I Got Lost For Hours In 'Darknet' For PSVR: Hands On
Darknet is not the type of VR game I would expect to hold my attention. When I imagine a great VR game, I usually envision a first-person game that makes me feel like I’m somewhere other than my living room. To me, virtual reality is about transporting me to a new place. I want to walk on the surface of Mars, and pilot a space ship, and shoot zombies in the face, and throw slushies at my customers. Darknet is none of those things, and yet I find myself drawn to its simple but challenging gameplay.
Hack The Mainframe
In Darknet, you become an elite hacker-for-hire with the tools needed to steal data from “the world’s most secure networks.” Your goody bag includes viruses, hydras, exploits, and worms, which help you get past the strongest security systems around. You must poke and prod at the target network to find vulnerabilities and take down the security measures one by one so that you can retrieve sensitive data and collect a bounty.
Of course, hacking in Darknet doesn’t resemble the real thing in any way, but don’t let the video game hacking trope scare you off; Darknet is a surprisingly fun puzzle game.
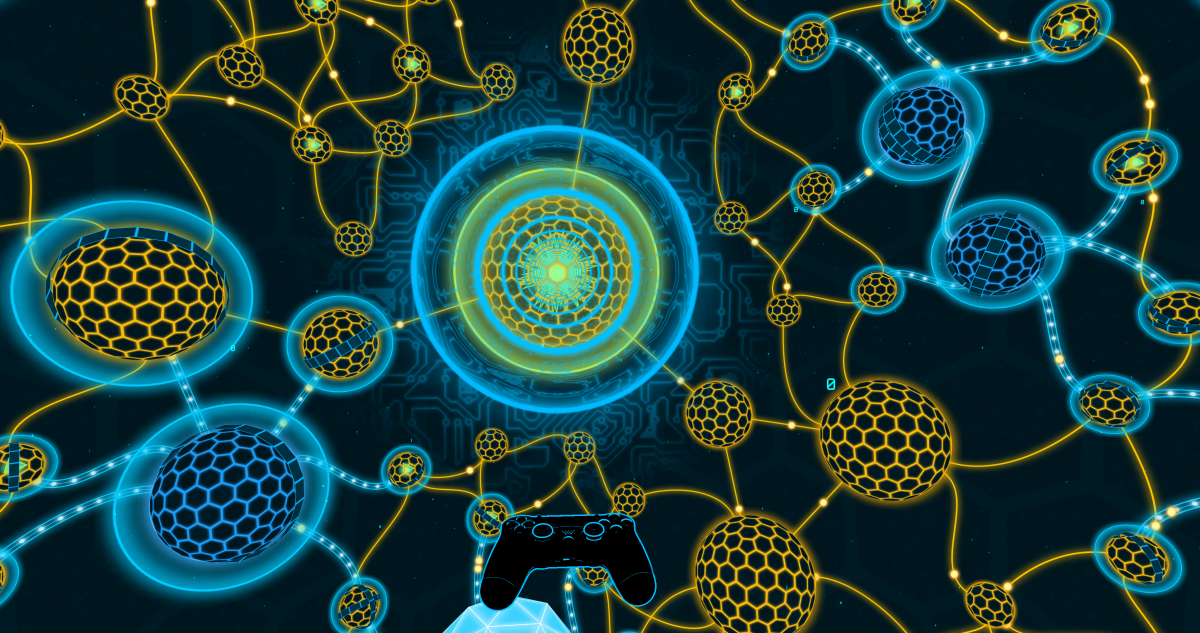
Darknet starts off with an easy to understand tutorial puzzle to get you familiarized with the controls and the game mechanics. The first tool you learn to use is the basic virus, which lets you take control of vulnerable nodes (represented as spheres on the map). When you deploy a virus to your target, the view zooms in to show a puzzle that you must solve so that you get control of the node’s core.
Each puzzle features a variety of blue hexagons that represent antivirus software, which is there to stop you from reaching the yellow core and taking control of the node. Antivirus software stops your viruses, but your viruses also knock out the antivirus programs. With enough viruses and a strategic delivery plan, you can reach the core of any node.
Node puzzles vary in difficulty. Some nodes are unprotected and can be cracked with a single virus; others are protected by shields and firewalls, which increase the difficulty and lower your chances of success. The difficulty of the puzzles increases in relation to the size of the node, too. Larger nodes have more complex puzzle structures with more antivirus applications than smaller nodes.
Uncontrolled nodes are usually orange, but you’ll notice that some of the larger nodes are blue instead. The large blue nodes are called Sentinels, and they provide additional protection for adjacent nodes. Sentinels power the shield and firewall layers on neighboring nodes. If you take control of a Sentinel, you also deplete the protections it provides to other nodes.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Spread The Infection
Once you have control of a node, you can use it as a jumping off point to launch the other attacks on the network. Hydras are the second class of cyber-weapon that you get access to. When you deploy a hydra into the network, it seeks and infects any adjacent unprotected node and continues to spread until a node with a shield stops it in its tracks. The third class of attack is called an exploit, and those are used to weaken the firewall protection of the network. You can use exploits to launch a directed attack towards a Sentinel node to remove one of its firewall layers. Sentinels sometimes have a layer of ice on them, too, which must be removed before you can take control. The exploit attacks can remove the ice for you.
