Do The Meltdown and Spectre Patches Affect PC Gaming Performance? 10 CPUs Tested
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Shadow of War, Project CARS 2 & PUBG
Middle-earth: Shadow of War
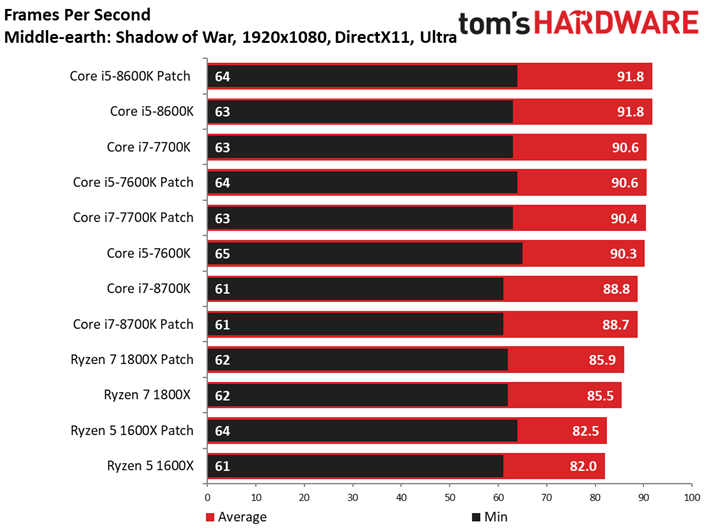
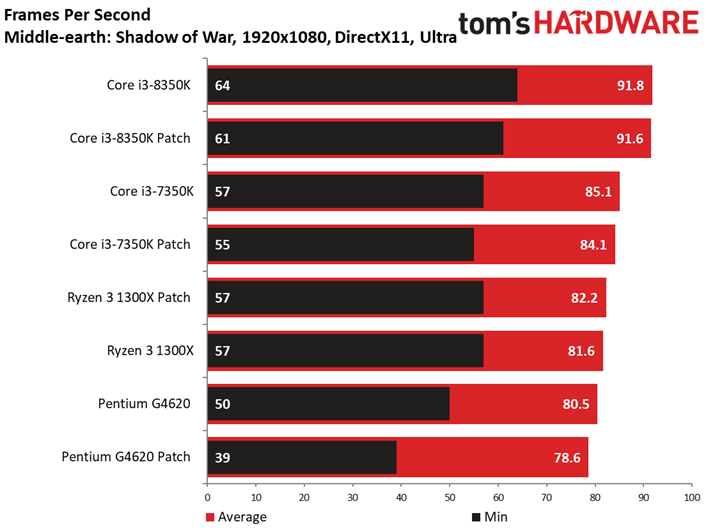
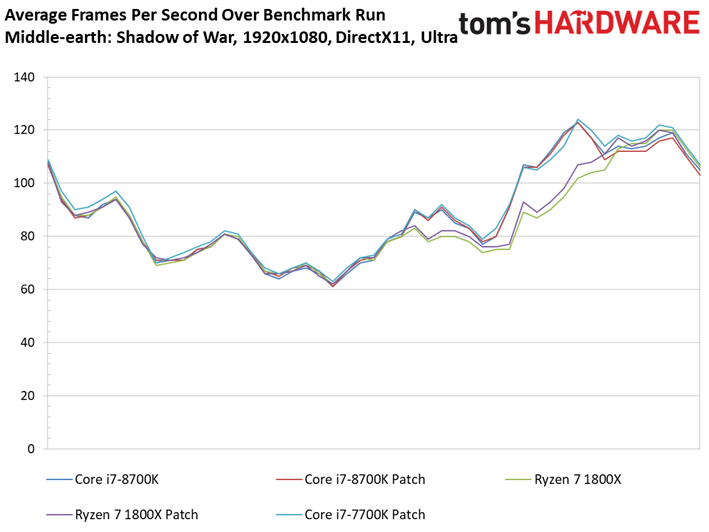
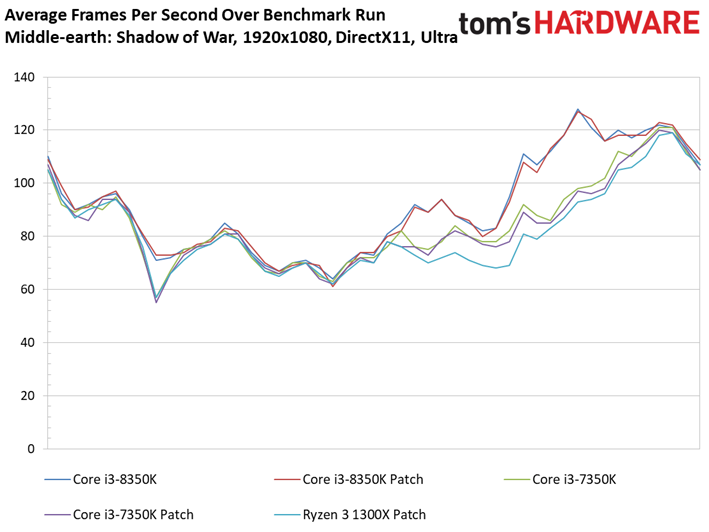
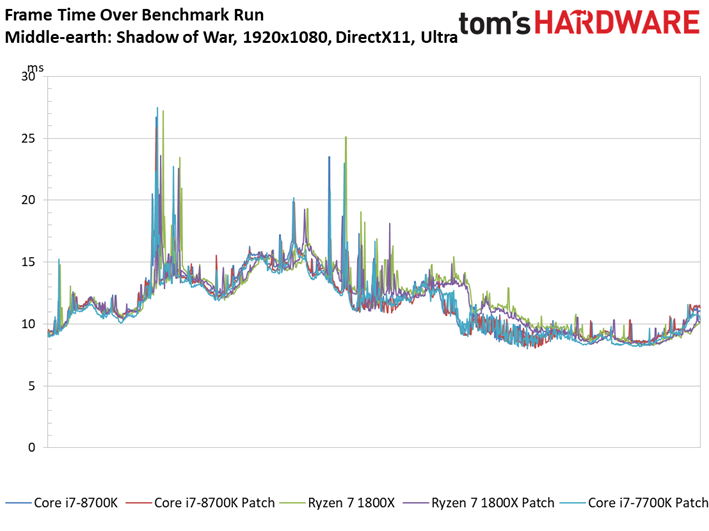
