Intel Releases 16 Security Advisories Covering 41 Vulnerabilities in CPUs, NUCs, SSDs
Thankfully there are patches to download for most issues.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Intel has released 16 new security advisories, which address 41 vulnerabilities. The advisories, some with 'high' severity ratings, appear to cover the full gamut of Intel catalog, including processors, devices, firmware, drivers and software. For example, several generations of Core processors and enterprise (Xeon) chips have newly disclosed vulnerabilities on the processor side. Then there are flaws and vulnerabilities in products like Optane SSD firmware, NUC firmware, Linux Kernel drivers, and the XTU tuning software.
The Intel Processor advisory has been given the CVEID of CVE-2022-21151. It is described in summary as "a potential security vulnerability in some Intel Processors may allow information disclosure." It is 'only' a medium severity rating vulnerability. We think this is because it requires an authenticated user with local access to exploit the chance to "potentially enable information disclosure" from the processor.
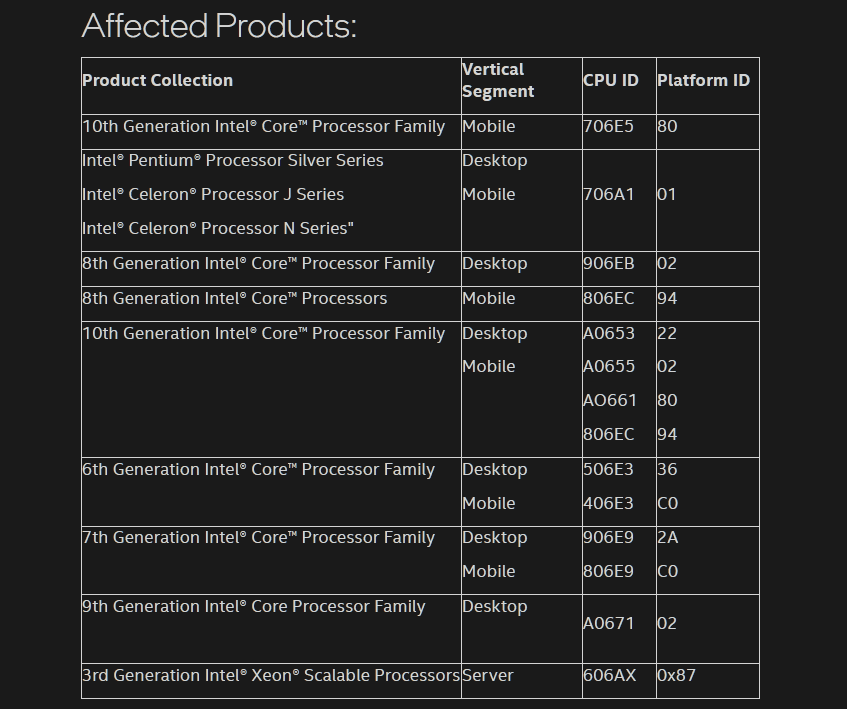
Affected processors are shown in the above table, and you could sum it up by saying that it spans the Skylake to Coffee Lake generations.
Article continues belowThough the exploitation of CVE-2022-21151 by a threat actor may sound unlikely, Intel has released a microcode update for those who feel it might be worth patching. Linux users can grab a microcode update from GitHub. Meanwhile, Windows users are advised to check Windows Update and motherboard/system makers for updated firmware.
We looked through the numerous other security advisories just published and thought it was worth highlighting that there are three Intel NUC vulnerabilities classed as high risk. They all "potentially enable escalation of privilege via local access." Intel has thankfully provided BIOS downloads for all the affected NUC products.
In its Optane SSD firmware advisory, Intel describes several high severity vulnerabilities which "may allow escalation of privilege, denial of service or information disclosure." If you have any Optane memory or SSDs, please check the link, where you will find a link to download updates to address these vulnerabilities.
Other vulnerabilities classed as high severity are detailed by the Intel Boot Guard and Intel TXT Advisory (Escalation of Privilege), the BIOS Advisory (Escalation of Privilege), and an Intel In-Band Manageability Advisory (Escalation of Privilege).
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Mark Tyson is a news editor at Tom's Hardware. He enjoys covering the full breadth of PC tech; from business and semiconductor design to products approaching the edge of reason.