Protect Your Data With Encryption

TrueCrypt 6.1--Tried And Tested
Data security is a sensitive topic. The increasing number of operating system features and Web services introduces more options for accessing, modifying—and losing—data. Yet, many people don’t really have a true security plan in place for protecting their data.
What would you think if an unauthorized person gained access to your personal files? Would someone be able to find information that is meant for your eyes only? Would they be able to do harm? I’d guess that they probably could—at least, that’s the case with <i>my</i> personal files. Whether data is personal or business related, important files have to be secured, and that brings us to a potentially incredible solution: TrueCrypt.
Ways In
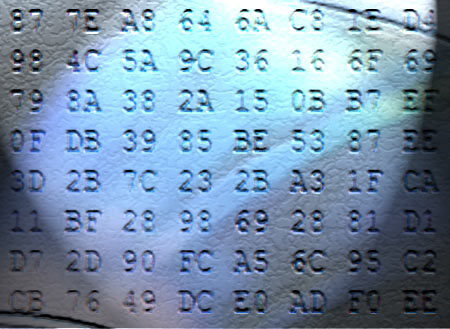
Most systems are not secure, even though known “security” measures such as Windows passwords, ZIP file passwords, BIOS passwords and FTP/Web passwords imply security. The truth is that everything that is handled or stored in plain text—which is the case for most of the examples above—can be bypassed. Windows passwords are stored in the system memory and only provide security as long as other ways of access, via network or USB, aren’t available. ZIP files can be accessed with some patience using brute-force attacks, and many Web services don’t use any encryption at all when handling login data. True security is only possible if data and transfers are protected with modern encryption algorithms using solid passwords.
Convenient Security
When I think about security products, I recall features such as the Trusted Platform Module on motherboards to validate systems, software, or users. There are components with integrated acceleration for encryption and decryption workloads; VIA’s Nano processor is a recent example. And then there are components that even come with built-in encryption: self-encrypting hard drives are popular, and Windows Vista supports Bit Locker when you purchase the expensive Ultimate or Enterprise editions.
However, most solutions come with a catch. They either require you to purchase software or hardware, or you have to change the way you work on your system(s). In addition, not all security solutions are truly secure, as there are sometimes ways around security features, which compromise your data. External hard drives with built-in encryption sometimes have intended or unintended backdoors; other examples are mentioned above.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Why Test TrueCrypt?
TrueCrypt has been around as an OpenSource encryption tool for a few years. Its main application was the creation of so-called encrypted containers to store files in a secure manner. Containers can even be mounted as Windows drives in recent versions of the tool. With the introduction of TrueCrypt 6.0, the tool was given the ability to encrypt an existing Windows installation on the fly, which means adding the extra layer of security by encrypting the entire system drive or partition. In our tests, this worked really well. In fact, our positive experience was the impetus to write this article—we found subjectively that TrueCrypt wouldn’t even slow down your system despite real-time encryption and decryption of your entire system instance and data.
Current page: TrueCrypt 6.1--Tried And Tested
Next Page TrueCrypt 6.1 Features And Testing Considerations