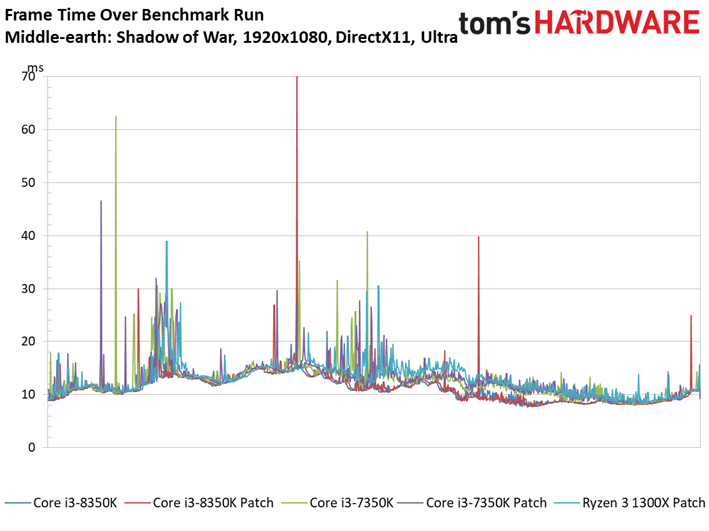
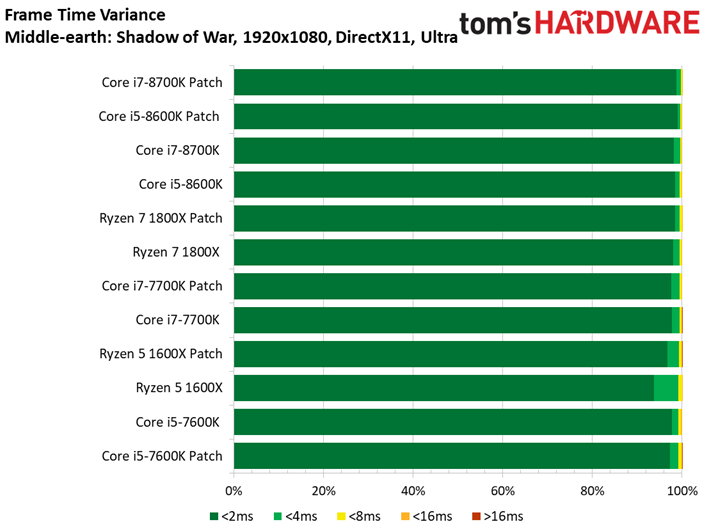
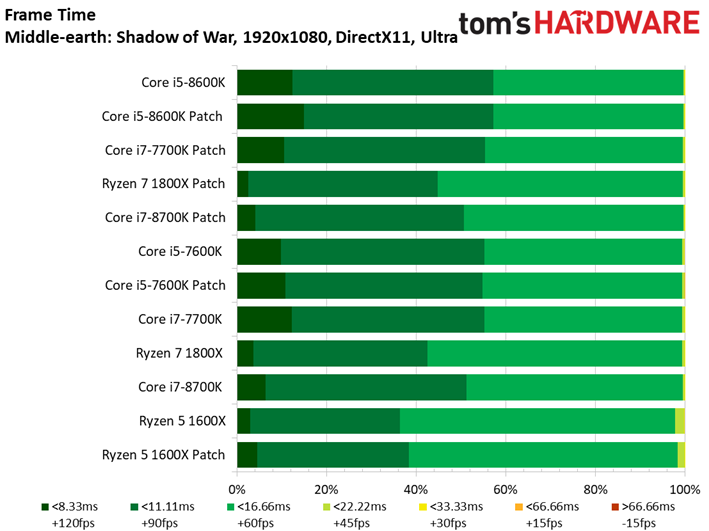
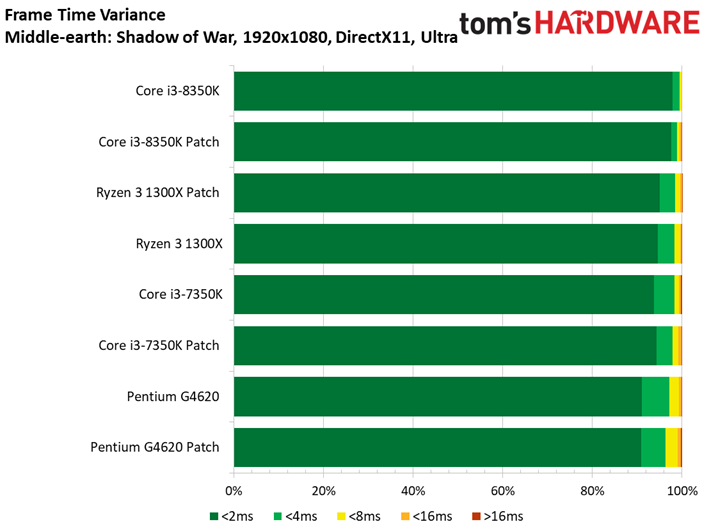
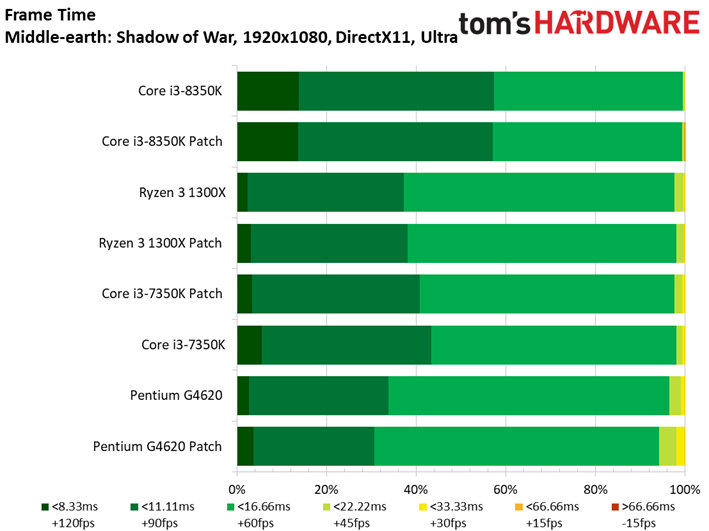
We swapped out the aging Middle-earth: Shadow of Mordor for Shadow of War during this round of tests. We like that its built-in benchmark is very consistent.
