Protect Your Data With Encryption
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
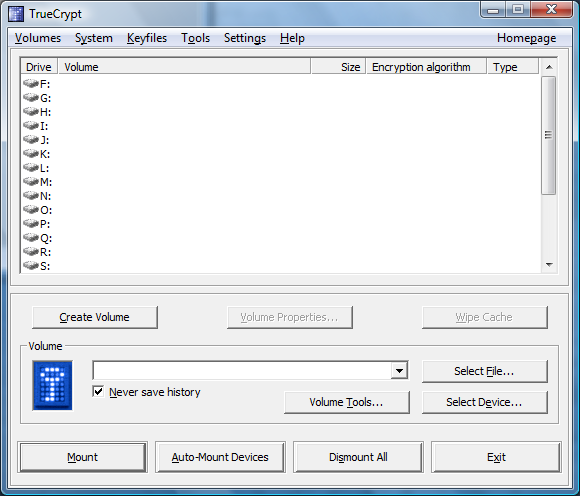
TrueCrypt 6.1 Features And Testing Considerations
TrueCrypt is available at http://www.truecrypt.org; despite the fact that I talked about Windows in the introduction, it is also available for Mac OS X and Linux. The latest stable version is 6.1a, which introduces various bug fixes and security enhancements. We used version 6.1 for this review, which has the following main features:
- Creation of an encrypted container, which can be mounted as a real drive.
- Encryption of an entire partition, such as one on a hard drive or a USB thumb drive.
- On-the-fly encryption of a Windows installation with pre-boot authentication (this is what we used for this review).
- Support for hidden volumes and unidentifiable volumes (data appears as random).
- Support of various encryption algorithms and nested double encryption.
Performance:
- Automatic, real-time and transparent encryption
- Multi-threaded design scales well on multi-core processors
TrueCrypt Testing On A Notebook
One of the editors of the German Tom’s Hardware site looked at TrueCrypt 5 in 2007, and found it to be a powerful tool back then. However, this time we decided to do more testing, as we wanted to know how well the real-time system encryption works in real life, and to check the impact on system performance and battery runtime on a modern notebook. Obviously, system encryption makes perfect sense on notebooks, laptops and probably even on nettops, although their performance might not be sufficient to allow truly transparent real-time encryption.
Data Can Be More Valuable Than Hardware
While people consider notebooks to be very valuable equipment, they don’t think about the implications of notebook theft until it’s too late. Businesses, especially, should consider that the data stored on notebooks is almost certainly more valuable than the hardware, which can be replaced quickly. A Windows password or encrypted zip files won’t do the trick, as thieves will typically have access to most data once they access the notebook hard drive on another system. TrueCrypt, though, can add a really strong layer of security as long as you pick a solid password—20 characters or more are recommended, to be on the safe side. TrueCrypt also supports tokens and smart cards if you prefer this option.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: TrueCrypt 6.1 Features And Testing Considerations
Prev Page TrueCrypt 6.1--Tried And Tested Next Page Commencing Encryption For A Windows System