The fourth and final class of cyber-weapon at your disposal is the worm, which you can deploy from a node you control. The worm infects a nearby node and nullifies the target’s shield protection. A worm won’t necessarily infect an adjacent node, though; it could skip the adjacent node and move to the next one.
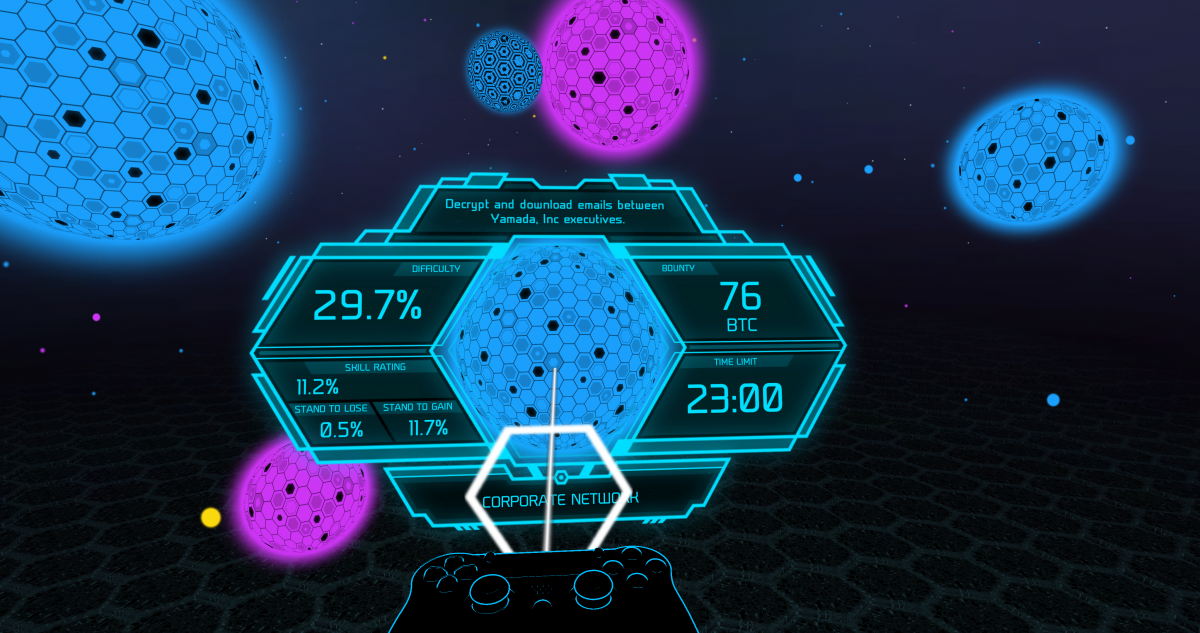
The worm attack isn’t available to you at the start of the game. You must unlock the worm after collecting a few bounties. Remember, you're a hacker-for-hire looking for a pay day. The missions you accept come with a bounty to collect once you’ve retrieved the desired data. Bounty missions pay you in BTC, which you can use to purchase upgrades. The worm upgrade will cost you 10 BTC, but it's well worth the investment. Other upgrades include faster viruses, starting funds, and access to deeper levels of the web.
BTC isn’t the only currency in the game. While you’re hacking, you’ll collect money from the nodes you control. That money doesn’t do you any good after a bounty mission is complete, but during the mission, you can use the money to purchase hacking applications. Each time you purchase a virus, hydra, exploit, or worm, the price of the next one will go up. You must continue to take control of additional nodes to help pay for more hacks so that you can gain access to more fortified targets. Fortunately, when you purchase a virus, it's yours to keep for the duration of the bounty mission. You can deploy all your viruses every time you hack a node.
The ultimate goal of any bounty mission is to reach the central root node. The root node contains the data that you’re being paid to access, and it’s heavily fortified. Expect to find several firewalls and a shield protecting the root, and an array of sentinel nodes that you must get through before you can take control of the root node.
Once you finish a bounty mission and collect your reward, there are many more missions to chose from. Some bounty offers are more lucrative than others, but the more it pays, the tougher the challenge. And some of the bounties have time limit stipulations, which adds a psychological factor to throw you off your game and make you choke.
And therein lies the beauty of Darknet. The game is simple on its surface, yet it's filled with challenges that keep you pressing on to beat the next one. I thought I was going to play Darknet for 20 minutes or so to get a feel for the game. Little did I know, three hours would pass before I gazed upon (actual) reality again.
Darknet is available on PlayStation VR for $14.99. You can also get the game on Oculus Rift and Gear VR.
Kevin Carbotte is a contributing writer for Tom's Hardware who primarily covers VR and AR hardware. He has been writing for us for more than four years.
-
bit_user I've heard of games using real bitcoin as in-game currency. Therefore, I'm annoyed that they seem to have borrowed the terminology for their fake currency.Reply
Oh well. I gave up on bitcoin over a year ago, anyhow. Nowadays, I hear it's mostly just traded by speculators in China.