Shadow of War isn't as sensitive to clock rate and IPC throughput as its predecessor. We don't see much variance between the Core i5 and i7 models, which are largely graphics-bound. There is, however, more distance between the lower-end models. But there is only a 13.2 FPS delta between the Core i7-8600K and Pentium G4620.
Project CARS 2
We're also swapping out Project CARS for Project CARS 2.
Article continues below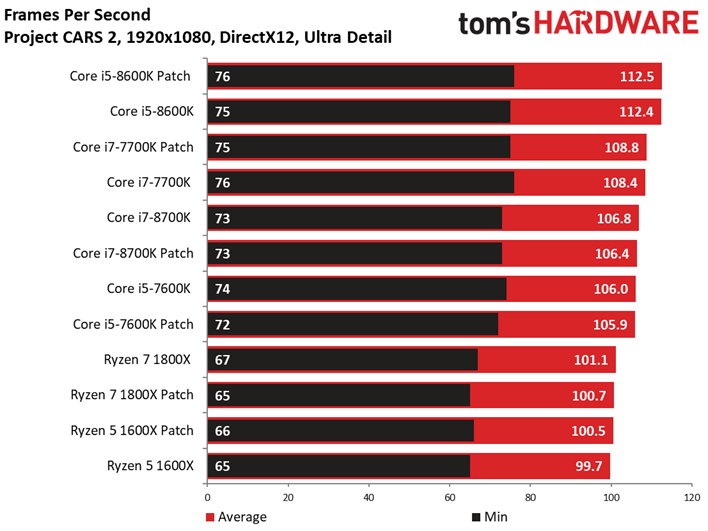
