-deployment failure reports from enterprise admins, and a scramble for mitigation while the fix is prepared.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
With KB5082063 still on the release channel and no patch date published, admins have three choices: delay the April update, isolate a test DC to validate patch behavior before wider rollout, or escalate through the Microsoft Support form Business to obtain the mitigation steps the company is providing case-by-case.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.

Luke James is a freelance writer and journalist. Although his background is in legal, he has a personal interest in all things tech, especially hardware and microelectronics, and anything regulatory.
-
das_stig This must be one of those high quality and tested patches, Microsoft promised us with such big fanfare, yet business as usual from the coding bots at Micromuppets !Reply -
thesyndrome https://www.tomshardware.com/tech-industry/artificial-intelligence/microsofts-ceo-reveals-that-ai-writes-up-to-30-percent-of-its-code-some-projects-may-have-all-of-its-code-written-by-aiReply
I love reposting this whenever the opportunity arises....which is ALARMINGLY often now -
ezst036 Where this is going to hurt most is the smallest small businesses just slightly big enough to have some server needs. Microsoft Server is generally effectively dead but it lives on in quarters that don't get measured by statistics at many small businesses and governments These orgs don't yet have Linux talent in their employee pools and they don't have the financial resources to overcome the hurdle of fully setting up their own server from scratch and doing widespread migrations. No knowledge, no money. So they are stuck on Legacy Microsoft junk like MS Server 2026.Reply
Microsoft makes it super easy and super cheap to sign a deal with the devil and get hooked on to that fentanyl.
We all know how it is. Once you're a drug addict, breaking the habit and getting the needle out of your arm aint easy. Microsoft is well known for creating pitfalls within Windows(which includes Server) that once you're in the pit it is impossible to simply leave. It is a pit with deep, deep hooks into your skin. -
ezst036 Reply
It seems like looking at the Microsoft Dashboard as of this time to affect many versions.jp7189 said:2063 only applies to 2025. Why does the headline say 2016-2025 are affected?
https://learn.microsoft.com/en-us/windows/release-health/status-windows-server-2025
If I am reading it flawed(?), but it appears to affect many versions.
StatusOriginating updateHistoryConfirmedOS Build 26100.32690
KB50820632026-04-14Last updated: 2026-04-16, 18:50 PT
Opened: 2026-04-16, 18:50 PT
Affected versions:
Client: None
Server: Windows Server 2025; Windows Server 2022; Windows Server, version 23H2; Windows Server 2019; Windows Server 2016 -
MosephV Reply
Each OS version gets a unique KB article ID for their monthly updates . The problem highlighted in this article exists in all of them.jp7189 said:2063 only applies to 2025. Why does the headline say 2016-2025 are affected? -
MosephV Reply
Yeah. Each OS gets it's own KB article ID for the monthly updates as some aspects of each monthly update are unique to specific versions, while other parts are shared across all versions. The problem highlighted in this article exists in all of them.ezst036 said:It seems like looking at the Microsoft Dashboard as of this time to affect many versions.
https://learn.microsoft.com/en-us/windows/release-health/status-windows-server-2025
If I am reading it flawed(?), but it appears to affect many versions.
Edit: Sorry for pretty much repeating myself across two posts in a row.
