Cloudflare Access Provides BeyondCorp-Like Security To Any Company
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Cloudflare announced a new service, which provides a level of "perimeter-less" security typically only Google’s “BeyondCorp” enterprise network security architecture can provide, called Cloudflare Access.
What Is BeyondCorp?
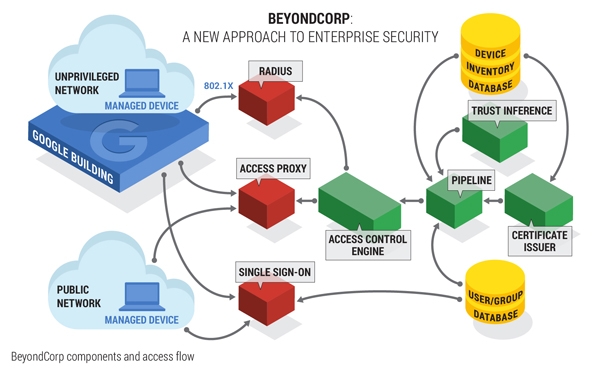
The BeyondCorp network security architecture was invented by Google post-Snowden revelations, when the company learned that the NSA may have had access to all of its “secure” internal network for years. This prompted Google to make a radical change in how it thinks about network security.
Most companies adopt a network security model where they consider everything inside the network safe and everything outside unsafe. What that means is that they use firewalls and VPNs to protect themselves from outside threats. However, the security between each system in their network is usually much weaker, because increased security often tends to come with complex set-ups, as well as training and higher maintenance costs.
Article continues belowAs we’ve seen in the past few years, major data breaches exposing tens of millions, hundreds of millions, or even billions of users seem to occur increasingly more often. This could be a sign that the typical enterprise network security model isn’t working too well.
If most companies think of their internal network as a “fortress,” where once breached by the enemy all bets are off, Google’s BeyondCorp turns every device into a fortress instead. This model has the advantage of having a “zero trust network” that can be accessed from anywhere in the world, because every device is considered to not be secure.
Therefore, users are only given the least amount of privileges in order to perform their jobs. What this ultimately means is that first off, attacks would have to breach the systems one by one, and second, the damage the attackers could do would be limited.
Cloudflare Access
Although Google has released details of its model to the public, implementing it may not be the easiest job. Cloudflare access, like Duo Security before it, is now offering a third-party BeyondCorp-like solution that companies can use to secure their enterprise applications.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
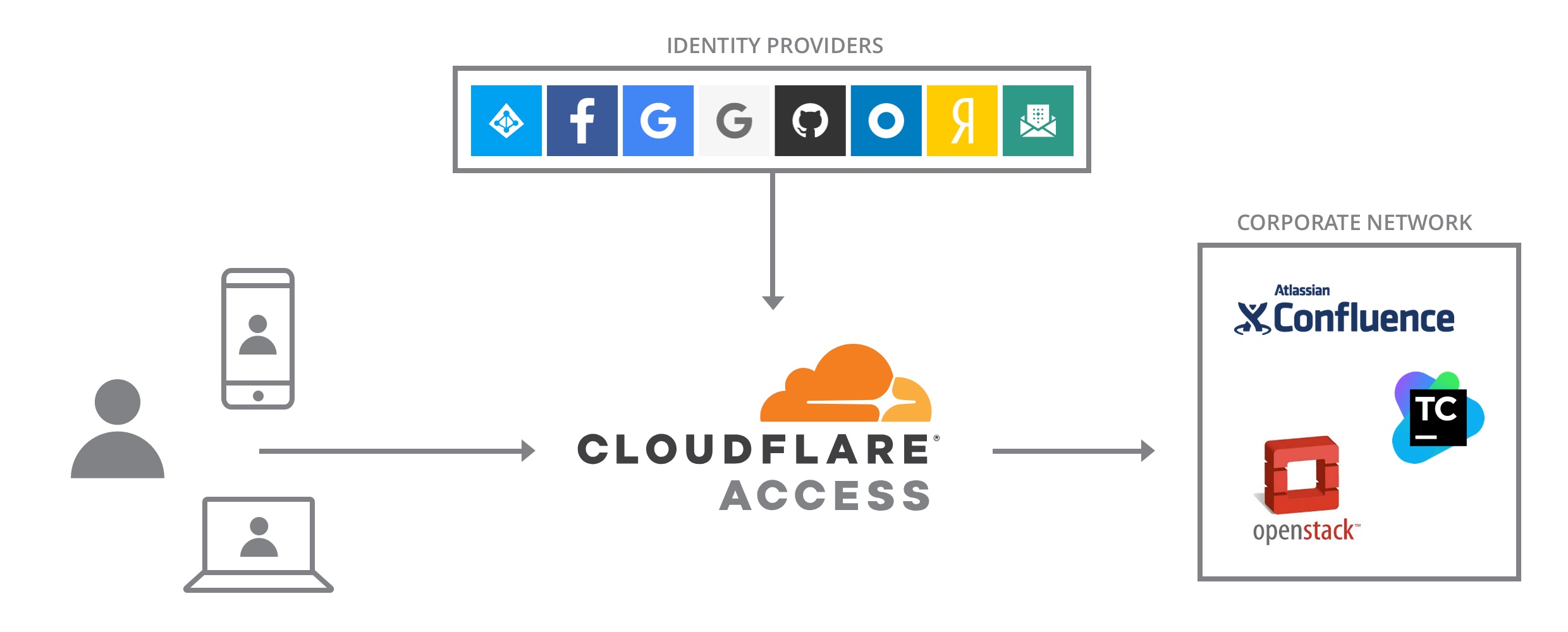
This solution, called Cloudflare Access, offers authentication through major identity providers such as Google, Azure Active Directory, and Okta, so companies can connect to Cloudflare using their existing identity providers.
The customer companies will also be able to authenticate their users via a unique TLS certificate, which means nobody who doesn’t have that certificate will be able to connect to Cloudflare Access-enabled devices. After the certificate verification is done, users will also need to authenticate with their credentials for a given enterprise application.
Further authorization restrictions can be set-up, so for instance, nobody besides the company’s employees could access project management tools or their its website’s content management system.
According to Cloudflare, there’s no need to use a VPN anymore, because all Cloudflare connections happen over HTTPS. This should improve security, performance, and productivity as employees don’t have to log in over slow connections.
IT administrators will also be able to:
Easily change access policiesModify session durationsRevoke existing user sessionsCentralized logging for audit and change logs
Cloudflare also noted that Access could be used in combination with its other latency-reducing and security-increasing services. The company also said that set-up can take minutes and is free to try for a single user and then $3 per seat per month, with bulk discounts also available for larger customers.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
bigpinkdragon286 Except of course if the CEO of Cloudflare wakes up and decides to make another "dangerous" and "arbitrary decision" and get his company out of the way so your site can be illegally taken down.Reply