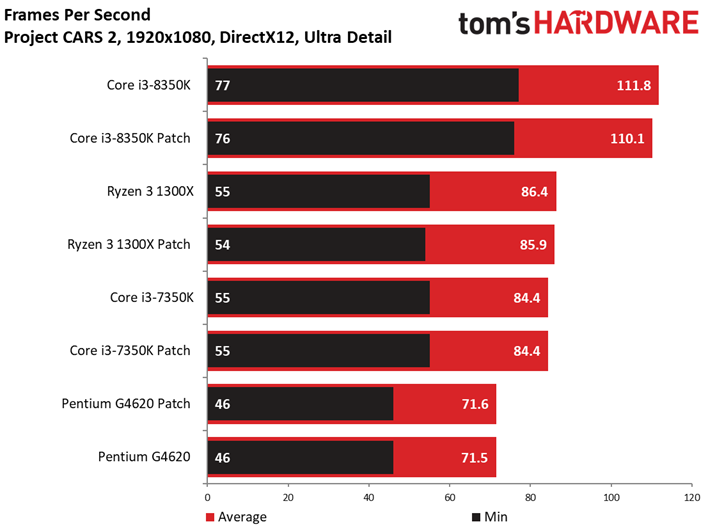
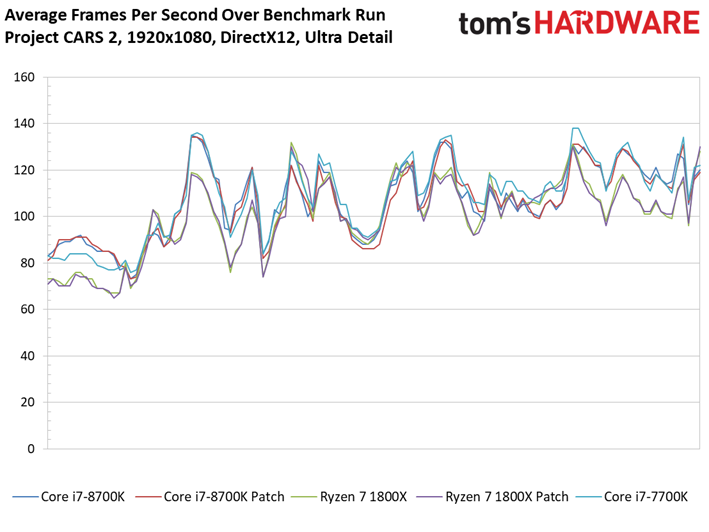
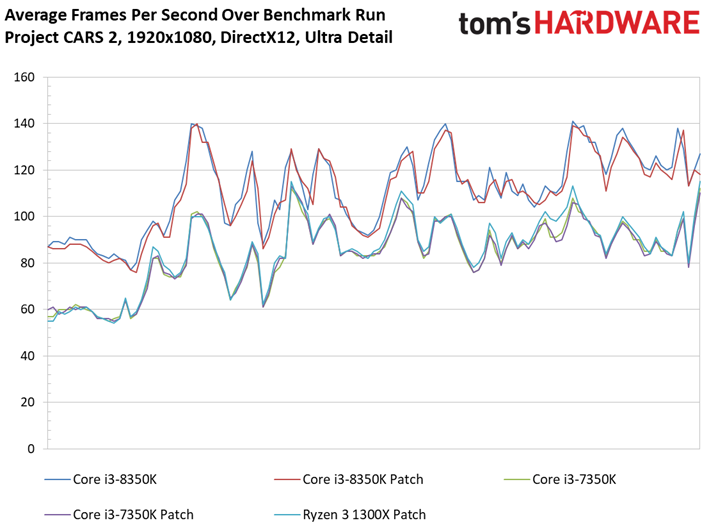
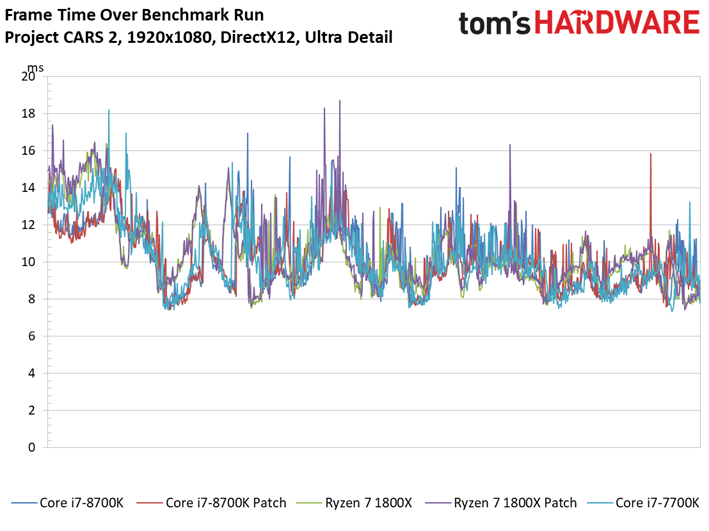
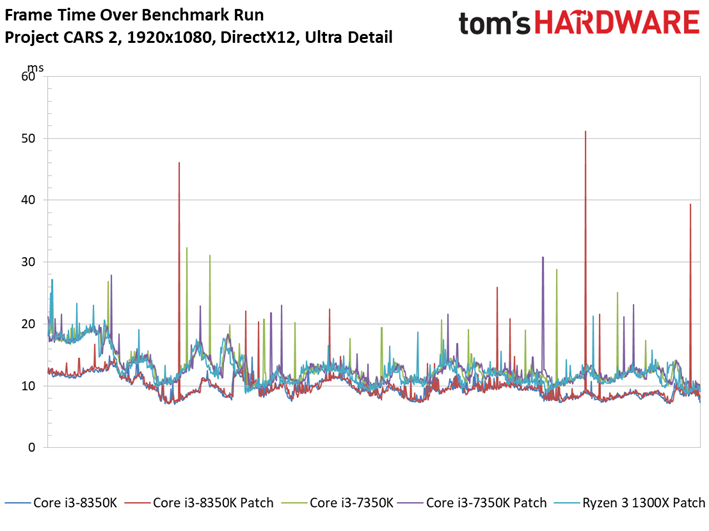
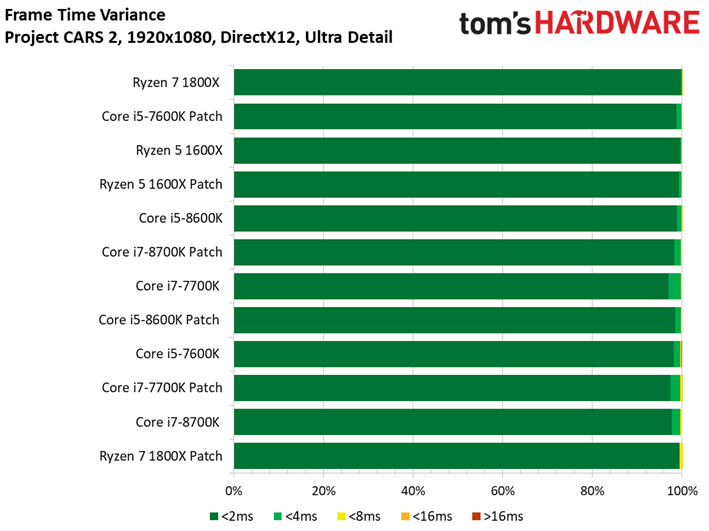
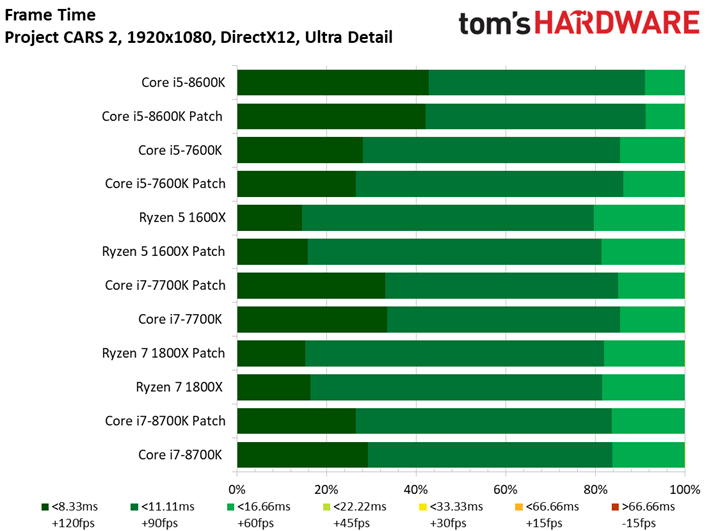
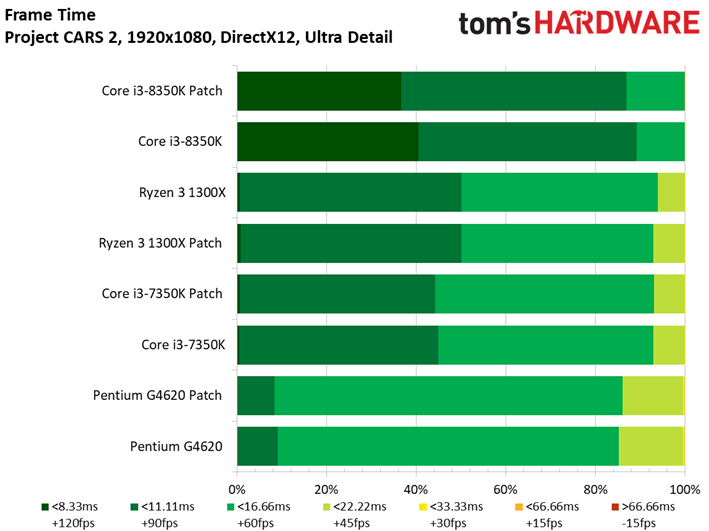
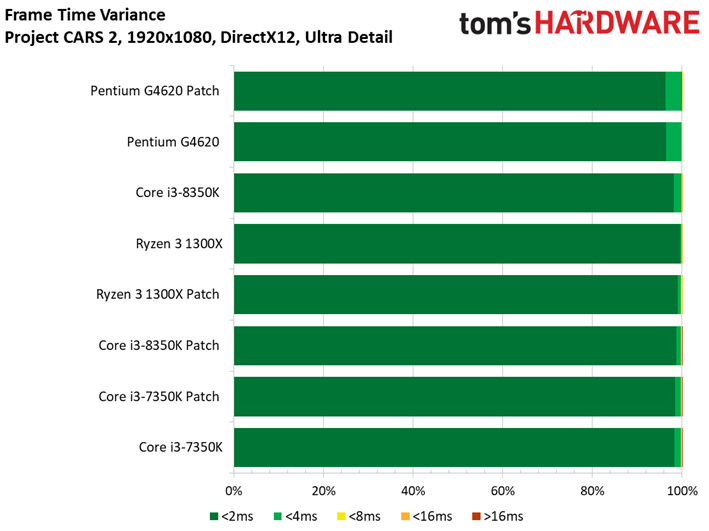
There's a bit more scaling to observe in this title, with the slowest processor lagging the leader by 41 FPS. Regardless, though, there isn't any significant variance attributable to security patches (aside from a 1.7 FPS delta between the Core i3-8350K results).
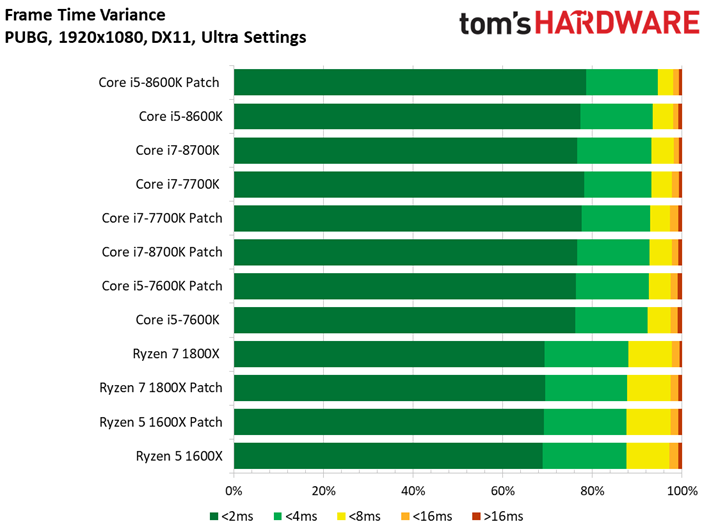
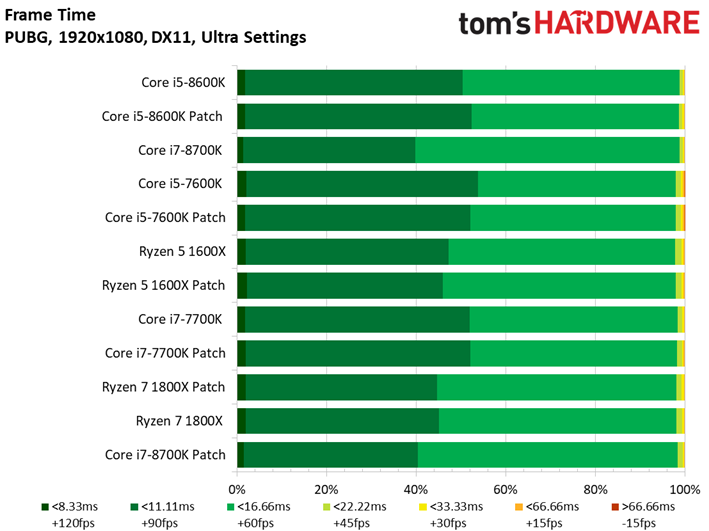
PlayerUnknown's Battlegrounds (PUBG)
This is also our first outing with PlayerUnknown's Battlegrounds.
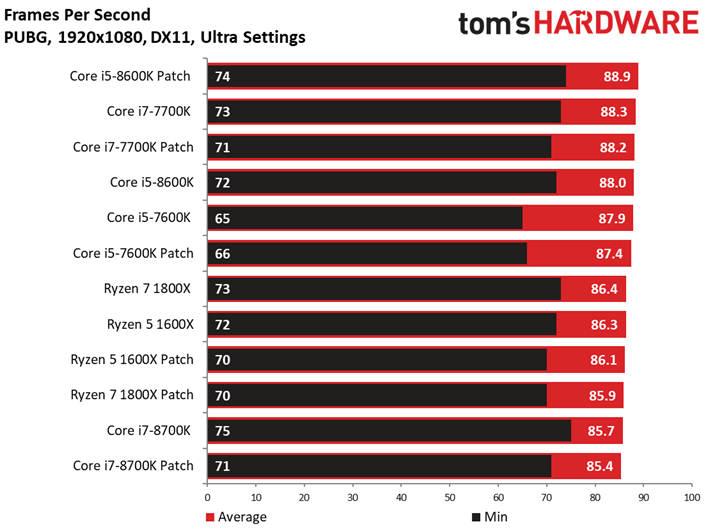
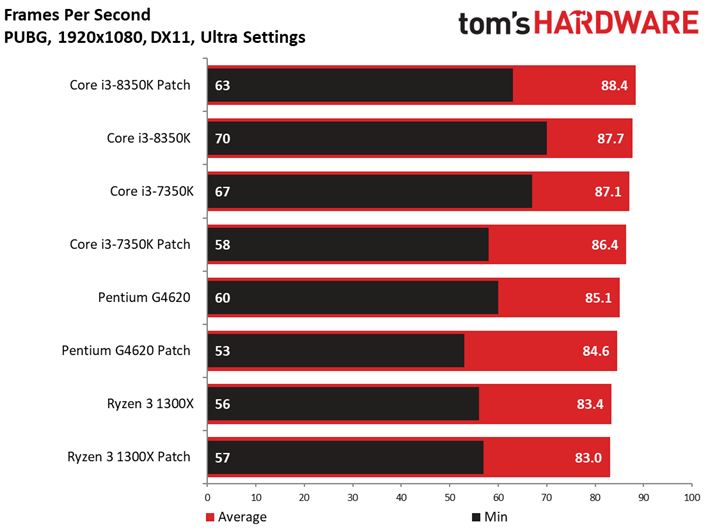
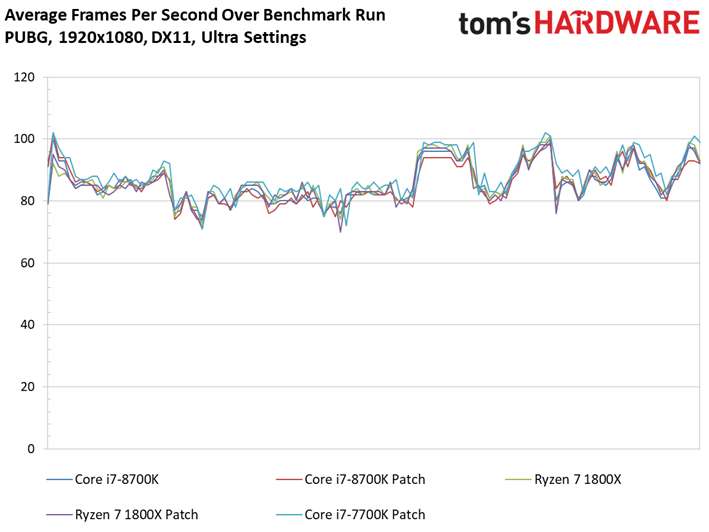
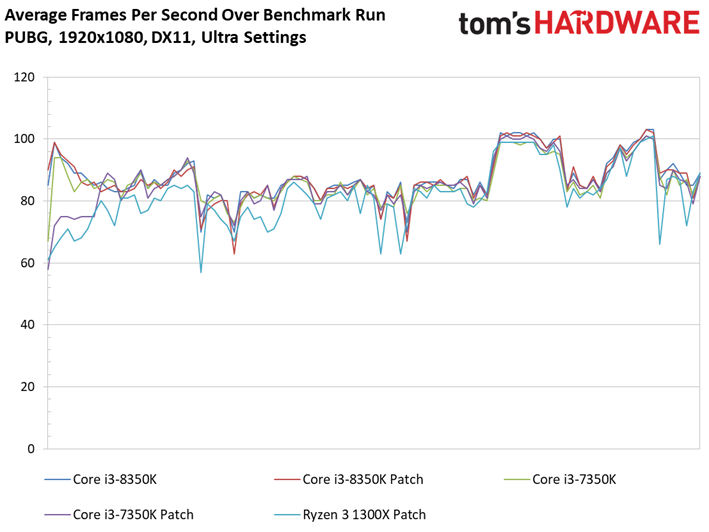
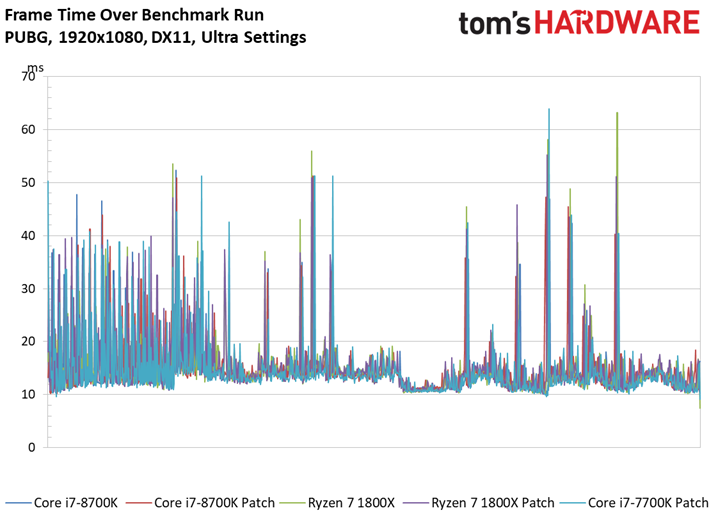
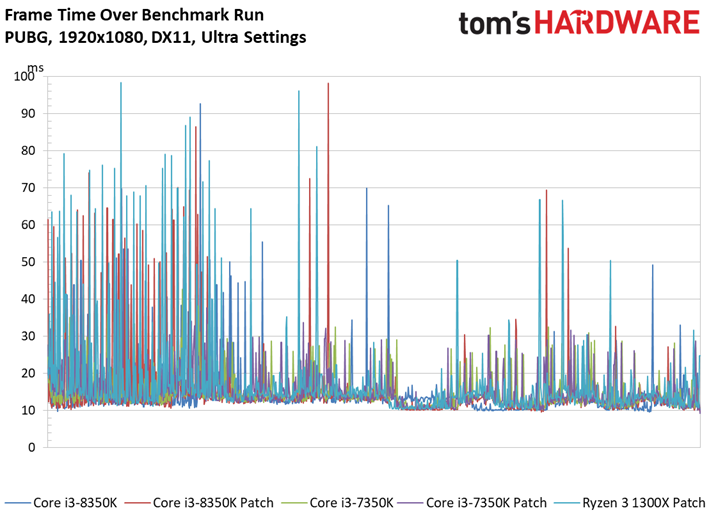
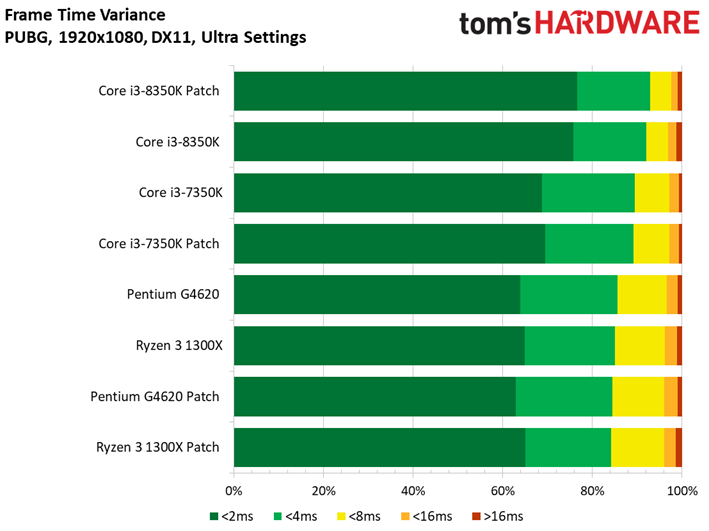
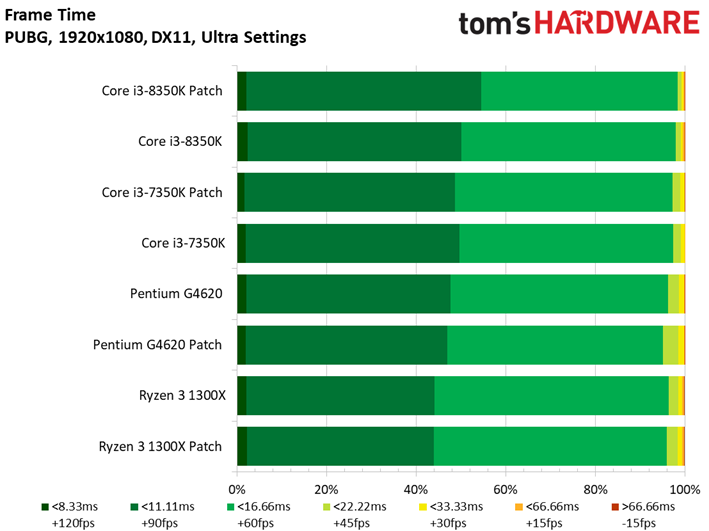
Although we're using a saved game sequence to ensure repeatability, we recently learned that PUBG recordings can lag in-game multiplayer performance by ~4-8 FPS. This is an odd tendency because recorded game sequences usually run faster than actual multiplayer matches. Nevertheless, we recorded a few sessions with our tool and then compared them to in-game results using the same path. Sure enough, the FPS line charts didn't overlap, even though the results indicate similar peaks and valleys. That means the recording is an accurate representation of trends, albeit with slower frame rates.
That doesn't mean the results are any more interesting than they have been, though. The game engine simply doesn't scale well; we only recorded a 5.9 FPS delta between the fastest and slowest processors in our test pool. We probably could amplify this difference by reducing graphics quality. However, we prefer setting the eye candy to maximum for a more enjoyable experience, rather than deliberately creating a synthetic metric.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
MORE: CPU Security Flaw: All You Need To Know About Spectre
MORE: Best Gaming CPUs
Current page: Shadow of War, Project CARS 2 & PUBG
Prev Page Far Cry Primal, Grand Theft Auto V & Hitman Next Page Game On...For Now
Paul Alcorn is the Editor-in-Chief for Tom's Hardware US. He also writes news and reviews on CPUs, storage, and enterprise hardware.
-
madvicker The majority of PC users are going to be on older CPUs than the ones you've tested. These results are only pertinent to the small % of people who have recently bought a CPU / new PC. What about the rest, the majority with older CPUs? That would be a much more useful and interesting analysis for most readers....Reply -
arielmansur Newer cpus don't get a performance penalty.. but older ones sure do get a noticeable one..Reply -
salgado18 Reply20680472 said:The majority of PC users are going to be on older CPUs than the ones you've tested. These results are only pertinent to the small % of people who have recently bought a CPU / new PC. What about the rest, the majority with older CPUs? That would be a much more useful and interesting analysis for most readers....
Last page, third paragraph:
"so it's possible that the impact on older CPUs could be minor as well (game testing on those is in-progress)." -
ddearborn007 HmmmReply
3/4 of all personal computers in the world today are NOT running windows 10. I don't know the exact percentage of gaming systems that are NOT running windows 10, but surely it is substantial.
Why wasn't the performance hit measured on the operating system running 3/4 of all PC's in the world today published immediately? To date, it appears that these numbers are being withheld from the public; the only reason has to be that the performance hit is absolutely massive in many cases.........Oh, and out of the total number of PC's used world wide, "gaming" PC's are a very small percentage, again begging the question of why tests are only being published for windows 10.... -
LORD_ORION Need to test older CPUs... or is this article designed by Intel to stop people from returning recently purchased CPUs.Reply -
RCaron Excellent article Paul!Reply
I have a question.
I read originally that AMD Zen architecture had near-immunity to Spectre variant 2 because a CPU specific code (password if you will) (that changes with each CPU) was required in order to exploit the CPU. Which is why AMD was claiming that Zen was almost immune to Spectre variant 2. Is this not the case?
AMD continues to insist that Spectre 2 is difficult to exploit due to CPU architecture. You left this out, and you continually lumped AMD with Intel with respect to Spectre 2 vulnerability.
This is misleading to your readers, and portrays a bias towards Intel.
https://www.amd.com/en/corporate/speculative-execution -
tripleX Reply20680748 said:Hmmm
3/4 of all personal computers in the world today are NOT running windows 10. I don't know the exact percentage of gaming systems that are NOT running windows 10, but surely it is substantial.
Why wasn't the performance hit measured on the operating system running 3/4 of all PC's in the world today published immediately? To date, it appears that these numbers are being withheld from the public; the only reason has to be that the performance hit is absolutely massive in many cases.........Oh, and out of the total number of PC's used world wide, "gaming" PC's are a very small percentage, again begging the question of why tests are only being published for windows 10....
Global OS penetration for Win 10 and Win 7 is effectively tied.
-
Paul Alcorn Reply20680892 said:Excellent article Paul!
I have a question.
I read originally that AMD Zen architecture had near-immunity to Spectre variant 2 because a CPU specific code (password if you will) (that changes with each CPU) was required in order to exploit the CPU. Which is why AMD was claiming that Zen was almost immune to Spectre variant 2. Is this not the case?
AMD continues to insist that Spectre 2 is difficult to exploit due to CPU architecture. You left this out, and you continually lumped AMD with Intel with respect to Spectre 2 vulnerability.
This is misleading to your readers, and portrays a bias towards Intel.
https://www.amd.com/en/corporate/speculative-execution
From the AMD page (which you linked)
Google Project Zero (GPZ) Variant 1 (Bounds Check Bypass or Spectre) is applicable to AMD processors.
And...
GPZ Variant 2 (Branch Target Injection or Spectre) is applicable to AMD processors.
While we believe that AMD’s processor architectures make it difficult to exploit Variant 2, we continue to work closely with the industry on this threat. We have defined additional steps through a combination of processor microcode updates and OS patches that we will make available to AMD customers and partners to further mitigate the threat.
AMD will make optional microcode updates available to our customers and partners for Ryzen and EPYC processors starting this week. We expect to make updates available for our previous generation products over the coming weeks. These software updates will be provided by system providers and OS vendors; please check with your supplier for the latest information on the available option for your configuration and requirements.
Linux vendors have begun to roll out OS patches for AMD systems, and we are working closely with Microsoft on the timing for distributing their patches. We are also engaging closely with the Linux community on development of “return trampoline” (Retpoline) software mitigations.
AMD hasn't released the microcode updates yet, but to its credit, it's probably better to make sure it is validated fully before release.
-
DXRick Do the OS patches (without the microcode patches) fix the two exploits? If so, why would we even want the Intel patches at all?Reply